2018-04-02 - QUICK POST: NECURS BOTNET MALSPAM PUSHES QUANTLOADER AND FOLLOW-UP MALWARE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- Zip archive of the malspam tracker: 2018-04-02-Necurs-Botnet-malspam-tracker-10-examples.csv.zip 1.1 kB (1,114 bytes)
- Zip archive of the infection traffic: 2018-04-02-two-pcaps-of-Necurs-Botnet-malspam-infection-traffic.zip 1.4 MB (1,434,746 bytes)
- Zip archive of the associated emails, malware, and artifacts: 2018-04-02-Necurs-Botnet-emails-malware-and-artifacts.zip 1.8 MB (1,794,700 bytes)
NOTES:
- Emails had the wrong encoding in the email files for the attachments (should've been base64 but was listed as: quoted-printable).
- I fixed that in the emails I collected for today's malware archive.
- Infection chain: 7z attachment --> extracted .url file --> .js file over SMB --> QuantLoader via HTTP --> follow-up malware via HTTP
- In my first run, the follow-up malware might be Evil Ammyy (Twitter thread).
- Later in the day during my second try, I saw GlobeImposter ransomware as the follow-up malware.
- I collected 80 .js files from the server at 169.239.128[.]144, and I've included them in today's malware archive.
IMAGES
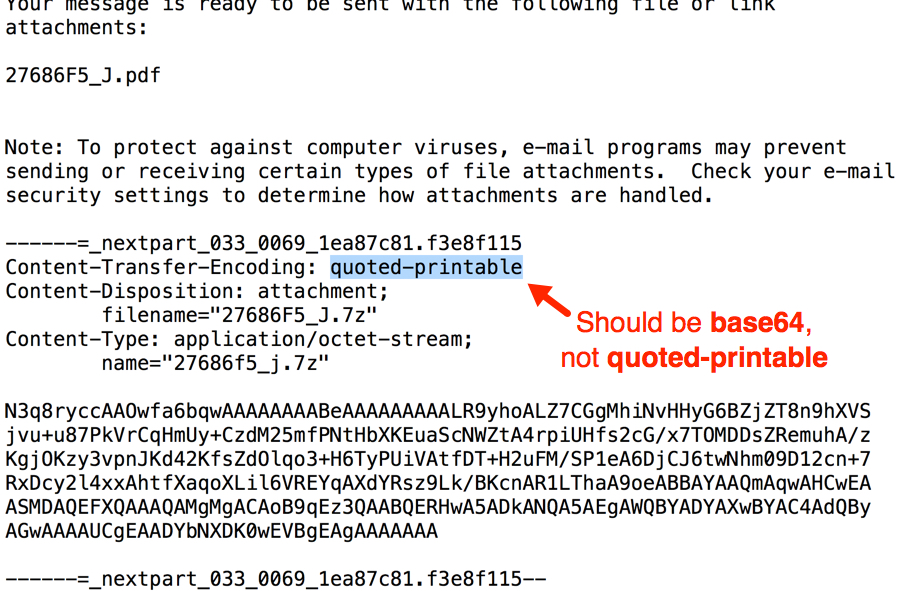
Shown above: Format error seen in emails from this wave of malspam.
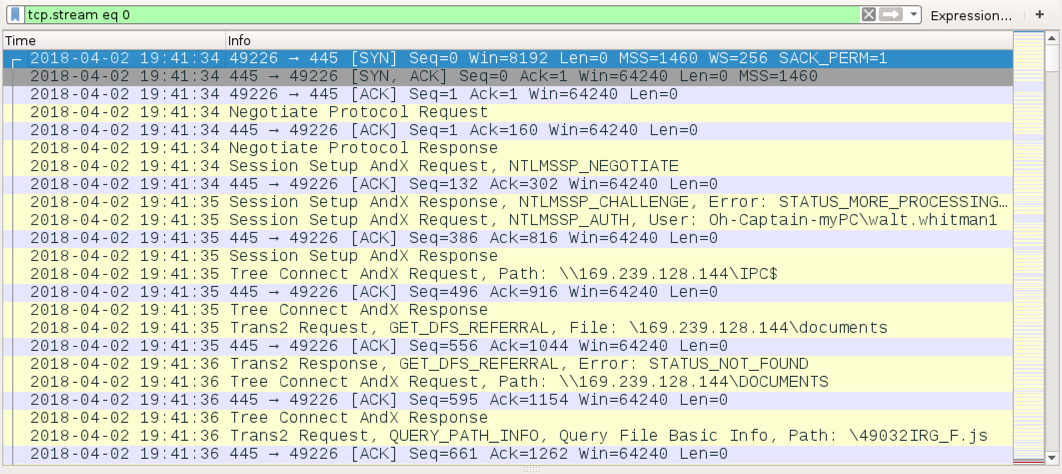
Shown above: SMB traffic from the extracted .url file to retrieve a .js file (filtered in Wireshark).
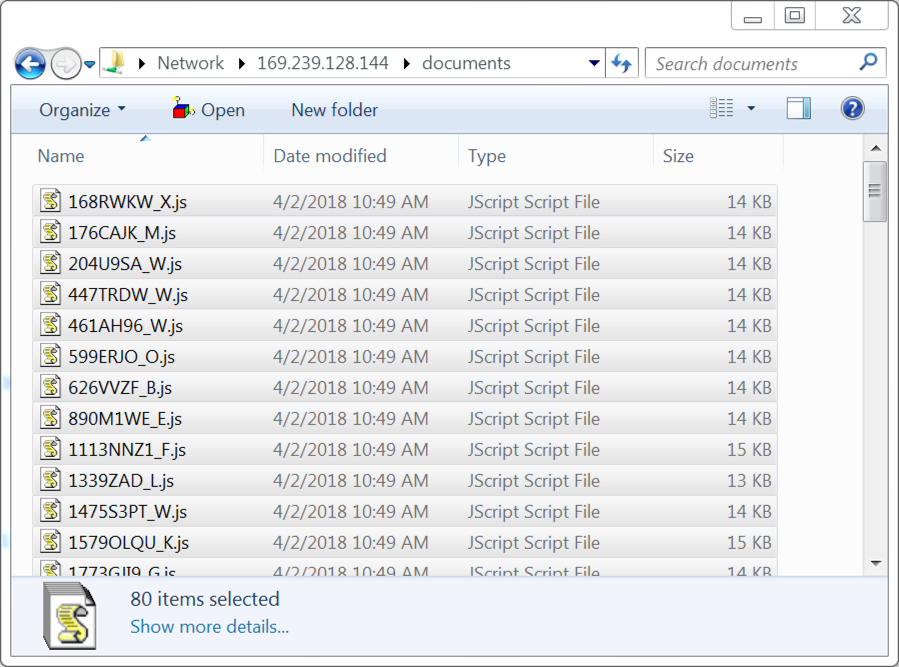
Shown above: Saw 80 .js files from that server over SMB.
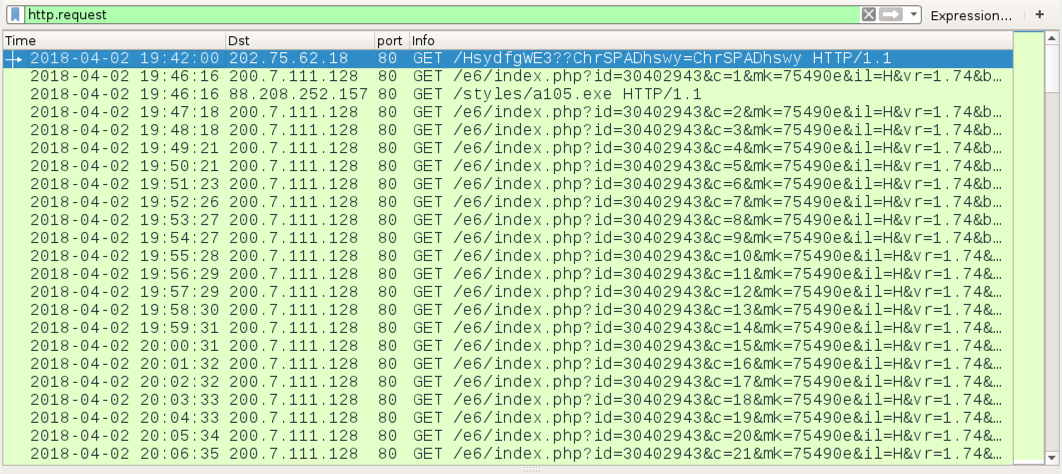
Shown above: Traffic from my second infection filtered in Wireshark (just the HTTP requests).
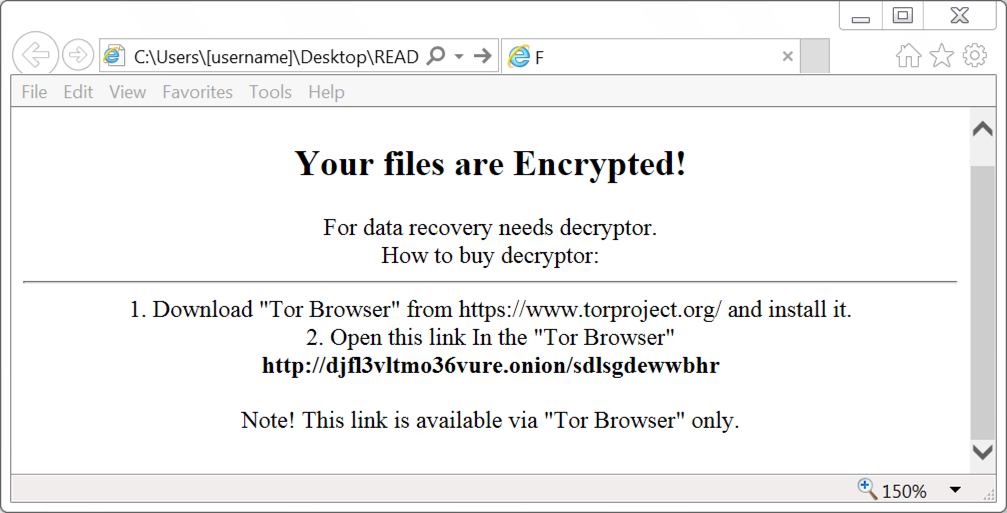
Shown above: GlobeImposter ransomware from my second infection attempt.
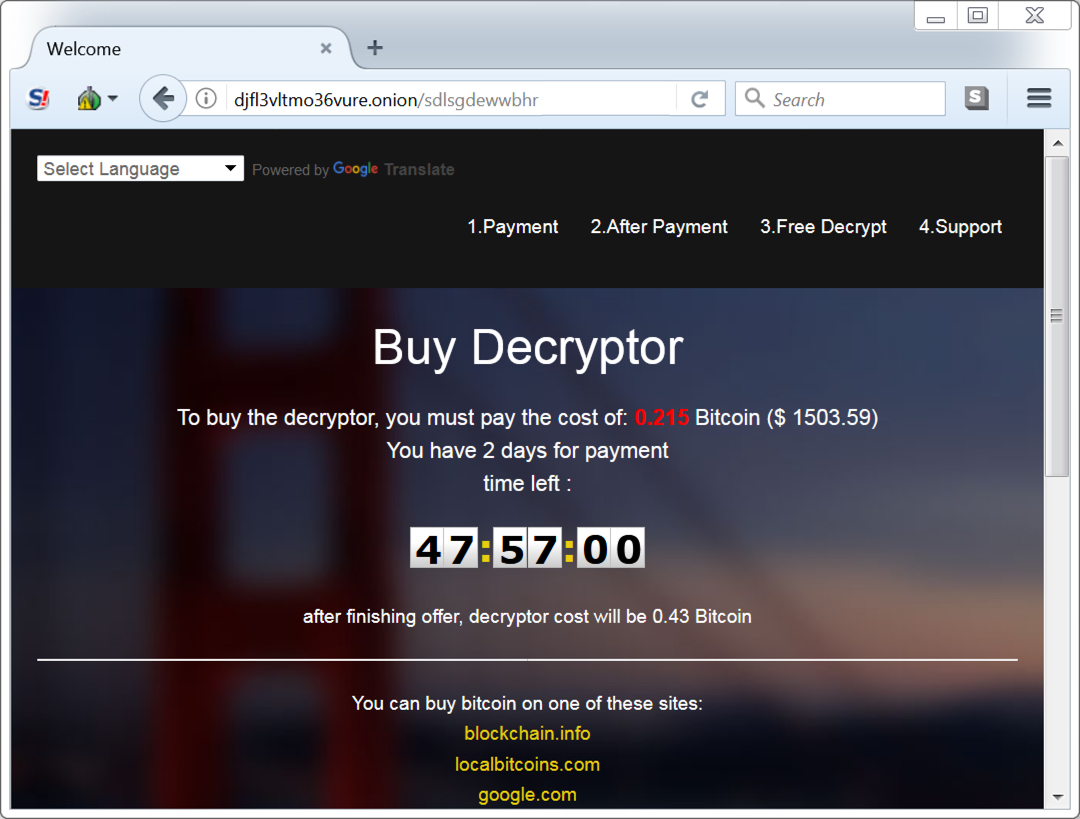
Shown above: GlobeImposter decryptor.
Click here to return to the main page.
