2016-10-06 - PSEUDO-DARKLEECH RIG EK FROM 107.191.63[.]102 SENDS CERBER RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-06-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware.pcap.zip 349.4 kB (349,390 bytes)
- 2016-10-06-pseudoDarkleech-Rig-EK-sends-Cerber-ransomware.pcap (461,857 bytes)
- 2016-10-06-pseudoDarkleech-Rig-EK-and-Cerber-ransomware-files.zip 329.1 kB (329,071 bytes)
- 2016-10-06-Cerber-ransomware-decrypt-instructions-README.hta (63,059 bytes)
- 2016-10-06-page-from-howmuchtofly_com-with-injected-script.txt (28,871 bytes)
- 2016-10-06-pseudoDarkleech-Rig-EK-flash-exploit.swf (24,738 bytes)
- 2016-10-06-pseudoDarkleech-Rig-EK-landing-page.txt (30,091 bytes)
- 2016-10-06-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware.exe (284,645 bytes)
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-03-22 - PaloAlto Networks Unit 42 blog: Campaign Evolution: Darkleech to Pseudo-Darkleech and Beyond
- 2016-07-02 - SANS ISC diary: Change in patterns for the pseudoDarkleech campaign
- 2016-09-14 - Malware-traffic-analysis.net: The pseudoDarkleech campaign starts using Rig EK instead of Neutrino EK
- 2016-10-03 - Malware-traffic-analysis.net: The pseudoDarkleech campaign stops sending CryptXXX, starts sending Cerber ransomware
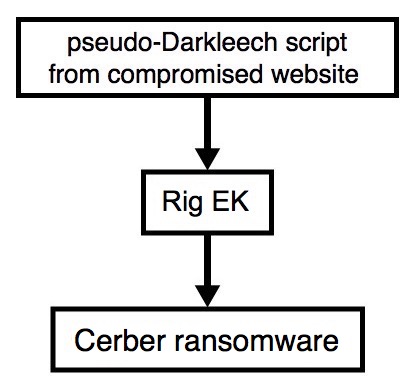
Shown above: Flowchart for this infection traffic.
TRAFFIC
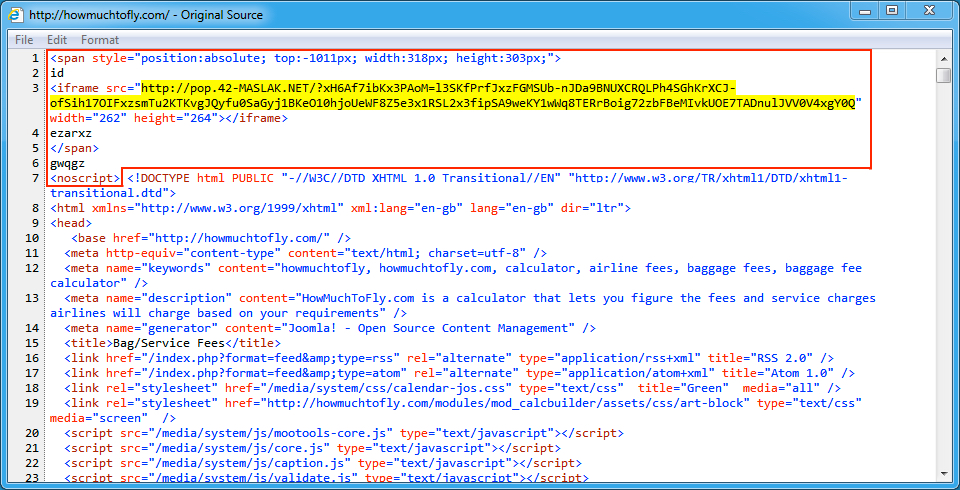
Shown above: Injected script from the pseudoDarkleech campaign in page from the compromised site.
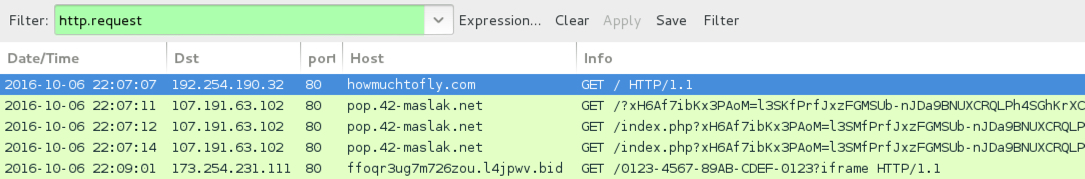
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- howmuchtofly[.]com - Compromised website
- 107.191.63[.]102 port 80 - pop.42-maslak[.]net - Rig EK
- 31.184.234[.]0 - 31.184.235[.]255 port 6892 (UDP) - UDP traffic caused by Cerber ransomware
- 173.254.231[.]111 port 80 - ffoqr3ug7m726zou.l4jpwv[.]bid - HTTP traffic caused by Cerber ransomware
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- ffoqr3ug7m726zou.13uvry[.]top
- ffoqr3ug7m726zou.3nke6l[.]bid
- ffoqr3ug7m726zou[.]onion[.]to
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 662ba372c286dcd19d52720052b2f8bb9042d60dea47349974016f39b454d46e
File name: 2016-10-06-pseudoDarkleech-Rig-EK-flash-exploit.swf (24,738 bytes)
PAYLOAD:
- SHA256 hash: 5a657b257dea1e2e0703a3afaac814bdca239721d51b293581de71b4a90ea624
File name: 2016-10-06-pseudoDarkleech-Rig-EK-payload-Cerber-ransomware.exe (284,645 bytes)
Click here to return to the main page.