2017-06-06 - HANCITOR INFECTION WITH ZLOADER
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-06-06-Hancitor-infection-with-ZLoader.pcap.zip 9.1 MB (9,075,128 bytes)
- 2017-06-06-Hancitor-infection-with-ZLoader.pcap (9,827,835 bytes)
- 2017-06-06-Hancitor-malspam-4-examples.zip 4.9 kB (4,853 bytes)
- 2017-06-06-Hancitor-malspam-1434-UTC.eml (1,712 bytes)
- 2017-06-06-Hancitor-malspam-1501-UTC.eml (1,697 bytes)
- 2017-06-06-Hancitor-malspam-1521-UTC.eml (1,699 bytes)
- 2017-06-06-Hancitor-malspam-1747-UTC.eml (1,696 bytes)
- 2017-06-06-malware-from-Hancitor-infection.zip 252.5 kB (252,535 bytes)
- BNA208.tmp (187,904 bytes)
- eFax_aol.doc (225,792 bytes)
NOTES:
- @James_inthe_box also reported on today's wave of Hancitor malspam (link).
EMAILS
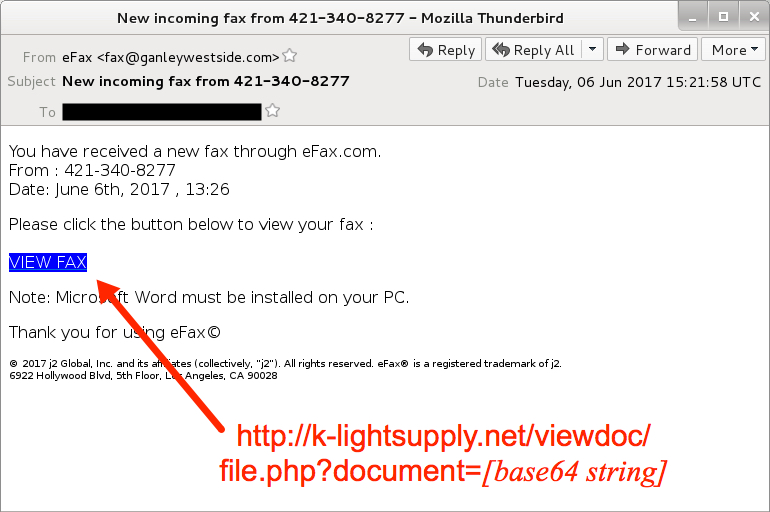
Shown above: Screen shot from one of the emails.
EMAIL HEADERS:
- Date: Tuesday 2017-06-06 as early as 14:34 UTC through at least 17:47 UTC
- From: "eFax" <fax@ganleywestside[.]com>
- Subject: New incoming fax from 421-310-1472
- Subject: New incoming fax from 421-337-7648
- Subject: New incoming fax from 421-346-4073
- Subject: New incoming fax from 421-340-8277
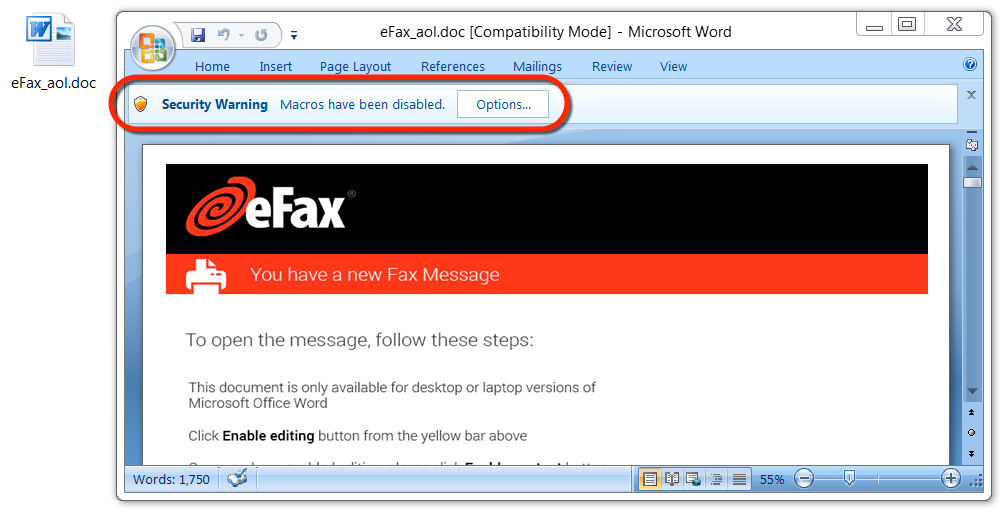
Shown above: Malicious Word document from link in the malspam.
TRAFFIC
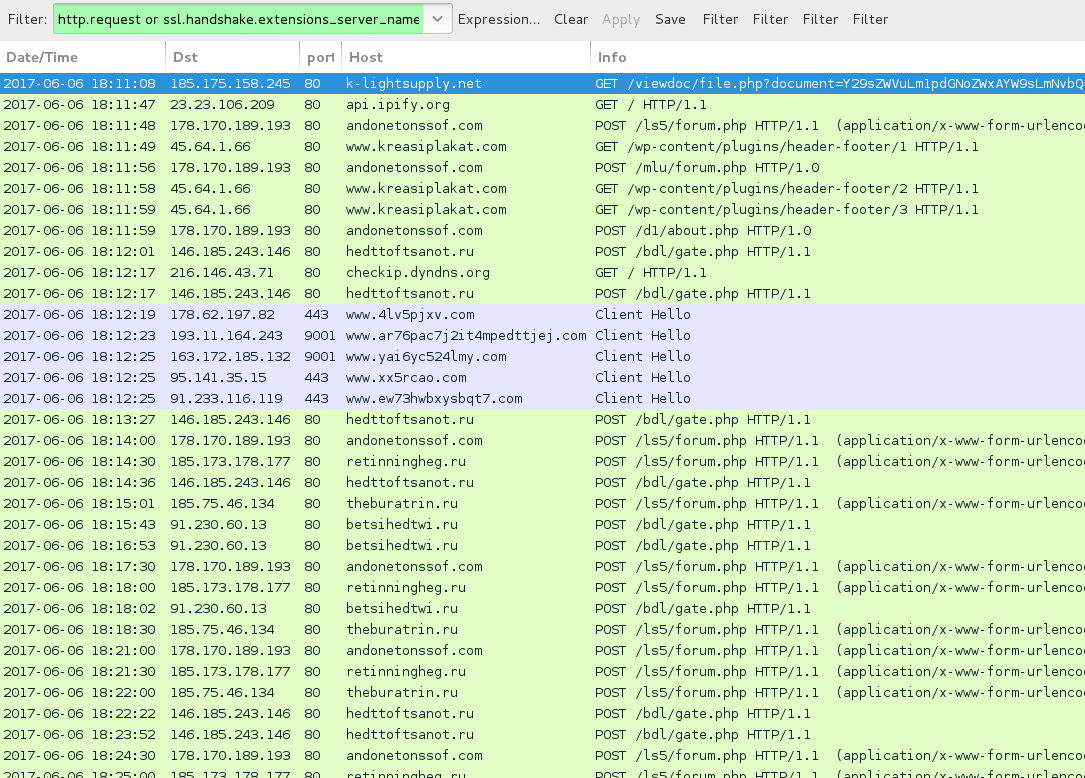
Shown above: Traffic from the infection filtered in Wireshark.
HTTP REQUESTS FOR THE WORD DOCUMENT:
- 185.175.158[.]245 port 80 - GANDSSTORE[.]CO[.]UK - GET /viewdoc/file.php?document=[base64 string]
- 185.175.158[.]245 port 80 - GILBERTANDSULLIVANSTORE[.]CO[.]UK - GET /viewdoc/file.php?document=[base64 string]
- 185.175.158[.]245 port 80 - k-lightsupply[.]net - GET /viewdoc/file.php?document=[base64 string]
- 185.175.158[.]245 port 80 - STEPFEEDERS[.]CA - GET /viewdoc/file.php?document=[base64 string]
NAME FOR THE MALICIOUS WORD DOCUMENTS:
- eFax_[recipient's email domain, minus the suffix].doc
POST-INFECTION TRAFFIC FROM MY ONE INFECTED HOST:
- 178.170.189[.]193 port 80 - andonetonssof[.]com - POST /ls5/forum.php
- 178.170.189[.]193 port 80 - andonetonssof[.]com - POST /mlu/forum.php
- 178.170.189[.]193 port 80 - andonetonssof[.]com - POST /d1/about.php
- 45.64.1[.]66 port 80 - www.kreasiplakat[.]com - GET /wp-content/plugins/header-footer/1
- 45.64.1[.]66 port 80 - www.kreasiplakat[.]com GET /wp-content/plugins/header-footer/2
- 45.64.1[.]66 port 80 - www.kreasiplakat[.]com - GET /wp-content/plugins/header-footer/3
- 91.230.60[.]13 port 80 - betsihedtwi[.]ru - POST /bdl/gate.php
- 146.185.243[.]146 port 80 - hedttoftsanot[.]ru - POST /bdl/gate.php
- 185.173.178[.]177 port 80 - retinningheg[.]ru - POST /ls5/forum.php
- 185.75.46[.]134 port 80 - theburatrin[.]ru - POST /ls5/forum.php
- api.ipify[.]org - GET /
- checkip.dyndns[.]org - GET /
- Various IP addresses on various TCP ports - Tor traffic
FILE HASHES
WORD DOCUMENT FROM LINK IN THE EMAIL:
- SHA256 hash: fba0c13176f30040d6c78bb426ddaa5dd01afc45abb9b0ada8807f408167ca97
File name: eFax_aol.doc
File size: 225,792 bytes
File description: Hancitor maldoc
MALWARE RETRIEVED FROM THE INFECTED HOST:
- SHA256 hash: d4325516998b202ee4e21e97121afd9cdc72793df052bad15cd44bfdab7e3d67
File location: C:\Users\[username]\AppData\Local\Temp\BNA208.tmp
File size: 187,904 bytes
File description: DELoader/ZLoader
Click here to return to the main page.
