2021-12-10 (FRIDAY) - TA551 (SHATHAK) ICEDID (BOKBOT) WITH BACKCONNECT, COBALT STRIKE AND ANUBIS VNC
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
NOTES:
- In the reference below, I mistakenly reported the BackConnect and Anubis VNC traffic as "DarkVNC" for @Unit42_Intel.
- I've fixed this blog post and the material to show the correct activity.
- For more on Backconnect, see: https://www.netresec.com/?page=Blog&month=2022-10&post=IcedID-BackConnect-Protocol
- For more on Anubis VNC, see: https://blog.nviso.eu/2023/03/20/icedids-vnc-backdoors-dark-cat-anubis-keyhole/
REFERENCE:
ASSOCIATED FILES:
- 2021-12-10-IOCs-for-TA551-IcedID-infection.txt.zip 2.0 kB (2,041 bytes)
- 2021-12-10-TA551-malspam-example.eml.zip 55.2 kB (55,173 bytes)
- 2021-12-10-TA551-IcedID-with-Cobalt-Strike-and-BackConnect-and-Anubis-VNC.pcap.zip 13.9 MB (13,932,558 bytes)
- 2021-12-10-TA551-IcedID-malware-and-artifacts.zip 1.1 MB (1,108,713 bytes)
IMAGES
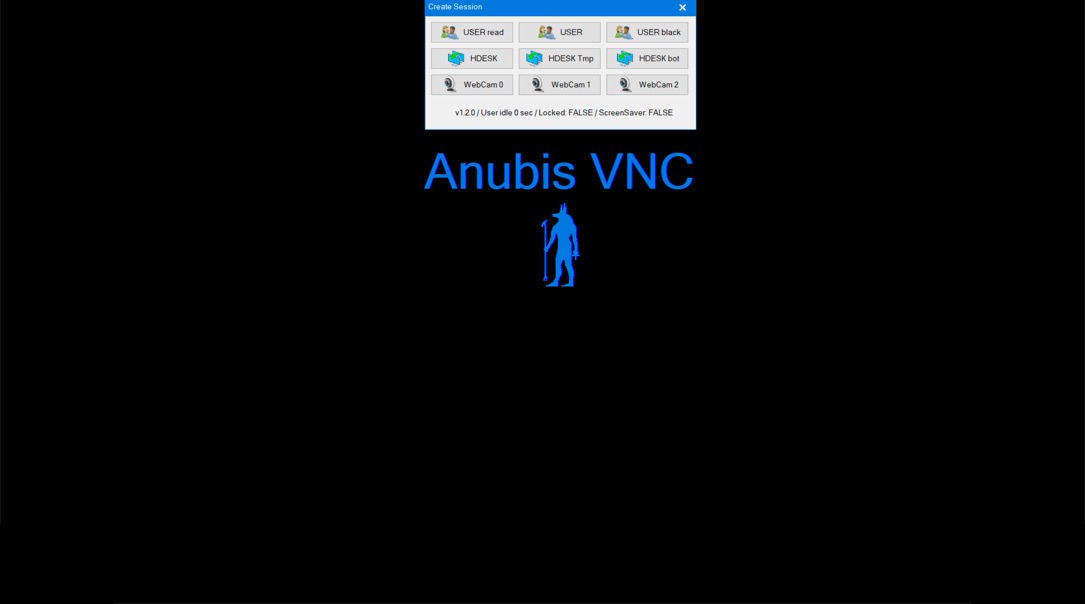
Shown above: Screenshot of video from the decoded VNC traffic.
Click here to return to the main page.
