2016-05-13 - TRAFFIC ANALYSIS EXERCISE - NO DECENT MEMES FOR SECURITY ANALYSTS
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive for this exercise: 2016-05-13-traffic-analysis-exercise-files.zip 9.9 MB (9,899,148 bytes)
- 2016-05-13-traffic-analysis-exercise-snort-events.txt (42,092 bytes)
- 2016-05-13-traffic-analysis-exercise-suricata-events.txt (91,105 bytes)
- 2016-05-13-traffic-analysis-exercise.pcap (11,655,628 bytes)
SCENARIO
The media likes to present cyber criminals as solitary hackers. The image below has a stereotypical portrayal. You can tell he's a criminal, because he's wearing a hoodie while typing on a laptop. You can tell this is cyber-related, because he's covered in ones and zeros.

Shown above: Cyber criminals as portrayed by the media.
In reality, massive campaigns routinely distributing malware indicate these hackers might be highly-organized groups that schedule time off for weekends and holidays.
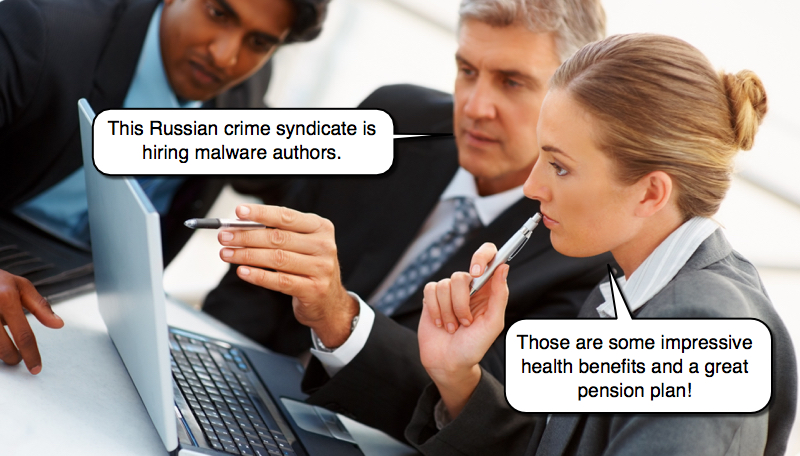
Shown above: How I picture cyber criminals.
This is crimeware. It's a world of numerous compromised websites directing traffic to exploit kits, wave after wave of malicious spam, and various routes of malware distribution seen on a near-daily basis. Indicators for crimeware are constantly changing. It's a cat and mouse game, where criminals are often one step ahead of the security professionals who defend our networks.
How can we counter this crimeware threat? A key component is near-real-time detection and analysis. The term "security analyst" is often used as a job title for foot soldiers in this cyber war. A security analyst is responsible for investigating suspicious events provided by intrusion detection systems (IDS) in near-real-time.
If you're a security analyst, what does the current crimeware landscape mean? It means, no matter how much protection your company has, at some point something will probably get through.
These traffic analysis exercises are designed to help analysts and other security professionals improve or keep up their skills. In this month's exercise, a user's infected computer generated several alerts. Your task is to examine the pcap and determine what happened. Included are two text files with the IDS events. One has signature hits from Snort using the Talos subscriber ruleset. The other has signature hits from Suricata using the EmergingThreats Pro ruleset.
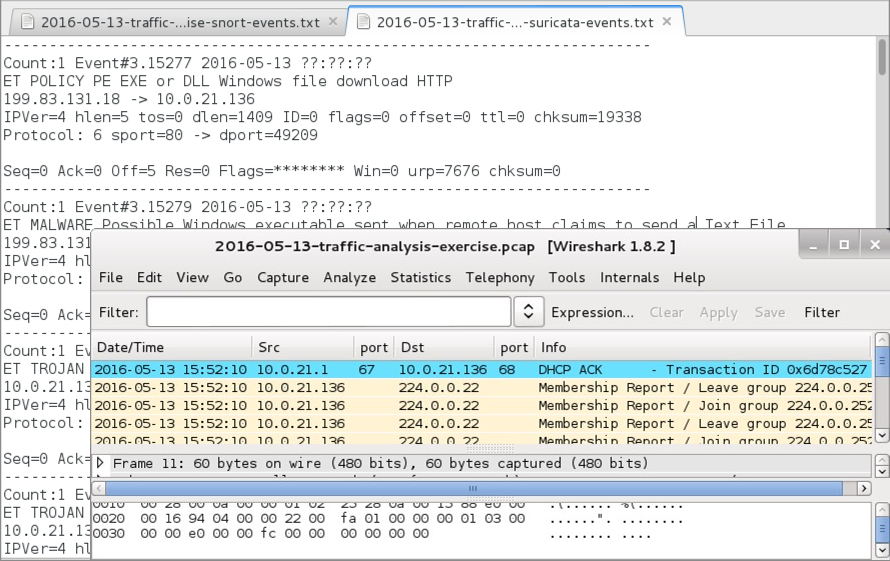
Shown above: Material for this traffic analysis exercise.
Review the traffic and consult the alerts if necessary. You should be able to get the following information from the pcap:
- The user's first and last name
- The host name of the user's Windows computer
- The MAC address of the user's Windows computer
- What type(s) or item(s) of malware the user's computer is infected with.
- How the user's computer got infected with the item(s) of malware.
The only drawback about being a security analyst? No decent memes. Can someone come up with a good meme about security analysts? If so, you'll be doing the security community a favor. In the image below, I fixed a meme I found (the one on the left) to fit the actual song lyrics (the one on the right).

Most probably don't care, but it's important to me.
I ask anyone reading this to create a meme about security analysts. Share your creation through Twitter using #securityanalystmeme. If you don't use Twitter, email your meme to admin@malware-traffic-analysis.net and I'll tweet it for you.
Meanwhile, enjoy the exercise.
2024 follow-up note: I cannot find any evidence that anyone responded to this meme challenge.
ANSWERS
- Click here for the answers.
Click here to return to the main page.
