30 DAYS OF FORMBOOK: DAY 18, THURSDAY 2023-06-22 - "K2L0"
NOTICE:
- Of note, the zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
NOTES:
- This the is my 18th of 30 infection runs for recent Formbook activity.
ASSOCIATED FILES:
- 2023-06-22-IOCs-for-Formbook-infection.txt.zip 1.9 kB (1,859 bytes)
- 2023-06-22-Formbook-infection-traffic.pcap.zip 3.5 MB (3,542,531 bytes)
- 2023-06-22-Formbook-malware-and-artifacts.zip 338 kB (337,611 bytes)
IMAGES
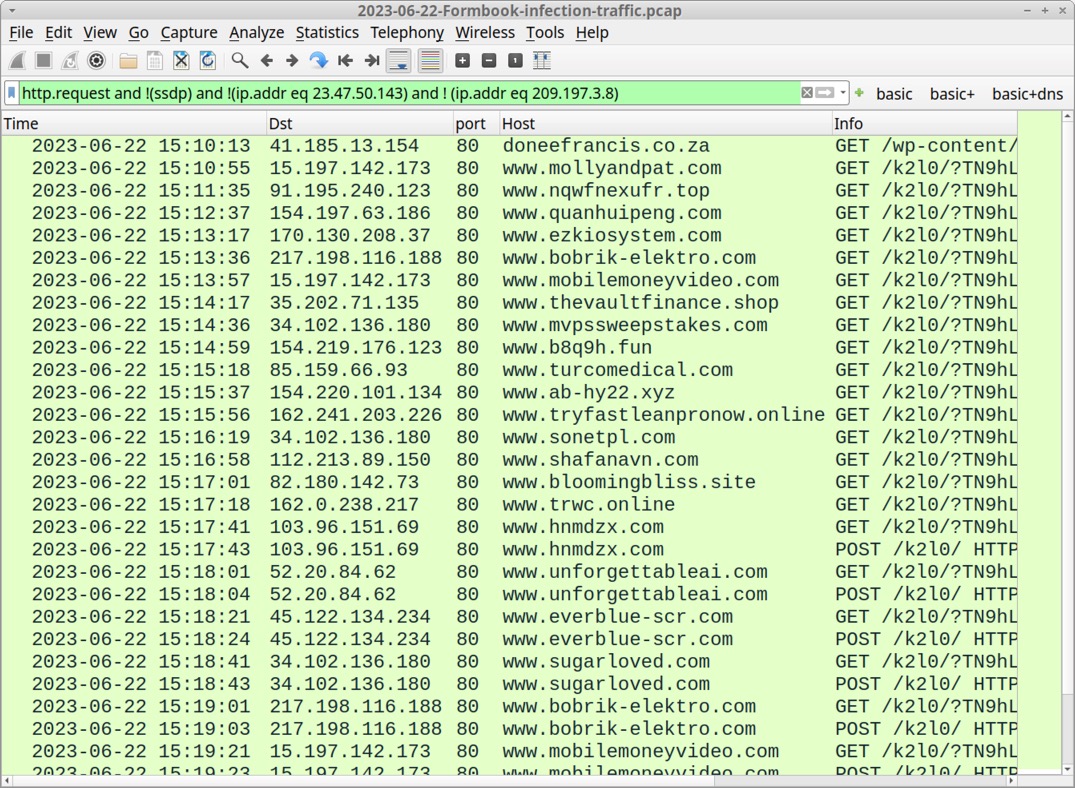
Shown above: Traffic from the infection filtered in Wireshark.
30 DAYS OF FORMBOOK: DAY 18, THURSDAY 2023-06-22 - "K2L0" INFECTION CHAIN: - Email --> RTF attachment (.doc extension) --> CVE-2017-11882 exploit --> URL for Formbook EXE --> run EXE --> Formbook C2 MALWARE/ARTIFACTS: - SHA256 hash: 600e9328c592417bfa986a5a2f7aca7503dcfde78d962d1e289bde8f890c1aae - File size: 4,414 bytes - File name: PR #1112100911.doc - File type: Rich Text Format data, version 1 - File description: RTF with .doc file extension, exploits CVE-2017-11882 to download the Formbook EXE below - SHA256 hash: 52e00713c3960978ca02db6caa0862f6f304388f05a1ee33203f20e5533b1789 - File size: 372,850 bytes - File downloaded from: hxxp[:]//doneefrancis[.]co[.]za/wp-content/plugins/seoplugins/formaneok3.1.exe - Persistent file location: C:\Program Files (x86)\Odfylp\mrwt88mxw0h8dp.exe - File type: PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive - File description: Windows EXE for Formbook version 4.1 PERSISTENCE: - Windows Registry key: HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run - Value name: UR_XNHA82T - Value type: REG_SZ - Value Data: C:\Program Files (x86)\Odfylp\mrwt88mxw0h8dp.exe DATA STORED FOR EXFILTRATION TO FORMBOOK C2 SERVER: - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlog.ini - 0 bytes - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlogim.jpeg (screenshot of desktop) - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlogrc.ini (Outlook Recovery) - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlogrf.ini (Firefox Recovery) - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlogrg.ini (Chrome Recovery) - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlogri.ini (Iexplore Recovery) - C:\Users\[username]\AppData\Roaming\-QR70-TT\-QRlogrv.ini (__Vault Recovery) - Note: All the above files were deleted after data exfiltation, except for first file at 0 bytes. FORMBOOK HTTP GET AND POST REQUESTS: - GET /k2l0/?[string of alphanumeric characters with the following mixed in: = _ + and /] - POST /k2l0/ DOMAINS THAT DID NOT RESOLVE: - DNS query for www.1ywab[.]com - no response from DNS server - DNS query for www.aldimerencasa[.]com - no response from DNS server - DNS query for www.adhika[.]online - response: No such name - DNS query for www.atsttoneworks[.]com - response: No such name - DNS query for www.capitalrepros[.]com - response: No such name DOMAINS USED FOR FORMBOOK GET REQUESTS: - Note: These appear to be legitimate websites or parked domain pages. - www.1xboro7[.]click - www.amenallelulia[.]com - www.bloomingbliss[.]site - www.brawnyemail[.]site - www.cetmetalprefabrik[.]com - www.colineverall[.]com - www.ezkiosystem[.]com - www.lunggear[.]com - www.quanhuipeng[.]com - www.sanctuary-for-the-arts[.]com - www.scopegaming[.]com - www.scripturewraps[.]com - www.shafanavn[.]com - www.sonetpl[.]com - www.tameniee[.]xyz - www.usdrub[.]com - www.worldassestsledger[.]com - www.youonpurpose[.]coach DOMAINS USED FOR FORMBOOK GET AND POST REQUESTS: - Note: These appear to be legitimate websites or parked domain pages. - www.32qtp[.]live - www.ab-hy22[.]xyz - www.b8q9h[.]fun - www.bobrik-elektro[.]com - www.everblue-scr[.]com - www.getflooringservices[.]today - www.hnmdzx[.]com - www.mobilemoneyvideo[.]com - www.mollyandpat[.]com - www.mvpssweepstakes[.]com - www.nqwfnexufr[.]top - www.sugarloved[.]com - www.thaomocquysonla[.]click - www.thevaultfinance[.]shop - www.trwc[.]online - www.tryfastleanpronow[.]online - www.turcomedical[.]com - www.unforgettableai[.]com - www.zhujiangceramics[.]com
Click here to return to the main page.
