2017-08-02 - HANCITOR INFECTION
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-08-02-Hancitor-infection-traffic.pcap.zip 327.6 kB (327,560 bytes)
- 2017-08-02-Hancitor-infection-traffic.pcap (512,864 bytes)
- 2017-08-02-Hancitor-malspam-3-examples.zip 4.1 kB (4,060 bytes)
- 2017-08-02-Hancitor-malspam-145839-UTC.eml (1,998 bytes)
- 2017-08-02-Hancitor-malspam-171842-UTC.eml (1,997 bytes)
- 2017-08-02-Hancitor-malspam-181153-UTC.eml (2,002 bytes)
- 2017-08-02-malware-from-Hancitor-infection.zip 254.6 kB (254,627 bytes)
- ADP_Invoice_989046.doc (241,664 bytes)
- BN2F78.tmp (210,432 bytes)
TODAY'S TWEETS COVERING THE 2017-08-02 WAVE OF #HANCITOR MALSPAM:
- @cheapbyte: And #hancitor #malspam #phishing Hancitor Fake ADP email August 2, 2017 URLs in text at Ghostbin (link)
- @James_inthe_box: New #hancitor run: "ADP Payroll Invoice <digits>" (link)
EMAILS
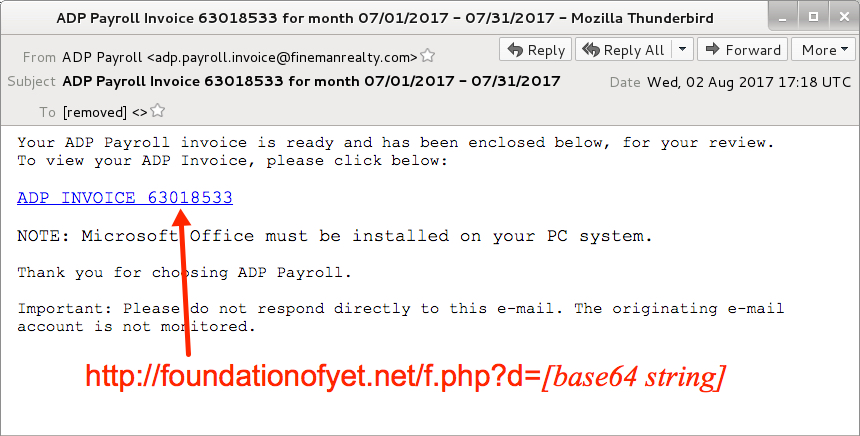
Shown above: Screenshot from one of the emails.
EMAIL HEADERS:
- Date: Wednesday 2017-08-02 as early as 14:58 UTC through at least 18:11 UTC
- From: "ADP Payroll" <adp.payroll.invoice@finemanrealty[.]com>
- Subject: ADP Payroll Invoice 58343861 for month 07/01/2017 - 07/31/2017
- Subject: ADP Payroll Invoice 63018533 for month 07/01/2017 - 07/31/2017
- Subject: ADP Payroll Invoice 78036003 for month 07/01/2017 - 07/31/2017
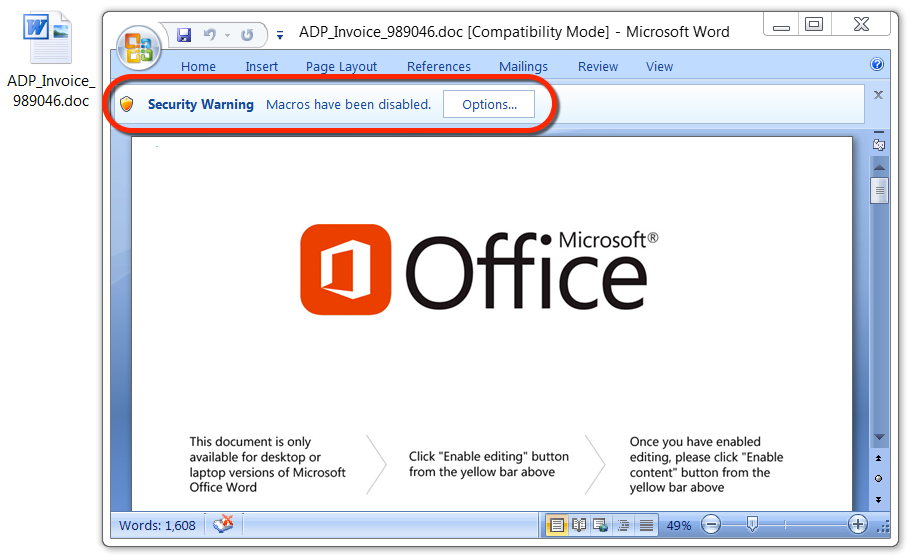
Shown above: Malicious Word document from link in the malspam.
TRAFFIC
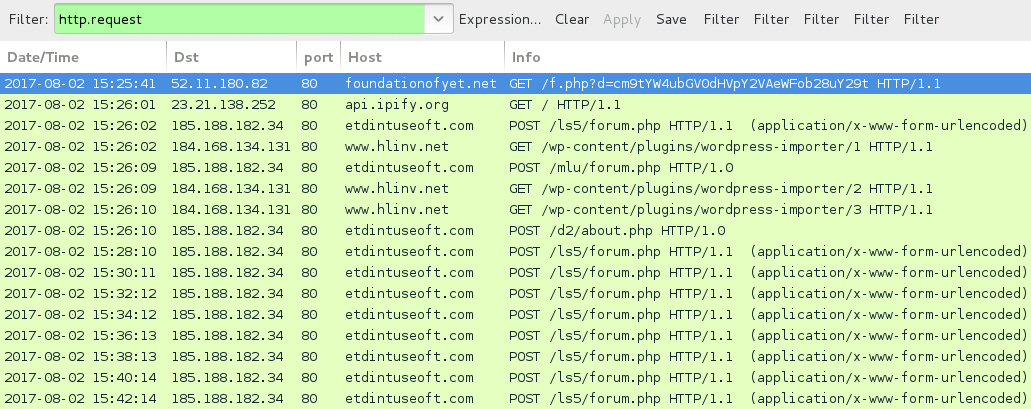
Shown above: Traffic from the infection filtered in Wireshark.
LINKS IN THE EMAILS THE WORD DOCUMENT:
- foundationofyet[.]net - GET /f.php?d=[base64 string]
- thefamilymoneyfarm[.]com - GET /f.php?d=[base64 string]
NAME FOR THE MALICIOUS WORD DOCUMENT:
- ADP_Invoice_[six random digits].doc
POST-INFECTION TRAFFIC FROM MY INFECTED HOST:
- 185.188.182[.]34 port 80 - etdintuseoft[.]com - POST /ls5/forum.php
- 185.188.182[.]34 port 80 - etdintuseoft[.]com - POST /mlu/forum.php
- 185.188.182[.]34 port 80 - etdintuseoft[.]com - POST /d2/about.php
- 184.168.134[.]131 port 80 - www.hlinv[.]net - GET /wp-content/plugins/wordpress-importer/1
- 184.168.134[.]131 port 80 - www.hlinv[.]net - GET /wp-content/plugins/wordpress-importer/2
- 184.168.134[.]131 port 80 - www.hlinv[.]net - GET /wp-content/plugins/wordpress-importer/3
- api.ipify[.]org - GET /
- DNS query for toflingtinjo[.]ru - Response: No such name
- DNS query for ersrofsafah[.]ru - Response: No such name
FILE HASHES
WORD DOCUMENT FROM LINK IN THE EMAIL:
- SHA256 hash: 0858582ca7d96c7d588cd83f2ef4cb94fcef2e6f70fdb0d022dbceb63a1c9ccc
File name: ADP_Invoice_989046.doc
File size: 241,664 bytes
File description: Hancitor maldoc
MALWARE RETRIEVED FROM THE INFECTED HOST:
- SHA256 hash: deb540755cc2fe423d6eabf4177778720ae01caf6c5973ffc24f7dec111fceba
File location: C:\Users\[username]\AppData\Local\Temp\BN2F78.tmp
File size: 210,432 bytes
File description: DELoader/ZLoader
Click here to return to the main page.
