2017-05-24 - JAFF RANSOMWARE INFECTION
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-05-24-Jaff-ransomware-traffic.pcap.zip 148.7 kB (148,746 bytes)
- 2017-05-24-Jaff-ransomware-malspam-tracker.csv.zip 0.9 kB (861 bytes)
- 2017-05-24-Jaff-ransomware-emails-and-malware.zip 883.6 kB (883,588 bytes)
NOTES:
- More information on this campaign can be found at: https://isc.sans.edu/forums/diary/Jaff+ransomware+gets+a+makeover/22446/
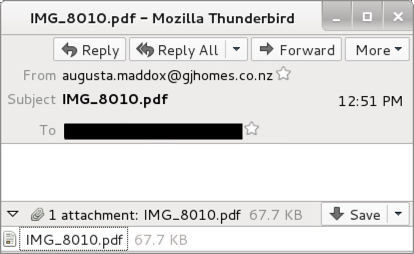
Shown above: An example of the emails.
4 EMAIL EXAMPLES:
READ: DATE/TIME -- SENDING ADDRESS (SPOOFED) -- SUBJECT -- ATTACHMENT NAME
- 2017-05-24 12:13:34 UTC -- morgan.pooley@menton-nautic-motors[.]com -- IMG_6943.pdf -- IMG_6943.pdf
- 2017-05-24 12:19:00 UTC -- ethel.maberley@dustybootsfarms[.]com -- img_5426.pdf -- img_5426.pdf
- 2017-05-24 12:27:10 UTC -- arturo.leavesley@baskoolstra[.]nl -- img_9117.pdf -- img_9117.pdf
- 2017-05-24 12:51:30 UTC -- augusta.maddox@gjhomes[.]co[.]nz -- IMG_8010.pdf -- IMG_8010.pdf
MALWARE
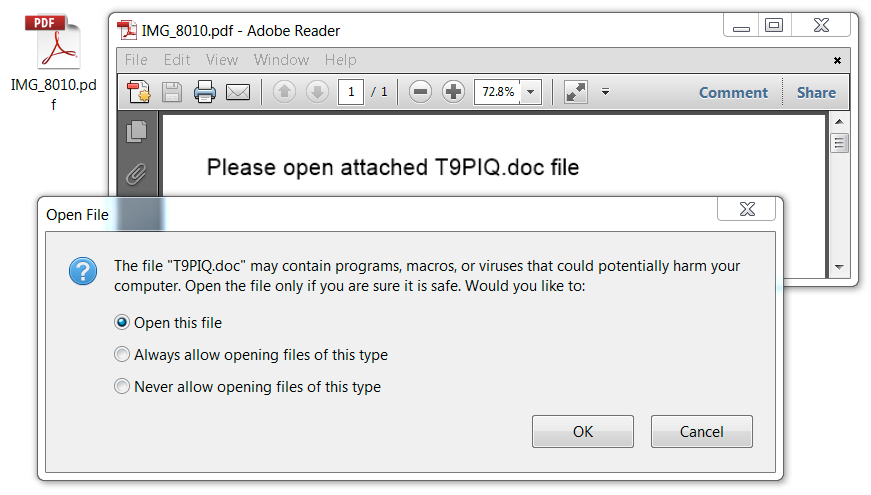
Shown above: As usual, the PDF attachment contains an embedded Word document with malicious macros.
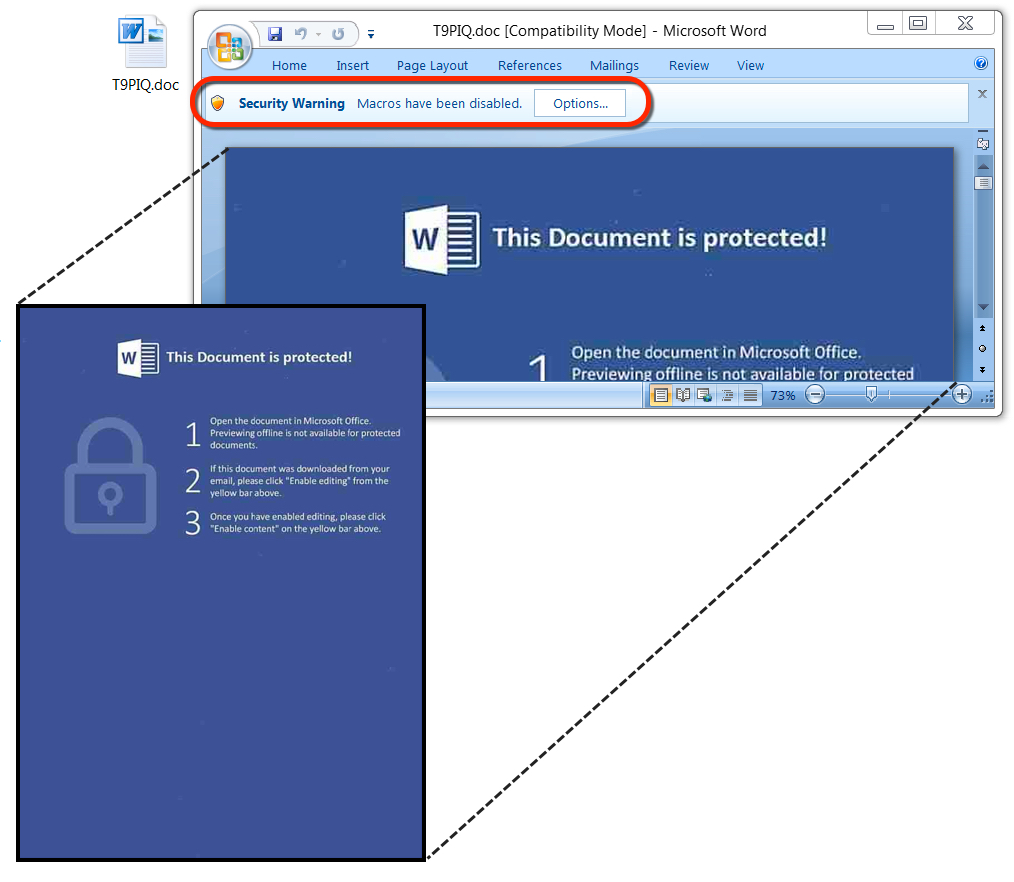
Shown above: No marks today in the bottom half of the images in these Word documents.
SHA256 HASHES FOR THE PDF ATTACHMENTS:
- 23b8ff79b843ec1b7b963bd7bff5d30161bf805bb2b8904c336d2da3dcf41dcb - img_9117.pdf
- 6faa78da1d6d8028d61ea96e16089893e3ba93e4dc357d552edd58df0bcfe2cd - img_5426.pdf
- 9580f0eb3807e78ec876fb1b439a3455113d5e66d2d3470bf0eca06748fc9ee1 - IMG_8010.pdf
- eb3cee41ccabe1449d99d36c255dc9d6162fe5931f32a9f73464be67df8b80cb - IMG_6943.pdf
SHA256 HASHES FOR THE EMBEDDED WORD DOCUMENTS:
- 018c0c2a56bcc94364aed07341e529c45f52c1e011b84fe5603a10d3f59e6f85 - T9PIQ.doc
- 3084e31a061f6adf56486e959450166671072c5503e35703a70f8f40424d7188 - U2MH1.doc
- a9eeb194ea0cfa3fb46a651b328e56fdd4428a13c893a4066a75bf407a14ab65 - GWM2CKV.doc
- df85f57b904273a5f14ee5f7f3aabdcb1f3c882f30e05caa05dc76c138f878e2 - XXZSTFDB.doc
JAFF RANSOMWARE SAMPLE:
- SHA256 hash: 077b498d9cc163e1ff5547e1abd625b8655f0339cb5e79d64c2ded17abb9e425
File size: 245,760 bytes
File location: C:\Users\[username]\AppData\Local\Temp\bruhadson8.exe
TRAFFIC
URLS FROM THE WORD MACROS TO DOWNLOAD JAFF RANSOMWARE:
- better57toiuydof[.]net - GET /af/FsMflooY
- david-faber[.]de - GET /FsMflooY
- digital-helpdesk[.]com - GET /FsMflooY
- dogplay[.]co[.]kr - GET /FsMflooY
- ecoeventlogistics[.]com - GET /FsMflooY
- elateplaza[.]com - GET /FsMflooY
- minnessotaswordfishh[.]com - GET /af/FsMflooY
- pcflame[.]com[.]au - GET /FsMflooY
- tdtuusula[.]com - GET /FsMflooY
- uslugitransportowe-warszawa[.]pl - GET /FsMflooY
JAFF RANSOMWARE POST-INFECTION TRAFFIC:
- 198.105.244[.]228 port 80 y887drossetorling[.]info - GET /a5/
- rktazuzi7hbln7sy[.]onion - Tor domain for Jaff Decryptor (same as the last few times)
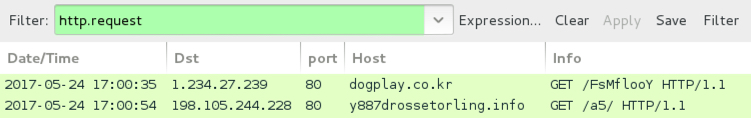
Traffic from the infection filtered in Wireshark.
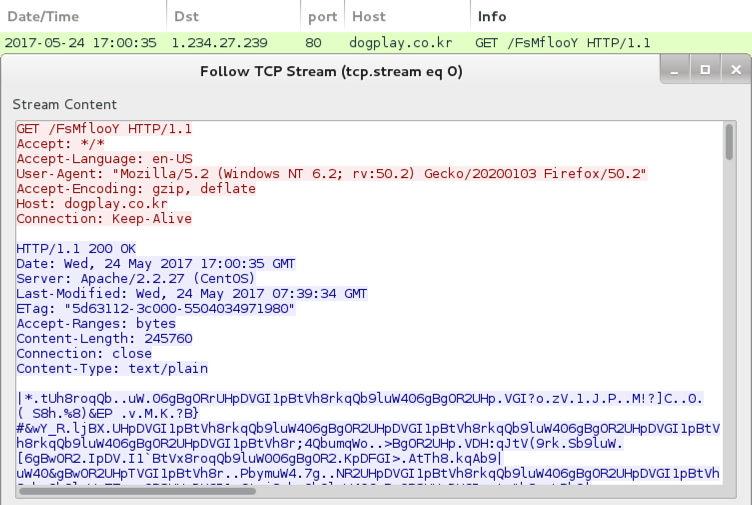
HTTP request for the Jaff ransomware.
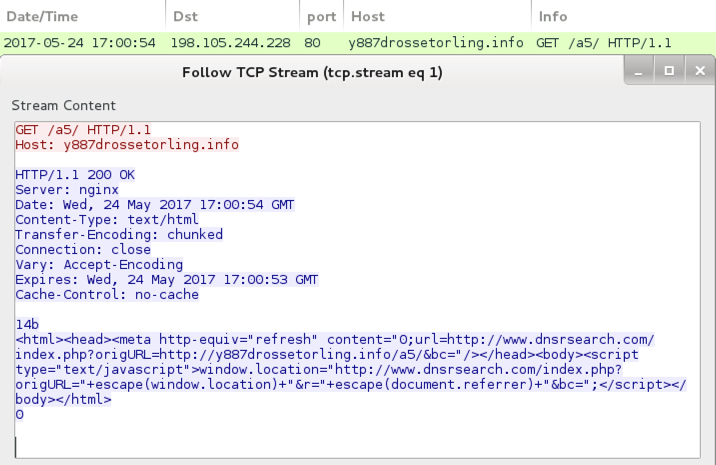
Post-infection traffic from the infected Windows host.
IMAGES
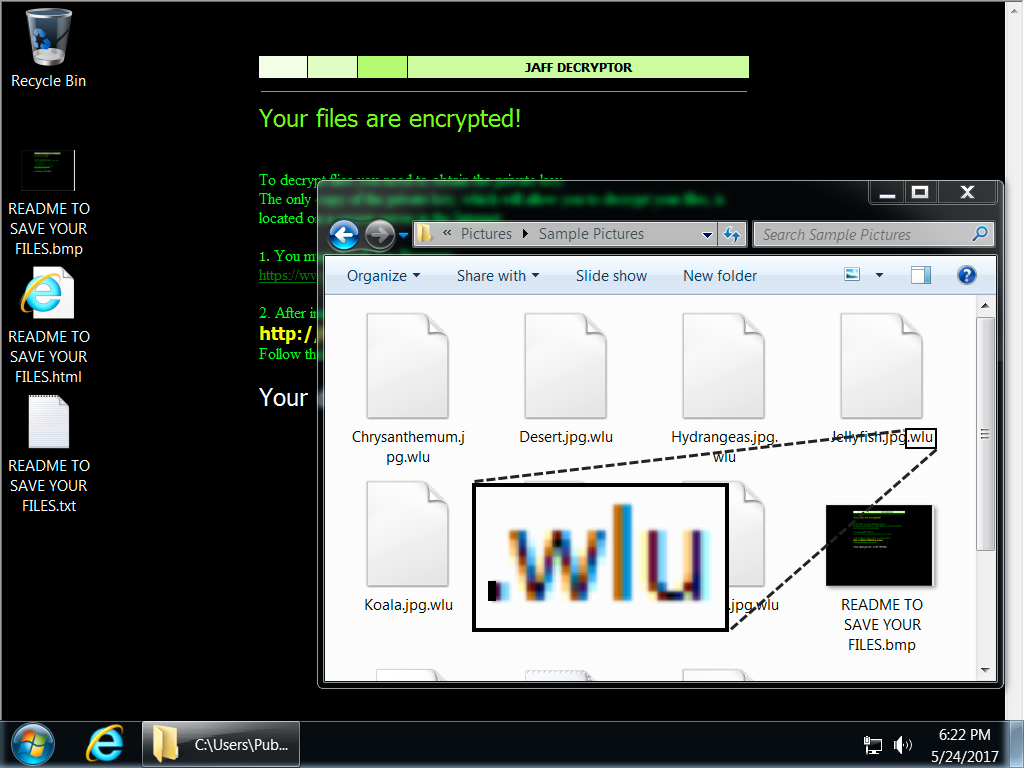
Shown above: Desktop of an infected Windows host.
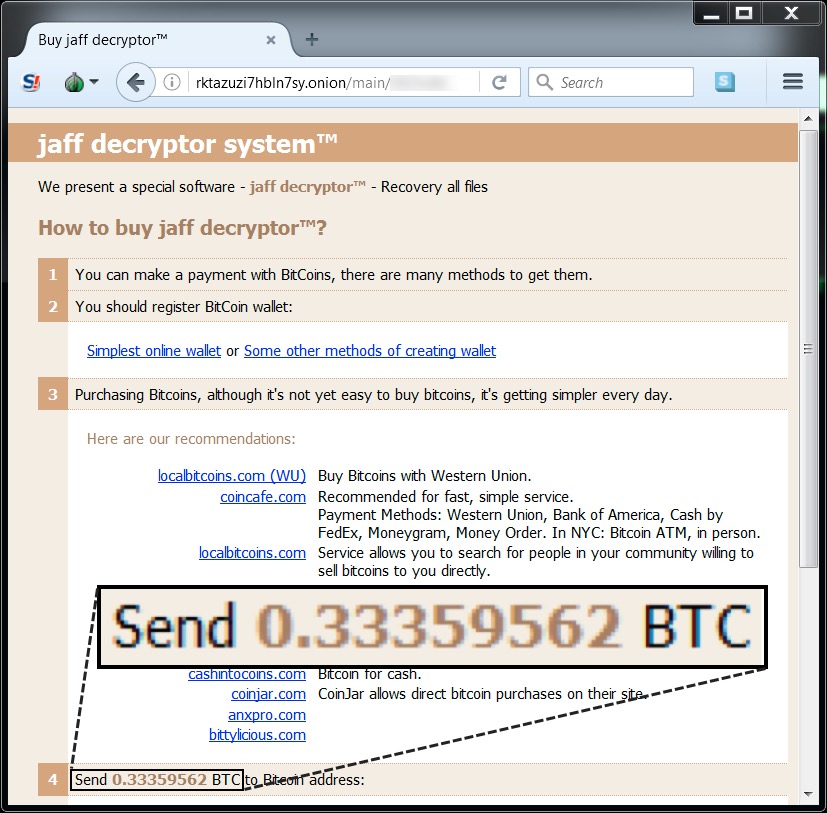
Shown above: Going to the Jaff Decryptor.
Click here to return to the main page.
