2016-05-02 - PSEUDO-DARKLEECH ANGLER EK FROM 185.73.221[.]95 SENDS BEDEP AND CRYPTXXX RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-05-02-pseudo-Darkleech-Angler-EK-sends-Bedep-and-CryptXXX-ransomware.pcap.zip 3.3 MB (3,300,340 bytes)
- 2016-05-02-pseudo-Darkleech-Angler-EK-sends-Bedep-and-CryptXXX-ransomware.pcap (3,540,047 bytes)
- 22016-05-02-pseudo-Darkleech-Angler-EK-and-Bedep-and-CryptXXX-ransomware-files.zip 655.6 kB (655,648 bytes)
- 2016-05-02-CryptXXX-ransomware-de_crypt_readme.bmp (2,326,734 bytes)
- 2016-05-02-CryptXXX-ransomware-de_crypt_readme.html (3,315 bytes)
- 2016-05-02-CryptXXX-ransomware-de_crypt_readme.txt (1,638 bytes)
- 2016-05-02-CryptXXX-ransomware.dll (223,232 bytes)
- 2016-05-02-click-fraud-malware.dll (773,280 bytes)
- 2016-05-02-page-from-blushdentalstudio_com-with-injected-pseudo-Darkleech-script.txt (13,095 bytes)
- 2016-05-02-pseudo-Darkleech-Angler-EK-flash-exploit.swf (66,922 bytes)
- 2016-05-02-pseudo-Darkleech-Angler-EK-landing-page.txt (91,294 bytes)
NOTES:
- On Friday 2016-04-29, I saw a renamed rundll32.exe dropped in the same folder as the CryptXXX ransomware .dll file, and it was used to load the CryptXXX ransomware.
- Today (Monday 2016-05-02), things are back to normal, with just the CryptXXX ransomware .dll file by itself in the folder.
- Today's Click-fraud malware: C:\ProgramData\{9A88E103-A20A-4EA5-8636-C73B709A5BF8}\shsetup.dll
- Today's CryptXXX: C:\Users\[username]\AppData\Local\Temp\{FDA5ED60-817E-44A9-B028-FDCC3D6F1D9B}\api-ms-win-system-NativeHooks-l1-1-0.dll
- Background on the pseudo-Darkleech campaign is available here.
- Proofpoint's blog on Angler EK spreading CryptXXX ransomware can be found here.
- An ISC diary I wrote about pseudo-Darkleech causing Angler EK/Bedep/CryptXXX infections is located here.
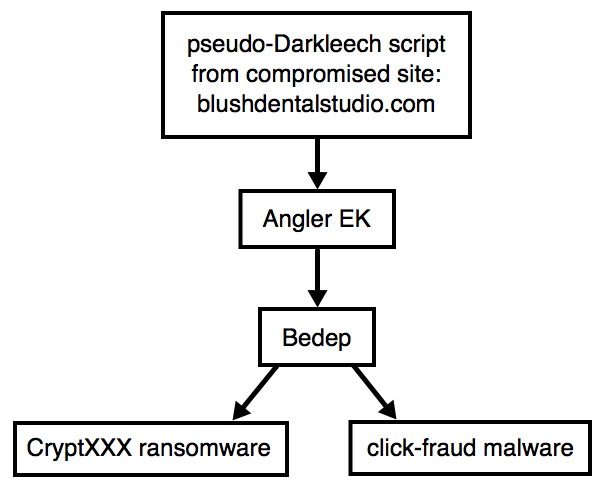
Shown above: Chain of events for today's infection.
TRAFFIC
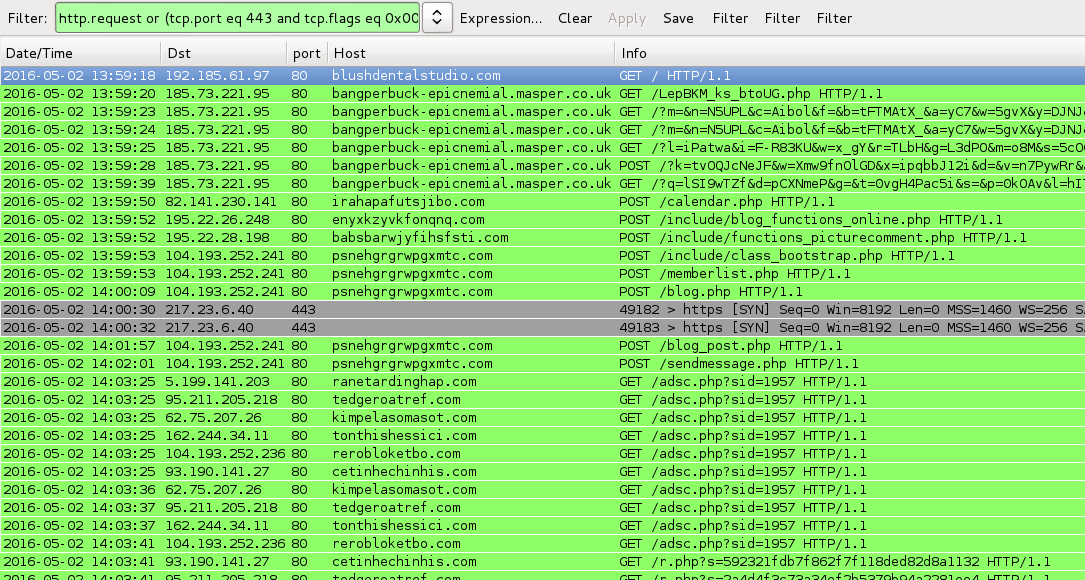
Shown above: Pcap of the traffic filtered in Wireshark. http.request or (tcp.port eq 443 and tcp.flags eq 0x0002)
ASSOCIATED DOMAINS:
- 185.73.221[.]95 port 80 - bangperbuck-epicnemial.masper[.]co[.]uk - Angler EK
TRAFFIC CAUSED BY BEDEP:
- 82.141.230[.]141 port 80 - irahapafutsjibo[.]com - POST /calendar.php
- 195.22.26[.]248 port 80 - enyxkzyvkfonqnq[.]com - POST /include/blog_functions_online.php
- 195.22.28[.]198 port 80 - babsbarwjyfihsfsti[.]com - POST /include/functions_picturecomment.php
- 104.193.252[.]241 port 80 - psnehgrgrwpgxmtc[.]com - POST /include/class_bootstrap.php
- 104.193.252[.]241 port 80 - psnehgrgrwpgxmtc[.]com - POST /memberlist.php
- 104.193.252[.]241 port 80 - psnehgrgrwpgxmtc[.]com - POST /blog.php
- 104.193.252[.]241 port 80 - psnehgrgrwpgxmtc[.]com - POST /blog_post.php
- 104.193.252[.]241 port 80 - psnehgrgrwpgxmtc[.]com - POST /sendmessage.php
TRAFFIC CAUSED BY BEDEP:
- 217.23.6[.]40 port 443 - custom encoded TCP traffic
TRAFFIC CAUSED BY CLICK-FRAUD MALWARE:
- 5.199.141[.]203 port 80 - ranetardinghap[.]com - GET /adsc.php?sid=1957
- 95.211.205[.]218 port 80 - tedgeroatref[.]com - GET /adsc.php?sid=1957
- 62.75.207[.]26 port 80 - kimpelasomasot[.]com - GET /adsc.php?sid=1957
- 162.244.34[.]11 port 80 - tonthishessici[.]com - GET /adsc.php?sid=1957
- 104.193.252[.]236 port 80 - rerobloketbo[.]com - GET /adsc.php?sid=1957
- 93.190.141[.]27 port 80 - cetinhechinhis[.]com - GET /adsc.php?sid=1957
IMAGES
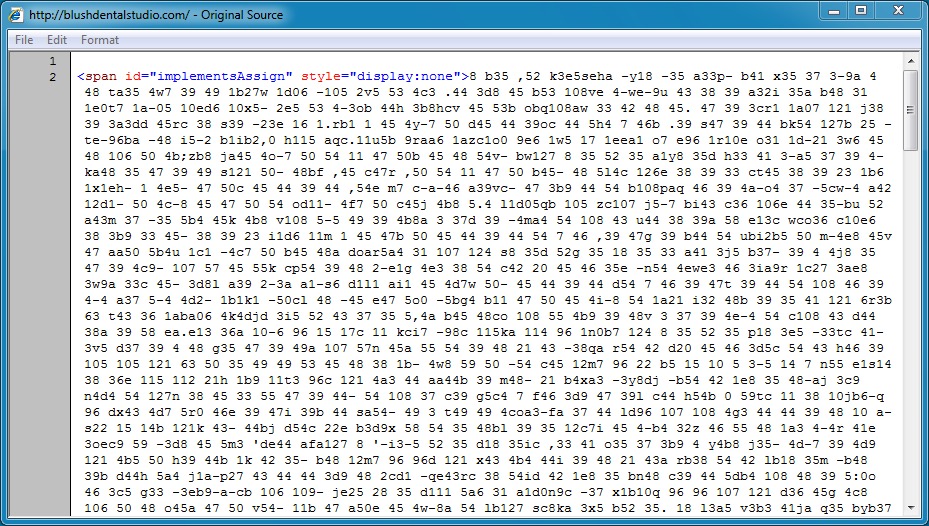
Shown above: Start of pseudo-Darkleech script returned from compromised website.
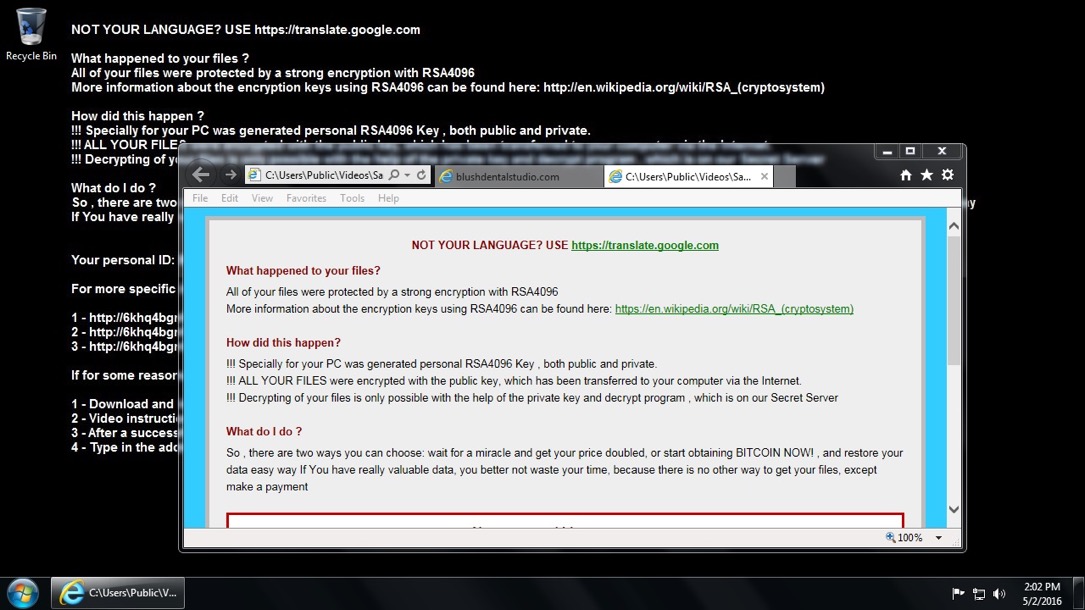
Shown above: Desktop of the Windows host after the Angler EK/Bedep/CryptXXX infection.
Click here to return to the main page.