2016-08-31 - PSEUDO-DARKLEECH NEUTRINO EK FROM 69.162.96[.]148 SENDS CRYPMIC RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Z2016-08-31-pseudoDarkleech-Neutrino-EK-sends-CrypMIC-ransomware.pcap.zip 232.7 kB (232,738 bytes)
- 2016-08-31-pseudoDarkleech-Neutrino-EK-sends-CrypMIC-ransomware.pcap (475,491 bytes)
- 2016-08-31-pseudoDarkleech-Neutrino-EK-and-CrypMIC-ransomware-files.zip 197.4 kB (197,361 bytes)
- 2016-08-31-page-from-nycrunningmama_com-with-injected-script.txt (205,375 bytes)
- 2016-08-31-pseudoDarkleech-Neutrino-EK-flash-exploit.swf (76,212 bytes)
- 2016-08-31-pseudoDarkleech-Neutrino-EK-landing-page.txt (2,344 bytes)
- 2016-08-31-pseudoDarkleech-Neutrino-EK-payload-CrypMIC.dll (69,632 bytes)
- README.BMP (3,276,854 bytes)
- README.HTML (238,182 bytes)
- README.TXT (1,654 bytes)
NOTES:
- Special thanks to Baber for providing me info about the compromised site.
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-03-22 - PaloAlto Networks Unit 42 blog: Campaign Evolution: Darkleech to Pseudo-Darkleech and Beyond
- 2016-07-02 - SANS ISC diary: Change in patterns for the pseudoDarkleech campaign
BACKGROUND ON CRYPMIC RANSOMWARE:
- 2016-07-06 - SANS ISC diary: CryptXXX ransomware updated [The date I first noticed this new branch of ransomware.]
- 2016-07-14 - From the Proofpoint blog [link]: "We believe that CryptXXX is in active development and possibly split off into two branches. The original branch is now up to version 5.001 (we wrote about the upgrade to version 3.100 near the end of May), while the new branch uses a different format for versioning and will require further analysis."
- 2016-07-20 - TrendLabs Security Intelligence Blog - CrypMIC Ransomware Wants to Follow CryptXXX's Footsteps [TrendLabs analyzes the new branch and names it.]
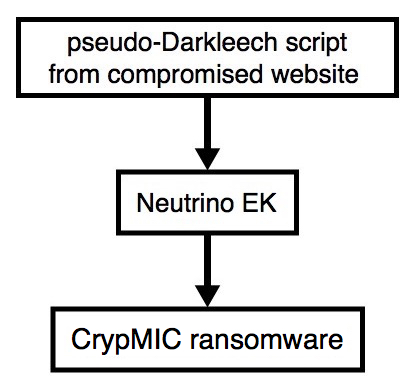
Shown above: Flowchart for this infection traffic.
TRAFFIC

Shown above: Injected script from the pseudoDarkleech campaign in page from the compromised site.

Shown above: Traffic from the pcap filtered in Wireshark. Wireshark filter: http.request or (!(tcp.port eq 80) and tcp.flags eq 0x0002)
ASSOCIATED DOMAINS:
- www.nycrunningmama[.]com - Compromised site
- 69.162.96[.]148 port 80 - zaposlen1-neyle.redhilltsa[.]org[.]uk - Neutrino EK
- 95.211.225[.]212 port 443 - Post-infection callback traffic (no response from the server)
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- ccjlwb22w6c22p2k[.]onion[.]to
- ccjlwb22w6c22p2k[.]onion[.]city
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 14f6d73bc167da3c7e9c6373fff63dafb1fdd921881068b0cf5387fbcbf4c237
File name: 2016-08-31-pseudoDarkleech-Neutrino-EK-flash-exploit.swf
PAYLOAD:
- SHA256 hash: 668262d0757185dbd0a48bb5a3ffe42a8b5f4cb6bf4e7a99e53d342146928ef1
File name: 2016-08-31-pseudoDarkleech-Neutrino-EK-payload-CrypMIC-ransomware.dll
IMAGES
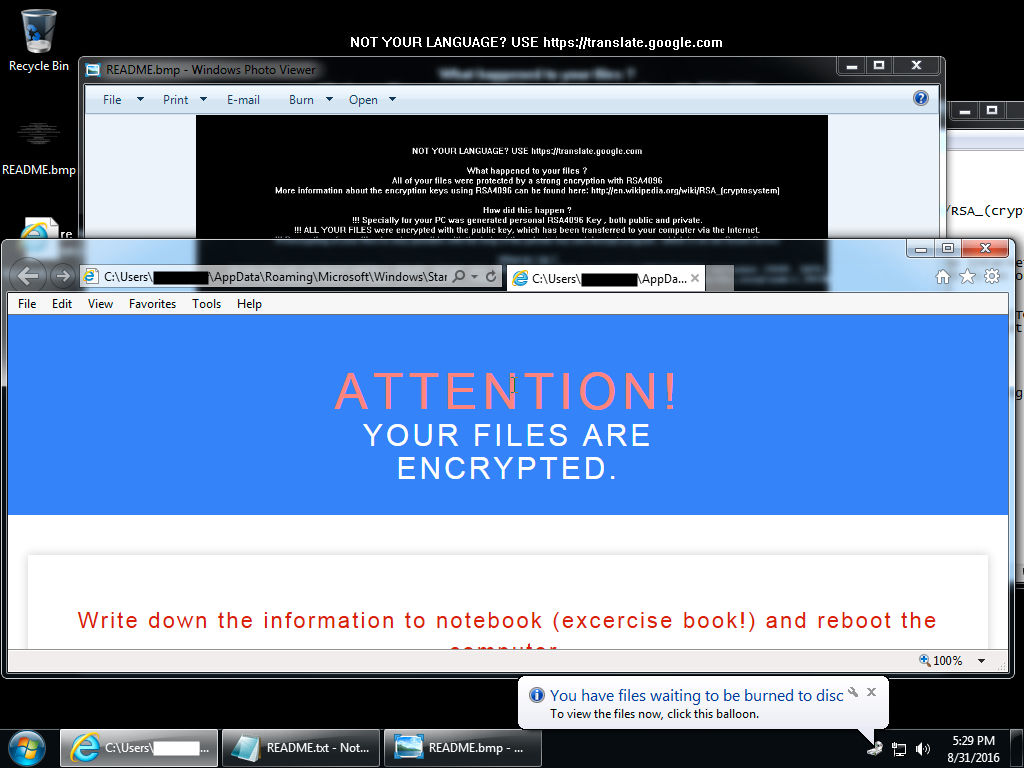
Shown above: Desktop of an infected Windows host after rebooting.
Click here to return to the main page.