2014-09-09 - (FILELESS INFECTION BY) ANGLER EK FROM 46.105.140[.]56 - TSEVID-SYNONYMI.JUSTDANCEATSEA[.]COM:8080
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
NOTES:
- This is the same type of fileless infection Angler EK traffic seen yestersday ( link ).
- The malware payload and post-infection traffic are similar, if not the same, in many aspects.
- For more info on this traffic, see Kafeine's blog entry at: https://malware.dontneedcoffee.com/2014/08/angler-ek-now-capable-of-fileless.html
CHAIN OF EVENTS
ASSOCIATED DOMAINS:
- 46.105.140[.]56 - tsevid-synonymi.justdanceatsea[.]com:8080 - Angler EK
- 94.126.178[.]29 - hgyudheedieibxy[.]com - Post-infection callback
- 95.141.36[.]218 - knpqxlxcwtlvgrdyhd[.]com - Post-infection callback
- 166.78.62[.]91 - hufqifjq[.]com - Post-infection callback
- 176.31.62[.]76 - itktxexjghvvxa[.]com - Post-infection callback
- 188.165.251[.]195 - qcemzrfxxqimzkxm[.]com - Post-infection callback
- 217.23.13[.]42 - nvlyffua[.]com - Post-infection callback
ANGLER EK:
- 14:46:06 UTC - tsevid-synonymi.justdanceatsea[.]com:8080 - GET /ndf4xx22ci.php
- 14:46:10 UTC - tsevid-synonymi.justdanceatsea[.]com:8080 - GET /2PDhzjcalvXNHRjbdIr_pYDT-RwxtCyNvhwWSNQG8UHziCD_2sXHdfXNVFeVxfaF
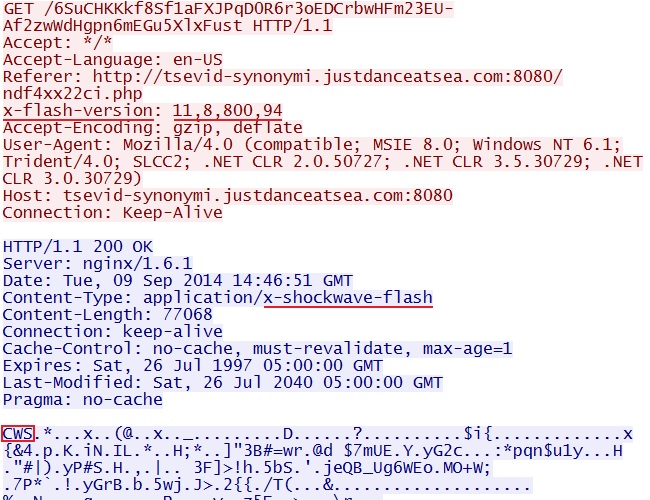
- 14:46:13 UTC - tsevid-synonymi.justdanceatsea[.]com:8080 - GET /6SuCHKKkf8Sf1aFXJPqD0R6r3oEDCrbwHFm23EU-Af2zwWdHgpn6mEGu5XlxFust
- 14:46:19 UTC - tsevid-synonymi.justdanceatsea[.]com:8080 - GET /qNhs3siJoyRLr08gTN2oi0yS2KzELEtEBHps8ABO_2TrPqlRwTrHzmsmUOn3-15Q
- 14:46:30 UTC - tsevid-synonymi.justdanceatsea[.]com:8080 - GET /NahZL2m_tDjEenoQf0wAuM3WwN1RqgWKxWS-E0rhoJMFKgt39hOhWWcUu7Vh5hK2
- 14:46:33 UTC - tsevid-synonymi.justdanceatsea[.]com:8080 - GET /sBb9d4H4_Bvq04nqS_GG1P5kPU7HhPyGSNTpTgt58amKZEG_ChEG3hfozXg7XBOP
POST-INFECTION TRAFFIC TO LEGITIMATE DOMAINS:
- 14:46:17 UTC - www.earthtools[.]org - POST /timezone/0/0
- 14:46:18 UTC - www.ecb.europa[.]eu - POST /stats/eurofxref/eurofxref-hist-90d.xml
- 14:46:25 UTC - www.download.windowsupdate[.]com - GET /msdownload/update/v3/static/trustedr/en/authrootstl.cab
- 14:46:39 UTC - www.earthtools[.]org - POST /timezone/0/0
- 14:46:40 UTC - www.ecb.europa[.]eu - POST /stats/eurofxref/eurofxref-hist-90d.xml
- 14:46:50 UTC - www.earthtools[.]org - POST /timezone/0/0
- 14:46:51 UTC - www.ecb.europa[.]eu - POST /stats/eurofxref/eurofxref-hist-90d.xml
NOTE: These appear to be checking for location (www.earthtools[.]org) and connectivity. HTTP POST requests to the European Central Bank home page (www.ecb.europa[.]eu) sent zero bytes of post data and returned XML data on exchange rates. There was also traffic to www.google[.]com, but only saw several 3-way handshakes with the connection immediately FIN-ed by the server. Examine the pcap file for more details.
POST-INFECTION TRAFFIC TO MALWARE DOMAINS:
- 14:46:23 UTC - 188.165.251[.]195:443 - encrypted traffic to: qcemzrfxxqimzkxm[.]com
- 14:46:32 UTC - 188.165.251[.]195:443 - encrypted traffic to: qcemzrfxxqimzkxm[.]com
- 14:46:42 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:46:42 UTC - 94.126.178[.]29:443 - encrypted traffic to: hgyudheedieibxy[.]com
- 14:46:42 UTC - 95.141.36[.]218:443 - encrypted traffic to: knpqxlxcwtlvgrdyhd[.]com
- 14:46:43 UTC - 166.78.62[.]91:443 - encrypted traffic to: hufqifjq[.]com
- 14:46:43 UTC - 176.31.62[.]76:443 - encrypted traffic to: itktxexjghvvxa[.]com
- 14:46:56 UTC - 188.165.251[.]195:443 - encrypted traffic to: qcemzrfxxqimzkxm[.]com
- 14:47:09 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:48:24 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:49:38 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:50:47 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:51:55 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:53:03 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
- 14:54:13 UTC - 217.23.13[.]42:443 - encrypted traffic to: nvlyffua[.]com
NOTE: Also saw numerous DGA-style domains that didn't resolve. Examine the pcap file for more details.
PRELIMINARY MALWARE ANALYSIS
FLASH EXPLOIT:
File name: 2014-09-09-Angler-EK-flash-exploit.swf
File size: 77,068
MD5 hash: 67ca9a31f220bc7b68f203c07ad668b9
Detection ratio: 1 / 55
First submission: 2014-09-08 14:58:31 UTC
VirusTotal link: https://www.virustotal.com/en/file/350836364013549b6a76aab79d57d109df6acc143759e24a952d3ff5d6a76ec4/analysis/
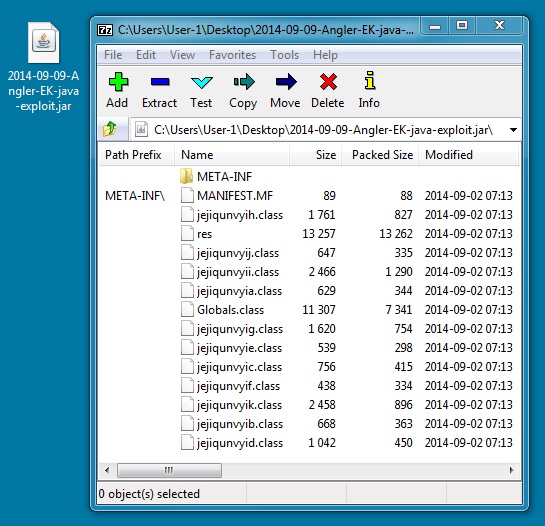
JAVA EXPLOIT:
File name: 2014-09-09-Angler-EK-java-exploit.jar
File size: 28,768
MD5 hash: b7b59e710aca39073c67cda53871111e
Detection ratio: 14 / 53
First submission: 2014-09-04 08:25:44 UTC
VirusTotal link: https://www.virustotal.com/en/file/c6a5c9154b088c1ae8ccaeb7b987ae560a5325ab389f994619c92bc71610f17b/analysis/
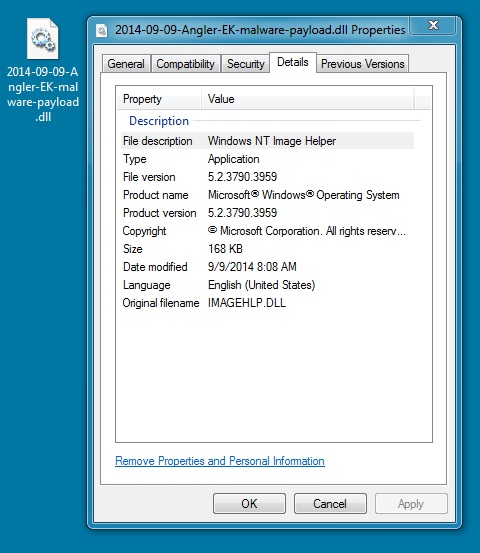
MALWARE PAYLOAD:
File name: 2014-09-09-Angler-EK-malware-payload.dll
File size: 172,912
MD5 hash: fc1e3c8bde2558636c8fc82de9bb38e9
Detection ratio: 2 / 54
First submission: 2014-09-09 15:22:03 UTC
VirusTotal link: https://www.virustotal.com/en/file/a098ef3e4d3cae52eaf32d0fe96400e91bf5cf29affa181d509d54008261e6f9/analysis/
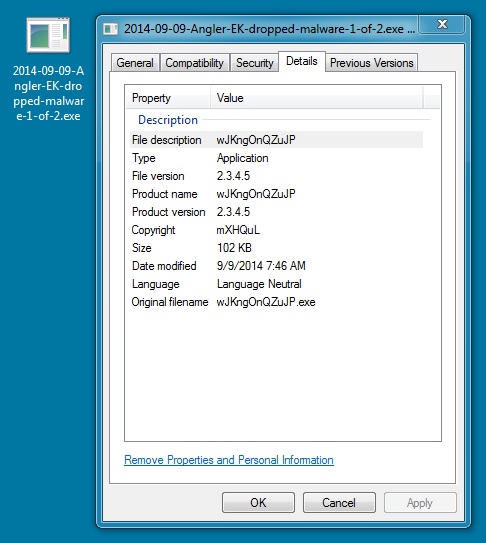
DROPPED MALWARE 1 OF 2:
File name: 2014-09-09-Angler-EK-dropped-malware-1-of-2.exe
File size: 104,448
MD5 hash: bbf0706b0591053cdedfcd5f6dfb19d6
Detection ratio: 4 / 53
First submission: 2014-09-09 15:23:09 UTC
VirusTotal link: https://www.virustotal.com/en/file/2df550dc4ef794692eea171420658827804b2b93cb39fc0b3990f75b6d1b29c1/analysis/
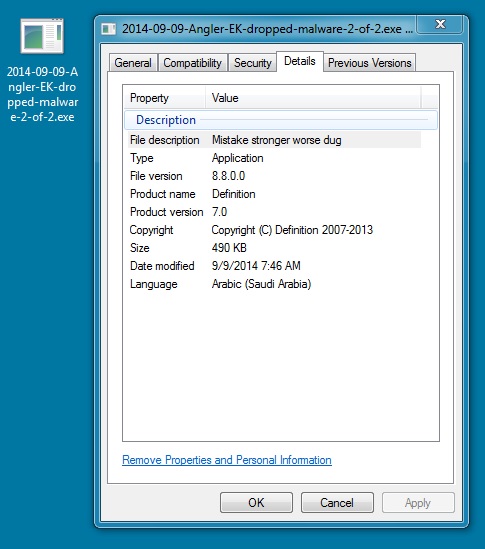
DROPPED MALWARE 2 OF 2:
File name: 2014-09-09-Angler-EK-dropped-malware-2-of-2.exe
File size: 502,284
MD5 hash: ab6c0871794252ab3f6a2c97d87c9857
Detection ratio: 4 / 55
First submission: 2014-09-09 15:23:33 UTC
VirusTotal link: https://www.virustotal.com/en/file/ee549fef895947a50641c96491c1e6e13c4bcd3c9f0eaa95ad5e5593a65c673e/analysis/
ALERTS
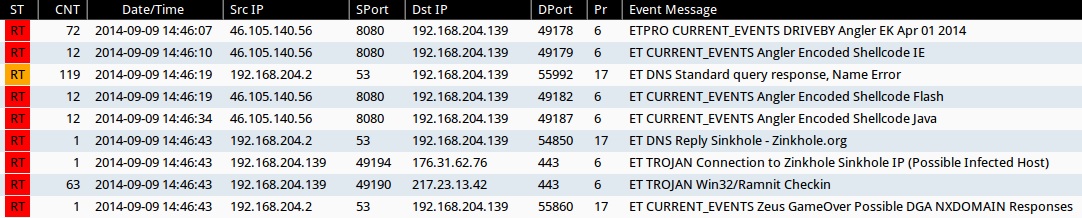
Emerging Threats and ETPRO rulesets from Sguil on Security Onion (without ET POLICY or ET INFO events):
- 2014-09-09 14:46:07 UTC - 46.105.140[.]56:8080 - ETPRO CURRENT_EVENTS DRIVEBY Angler EK Apr 01 2014 (sid:2807913)
- 2014-09-09 14:46:10 UTC - 46.105.140[.]56:8080 - ET CURRENT_EVENTS Angler Encoded Shellcode IE (sid:2018954)
- 2014-09-09 14:46:19 UTC - [internal host]:53 - ET DNS Standard query response, Name Error (sid:2001117)
- 2014-09-09 14:46:19 UTC - 46.105.140[.]56:8080 - ET CURRENT_EVENTS Angler Encoded Shellcode Flash (sid:2018956)
- 2014-09-09 14:46:34 UTC - 46.105.140[.]56:8080 - ET CURRENT_EVENTS Angler Encoded Shellcode Java (sid:2018957)
- 2014-09-09 14:46:43 UTC - [internal host]:53 - ET DNS Reply Sinkhole - Zinkhole.org (sid:2016419)
- 2014-09-09 14:46:43 UTC - 176.31.62[.]76:443 - ET TROJAN Connection to Zinkhole Sinkhole IP (Possible Infected Host) (sid:2016419)
- 2014-09-09 14:46:43 UTC - 217.23.13[.]42:443 - ET TROJAN Win32/Ramnit Checkin (sid:2018558)
- 2014-09-09 14:46:43 UTC - [internal host]:53 - ET CURRENT_EVENTS Zeus GameOver Possible DGA NXDOMAIN Responses (sid:2018316)
Sourcefire VRT ruleset from Snort 2.9.6.2 on Ubuntu 14.04 LTS:
- 2014-09-09 14:46:16 UTC - 46.105.140[.]56:8080 - [120:8:2] (http_inspect) INVALID CONTENT-LENGTH OR CHUNK SIZE
- 2014-09-09 14:46:43 UTC - various:443 - [1:31528:1] MALWARE-CNC Win.Trojan.Ramnit variant outbound detected (x12)
- 2014-09-09 14:46:43 UTC - 1various:443 - [1:31527:1] MALWARE-CNC Win.Trojan.Ramnit variant outbound detected (x30)
Click here to return to the main page.