2017-06-27 - HANCITOR MALSPAM (INVOICE PROBLEM)
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 22017-06-27-Hancitor-infection-with-ZLoader.pcap.zip 8.5 MB (8,531,510 bytes)
- 2017-06-27-Hancitor-infection-with-ZLoader.pcap (9,200,955 bytes)
- 2017-06-27-Hancitor-malspam-3-examples.zip 3.6 kB (3,645 bytes)
- 2017-06-27-Hancitor-malspam-1737-UTC.eml (1,551 bytes)
- 2017-06-27-Hancitor-malspam-1743-UTC.eml (1,556 bytes)
- 2017-06-27-Hancitor-malspam-1759-UTC.eml (1,544 bytes)
- 2017-06-27-malware-from-Hancitor-infection.zip 240.0 kB (240,015 bytes)
- BNEA00.tmp (188,928 bytes)
- Invoice_129383.doc (169,472 bytes)
SOME TWEETS COVERING THE 2017-06-27 WAVE OF #HANCITOR MALSPAM:
- @James_inthe_box: Incoming #hancitor; "Re: invoice
problem" links and c2 (link) - @cheapbyte: #hancitor #malspam #phishing Hancitor links June 27, 2017 huge number of links in text at Ghostbin (link)
EMAILS
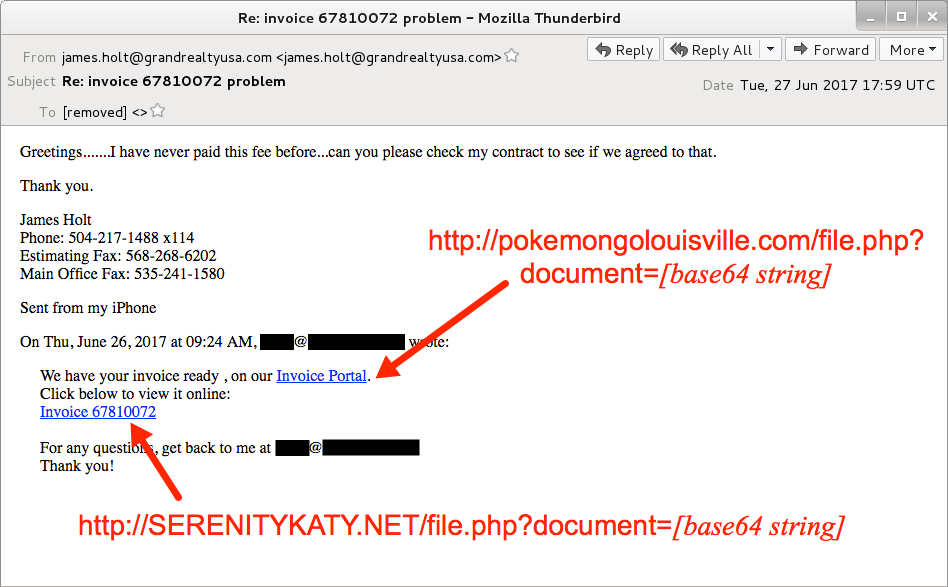
Shown above: Screenshot from one of the emails.
EMAIL HEADERS:
- Date: Tuesday 2017-06-27 as early as 17:37 UTC through at least 17:59 UTC
- From: "james.holt@grandrealtyusa[.]com" <james.holt@grandrealtyusa[.]com>
- Subject: Re: invoice 67810072 problem
- Subject: Re: invoice 67810072 problem
- Subject: Re: invoice 67810072 problem
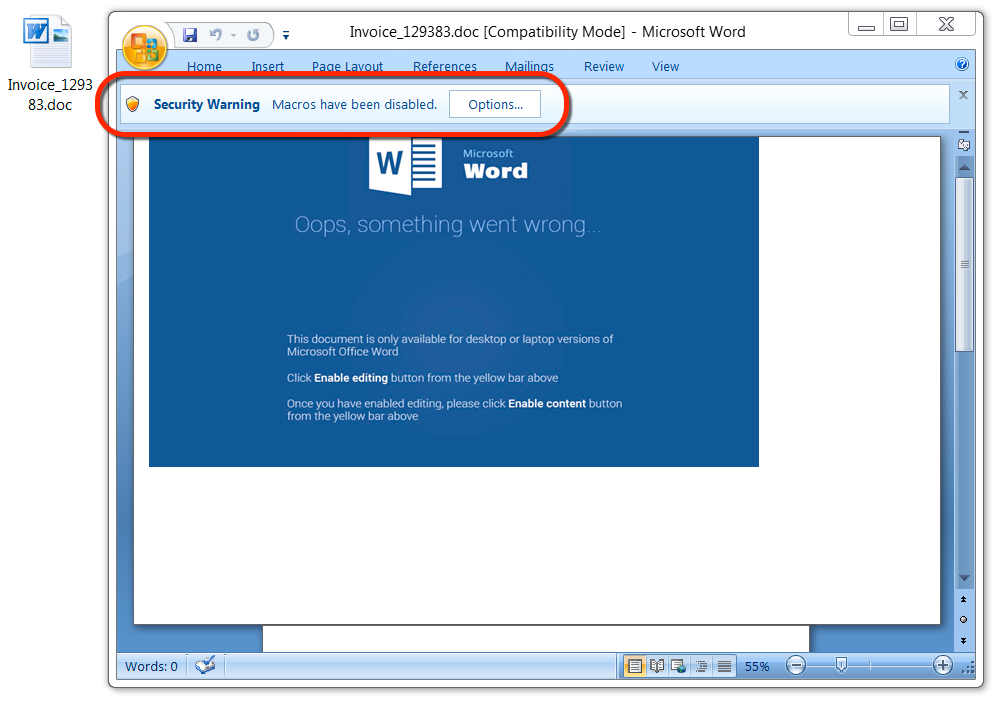
Shown above: Malicious Word document from link in the malspam.
TRAFFIC
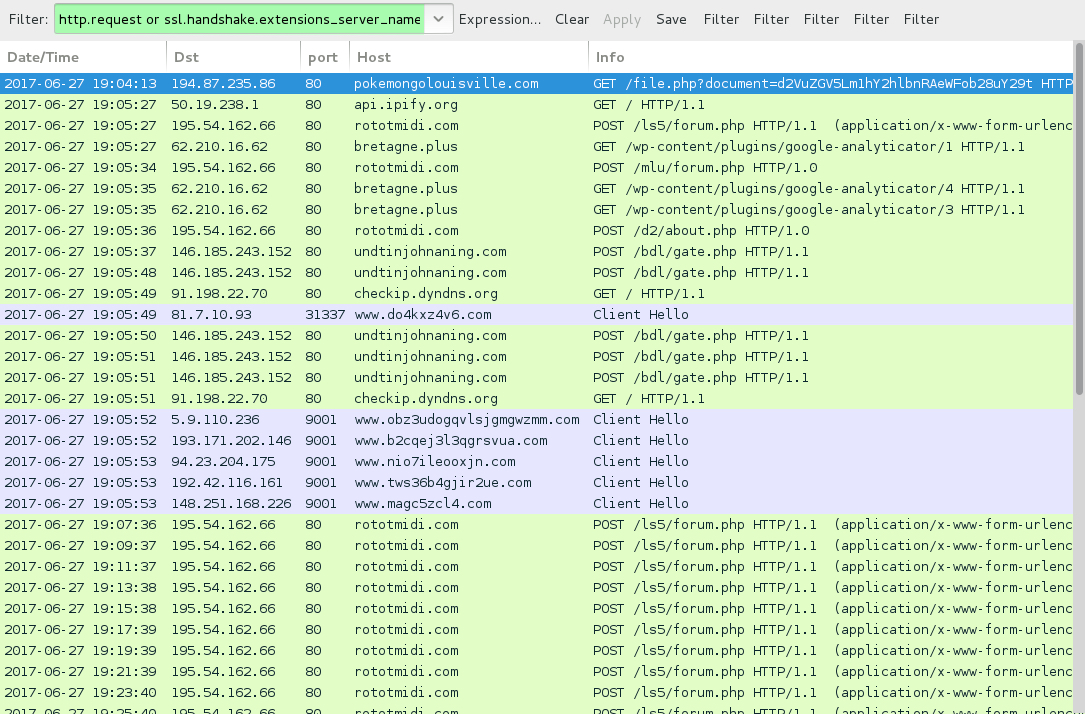
Shown above: Traffic from the infection filtered in Wireshark.
HTTP REQUESTS FOR THE WORD DOCUMENT:
- 2015FORDMUSTANGPARTS[.]COM - GET /viewdoc/file.php?document=[base64 string]
- akrapovicexhaustsystems[.]com - GET /viewdoc/file.php?document=[base64 string]
- pokemongoboulder[.]com - GET /viewdoc/file.php?document=[base64 string]
- SERENITYKATY[.]NET - GET /viewdoc/file.php?document=[base64 string]
NAME FOR THE MALICIOUS WORD DOCUMENTS:
- Invoice_[six-digit number].doc
POST-INFECTION TRAFFIC FROM MY ONE INFECTED HOST:
- 195.54.162[.]66 port 80 - rototmidi[.]com - POST /ls5/forum.php
- 195.54.162[.]66 port 80 - rototmidi[.]com - POST /mlu/forum.php
- 195.54.162[.]66 port 80 - rototmidi[.]com - POST /d2/about.php
- 62.210.16[.]62 port 80 - bretagne[.]plus - GET /wp-content/plugins/google-analyticator/1
- 62.210.16[.]62 port 80 - bretagne[.]plus - GET /wp-content/plugins/google-analyticator/4
- 62.210.16[.]62 port 80 - bretagne[.]plus - GET /wp-content/plugins/google-analyticator/3
- 146.185.243[.]152 port 80 - undtinjohnaning[.]com - POST /bdl/gate.php
- api.ipify[.]org - GET /
- checkip.dyndns[.]org - GET /
- Various IP addresses on various TCP ports - Tor traffic
FILE HASHES
WORD DOCUMENT FROM LINK IN THE EMAIL:
- SHA256 hash: e9f8b7b9faa8a61257c42ecec480c1a0b8855e7514122c7060c89f4ced2d592b
File name: Invoice_129383.doc
File size: 169,472 bytes
File description: Hancitor maldoc
MALWARE RETRIEVED FROM THE INFECTED HOST:
- SHA256 hash: e14982a13558812873982069243872ca703c9a3e21e7e9b31ff3e0062e368b68
File location: C:\Users\[username]\AppData\Local\Temp\BNEA00.tmp
File size: 188,928 bytes
File description: DELoader/ZLoader
Click here to return to the main page.
