2017-05-25 - HANCITOR INFECTION WITH ZLOADER
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-05-25-Hancitor-infection-with-ZLoader.pcap.zip 12.96 MB (12,961,984 bytes)
- 2017-05-25-Hancitor-infection-with-ZLoader.pcap (13,624,335 bytes)
- 2017-05-25-Hancitor-malspam-1616-UTC.eml.zip 1.4 kB (1,435 bytes)
- 2017-05-25-Hancitor-malspam-1616-UTC.eml (3,210 bytes)
- 2017-05-25-malware-from-Hancitor-infection.zip 242.9 kB (242,878 bytes)
- BNE9F0.tmp (176,640 bytes)
- Billing_ruinedsunglass.doc (206,336 bytes)
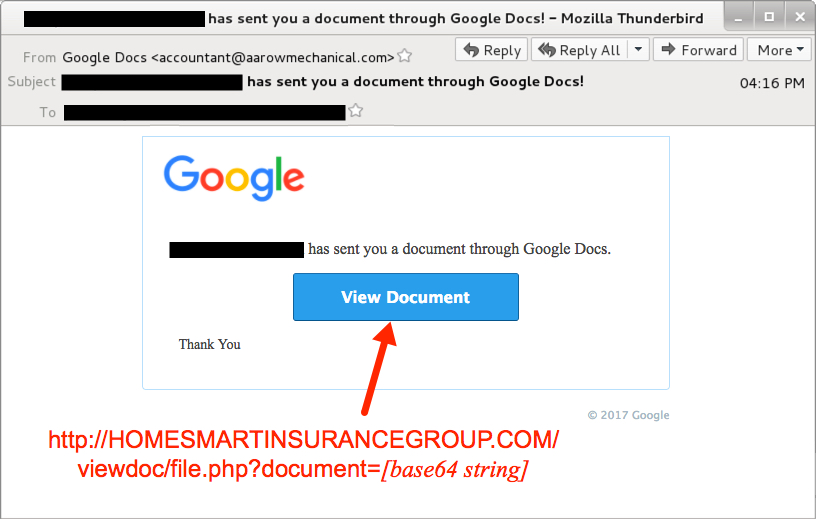
Shown above: Screen shot from one of the emails.
EMAIL HEADERS:
- Date: Thursday 2017-05-25
- Subject: [recipient's email domain] has sent you a document through Google Docs!
- From: "Google Docs" <accountant@aarowmechanical[.]com>
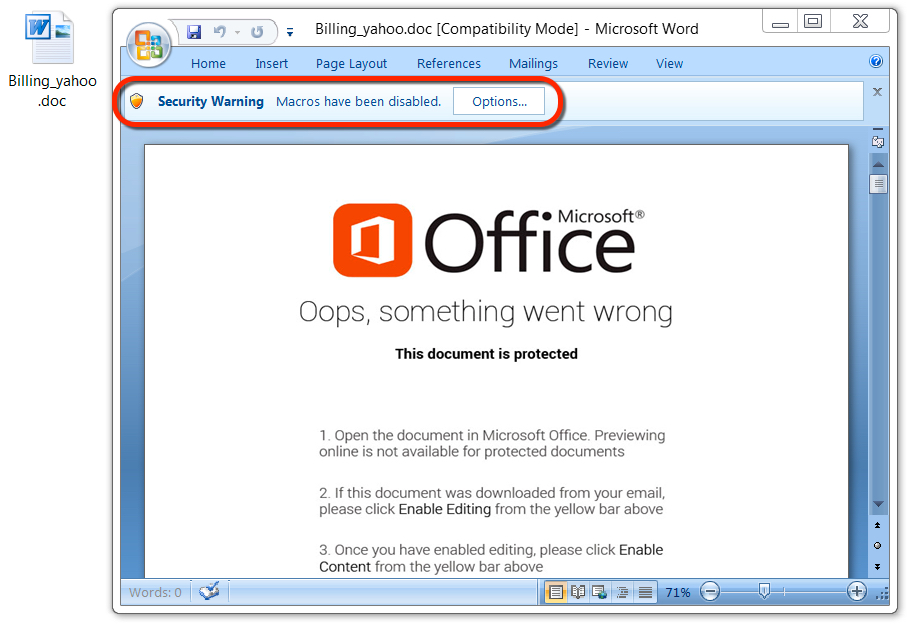
Shown above: Malicious Word document from link in the malspam.
TRAFFIC
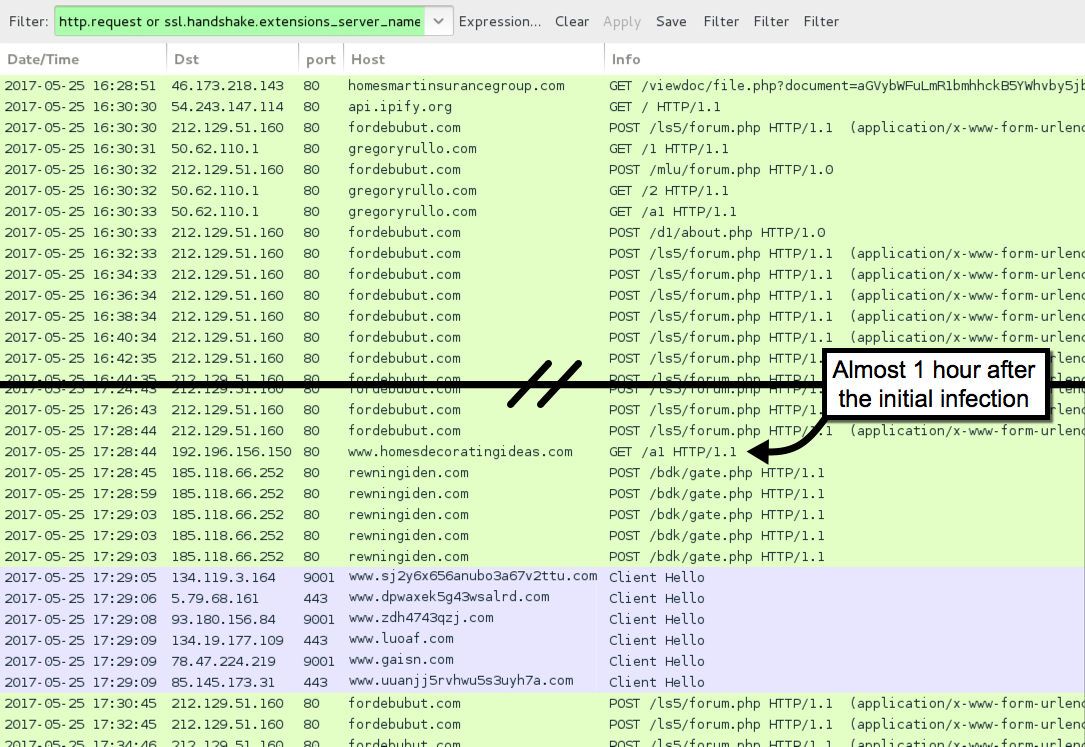
Shown above: Traffic from the infection filtered in Wireshark.
HTTP REQUESTS FOR THE WORD DOCUMENT:
- 46.173.218[.]143 port 80 - homesmartinsurancegroup[.]com - GET /viewdoc/file.php?document=[base64 string]
NAME FOR THE MALICIOUS WORD DOCUMENTS:
- Billing_[recipient's email domain without the suffix].doc
POST-INFECTION TRAFFIC FROM MY ONE INFECTED HOST:
- 212.129.51[.]160 port 80 - fordebubut[.]com - POST /ls5/forum.php
- 212.129.51[.]160 port 80 - fordebubut[.]com - POST /mlu/forum.php
- 212.129.51[.]160 port 80 - fordebubut[.]com - POST /d1/about.php
- 50.62.110[.]1 port 80 - gregoryrullo[.]com - GET /1
- 50.62.110[.]1 port 80 - gregoryrullo[.]com - GET /2
- 50.62.110[.]1 port 80 - gregoryrullo[.]com - GET /a1
- 192.196.156[.]150 port 80 - www.homesdecoratingideas[.]com - GET /a1
- 185.118.66[.]252 port 80 - rewningiden[.]com - POST /bdk/gate.php
- 198.105.244[.]228 port 80 - kedrolhechedt[.]com - POST /bdk/gate.php
- 198.105.244[.]228 port 80 - dijussoda[.]com - POST /bdk/gate.php
- api.ipify[.]org - GET /
- Various IP addresses on various TCP ports - Tor traffic
FILE HASHES
WORD DOCUMENT FROM LINK IN THE EMAIL:
- SHA256 hash: 0cf705e4804f3585e44368e8d611ddb9376863ff8c4400d156d043f6b181924e
File name: Billing_ruinedsunglass.doc
File size: 206,336 bytes
File description: Hancitor maldoc
MALWARE RETRIEVED FROM THE INFECTED HOST:
- SHA256 hash: dc8aa91015f1f67639b13489bd556e425aacc308d902ddf7585adf856c3aa7b2
File location: C:\Users\[username]\AppData\Local\Temp\BNE9F0.tmp
File size: 176,640 bytes
File description: DELoader/ZLoader
Click here to return to the main page.
